Kali Linux is the most popular and also my favorite pen testing distro. Its regular updates and stability accord it the top spot. Apart from Kali Linux, there are many other pen testing distros available. One of them is Parrot Security distro. Parrot Security sports many more tools than Kali Linux which includes software for cryptography, cloud, anonymity, digital forensics and of course programming. One of our readers has requested us to make a guide on how to install Parrot Security OS in Vmware. So be it.
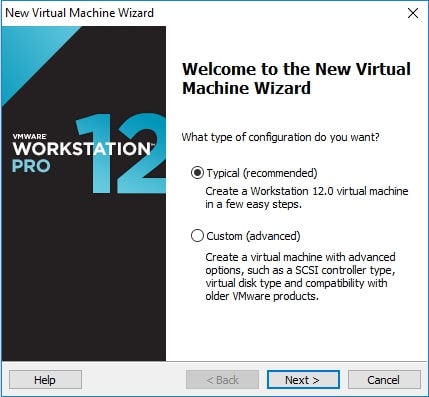
Download the Parrot Security OS . Unlike the makers of Kali Linux, Parrot Security have not yet provided a Vmware image to download. So we have to download a iso image (depending on your architecture yo- u can download a 32bit or 64 bit iso file). Once the download is finished, open Vmware Workstation (Version 12 used for this article). Hit “CTRL+N”. The below window should open.
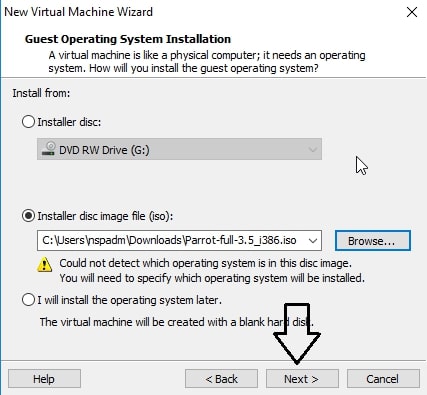
Make sure the “Typical” option is selected, and click on “Next”. That takes us to the next window. Initially, the “installer disc image file” field should be empty. Click on “browse” and browse to location of the iso file we just downloaded and select it. Now the window should look like below. Click on “Next”.
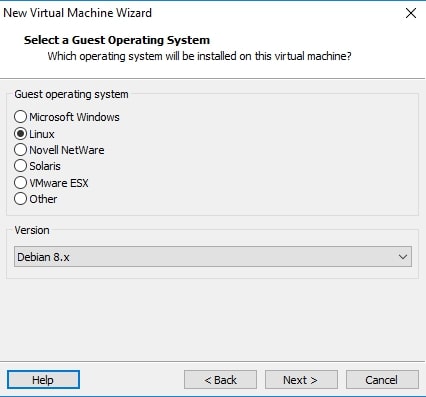
The Guest operating system should be automatically selected for you, