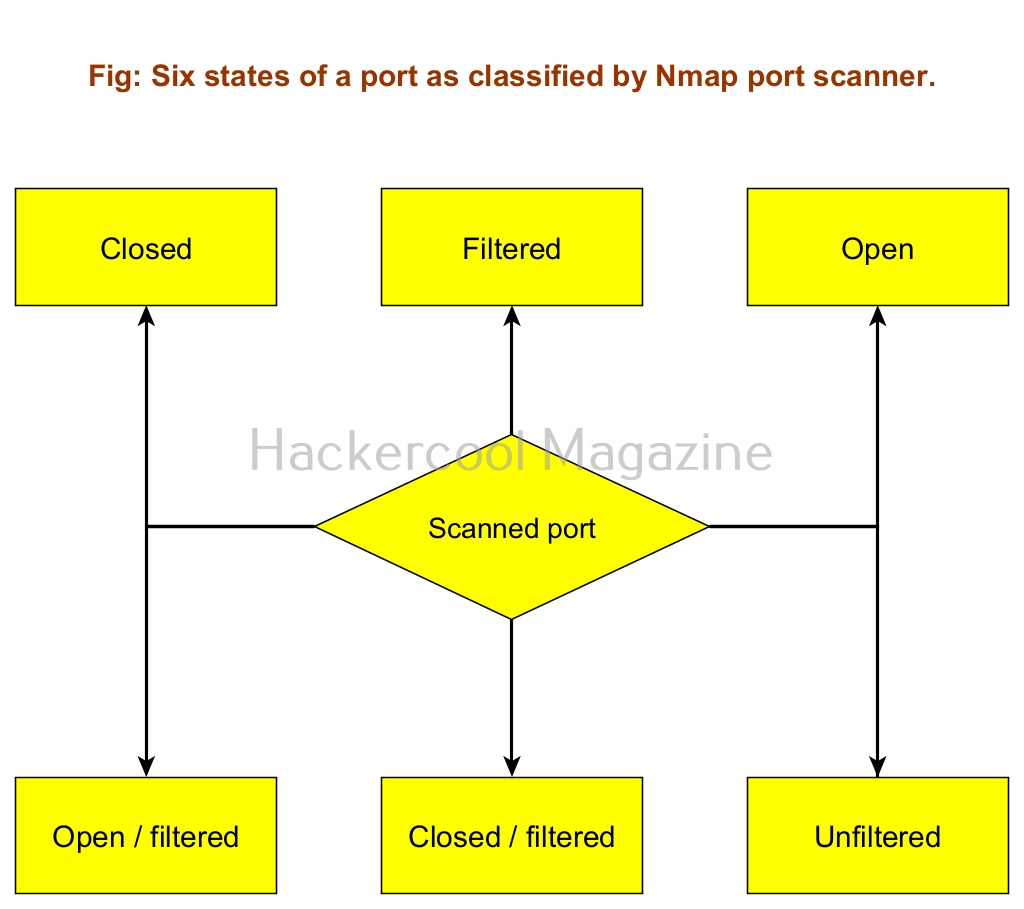
Hello aspiring Ethical Hackers. In this blogpost you will learn how to analyze port scanning results of Nmap. Scanning plays a very important role in hacking a system. Scanning is a phase in which we find out the ports which are open and the services listening on those ports. NMap is the most popular port scanner being used security guys nowadays. Read complete guide to Nmap. It is very important to understand results of Nmap port scan. Nmap classifies ports into six states. They are, open, closed, filtered, unfiltered, open | filtered and closed | filtered.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
Let us find out when Nmap classifies ports into specific states. To demonstrate the results of port scanning performed my Nmap, I use two virtual machines,
1. Kali Linux as attacker system.
2. Windows 10 as target system.
On the target system, I enable or install a SSH server. You can learn how to install a SSH server here. For this tutorial, I will be scanning this SSH port with Nmap.
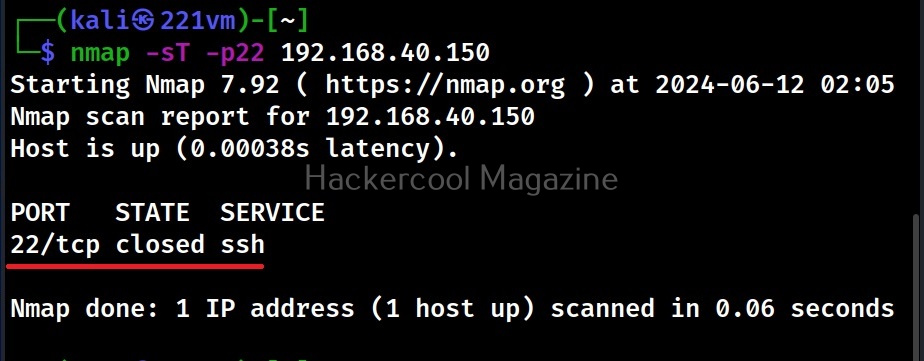
1. Closed:
Nmap classifies a port as closed when the port is accessible but there is no application listening on it. When I perform a default Nmap scan from the Kali system of port 22 of the target machine, I get a “closed” result as shown below.
nmap -sT –p22 <target ip>
Note that on our target machine, we have installed the SSH server but not yet started it.
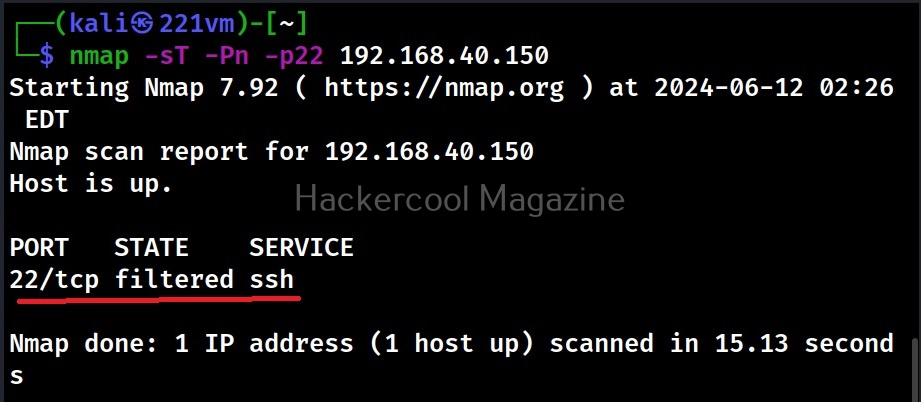
2. Filtered:
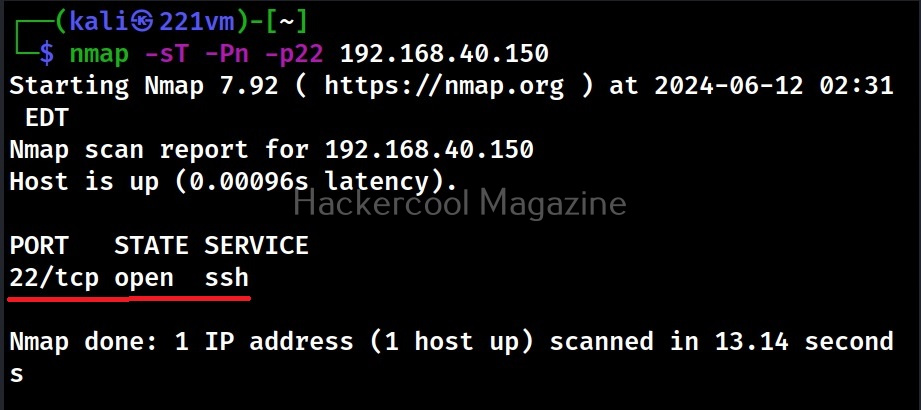
Nmap classifies a port as filtered when it can’t determine whether the port is open or closed because packet filtering prevents its probes from reaching the port. Let’s now start the SSH server and scan again. This time when we scan the same port again, we get a “filtered” result as shown below.
nmap -sT -Pn –p22 <target ip>
This is because although we have started the SSH service on the target system, Windows Defender Firewall, which is turned ON by default, is blocking our connection to the target port. When Nmap classifies a port as filtered, it is most likely that a firewall is blocking our probes.
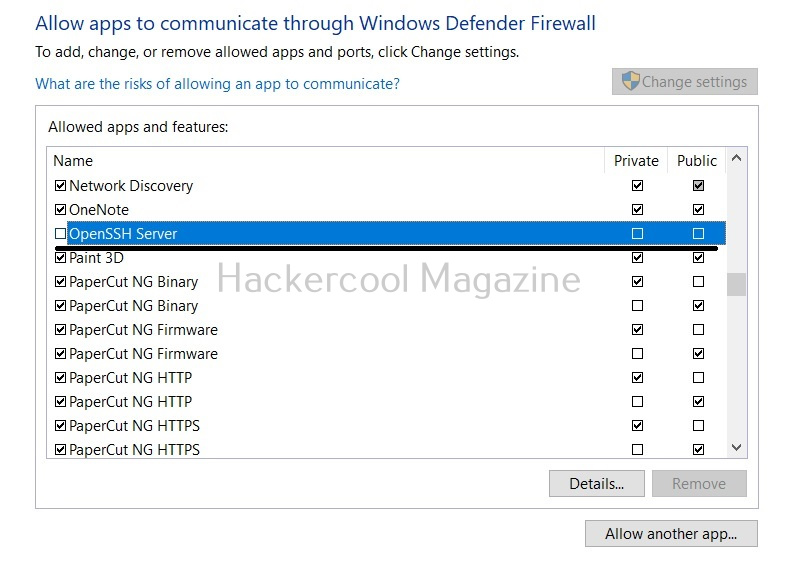
3. Open:
Nmap classifies a port as open when the port is accessible and if an application is actively accepting TCP connections, UDP datagrams or SCTP associations on this port. On our target system, let’s change the Windows Defender Firewall settings to allow the SSH service through the Firewall as shown below and scan the service again.
The result I get is “open”. This is because the SSH server is actively accepting connections.
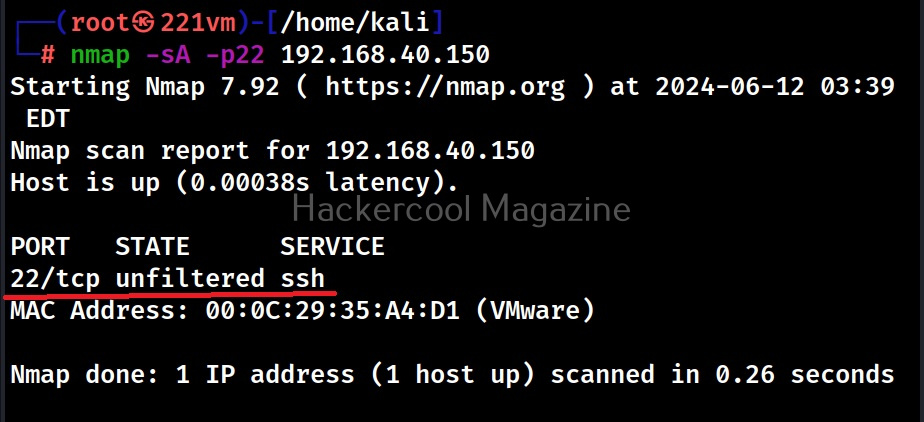
4. Unfiltered:
Nmap classifies a port as unfiltered when a port is accessible but it can’t determine whether it is open or closed. A port is classified as unfiltered only with the ACK scan. Learn about different scans that can be performed with Nmap.
nmap -sA –p22 <target ip>
This scan cannot determine if the port is open or closed and is generally used to find out rules of the firewall.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
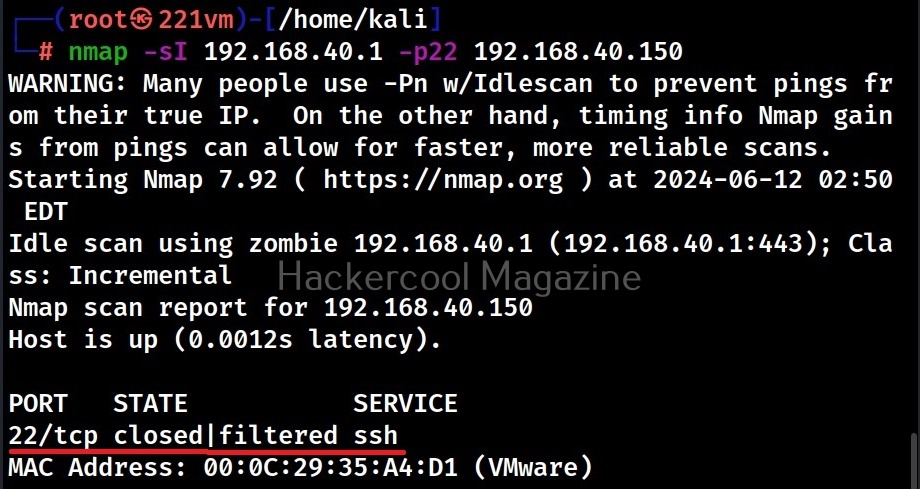
5. Closed | filtered:
Nmap gives this result when it can’t find out whether a port is closed or filtered. A port is classified this way by Nmap only when we perform IDLE scan. Now what is IDLE scan? Idle scan is a scan in which we use a zombie host to scan the victim. In our example, we use another host with IP 192.168.40.1 as a zombie to perform IDLE scan on our victim.
nmap -sI <zombie_host> -p22 <target ip>
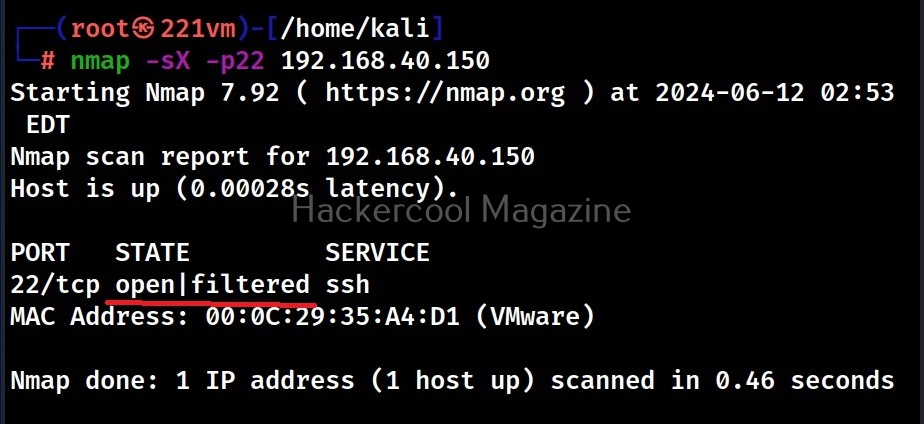
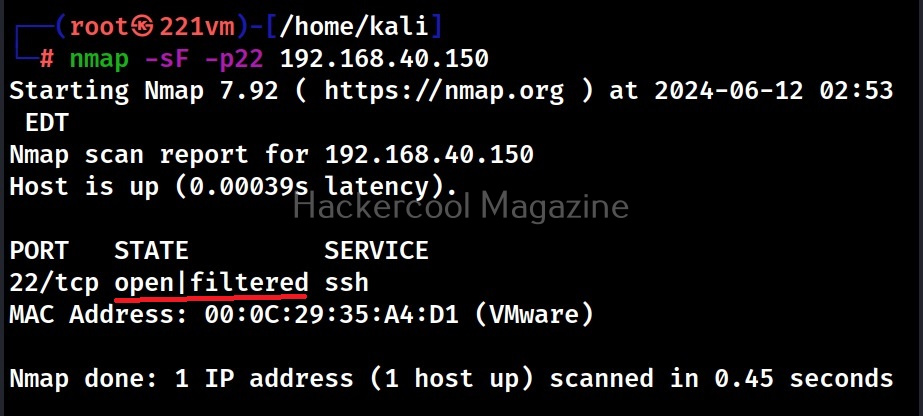
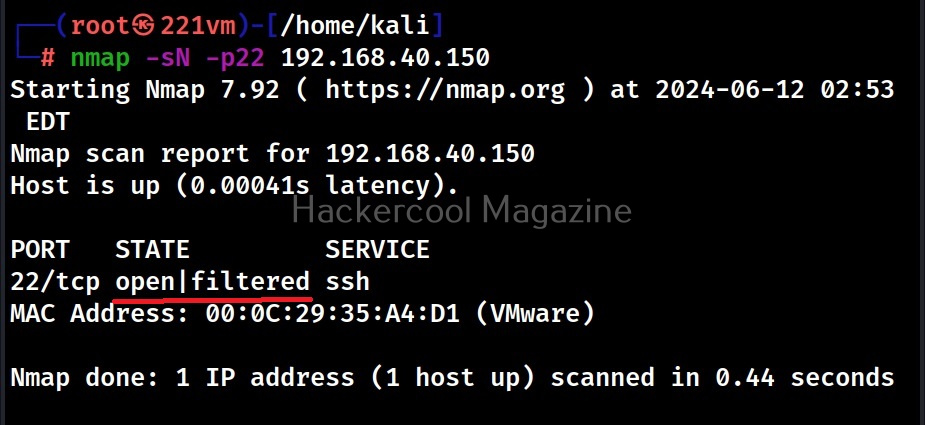
6. Open | filtered:
A port is classified as open | filtered when Nmap is unable to determine whether a port is open or filtered. This happens for scan types in which open ports give no response. The UDP, IP protocol, FIN, NULL and XMAS scans classify ports this way.
The port is classified as “open | filtered” in above cases because Nmap can’t determine whether the port is open or filtered.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply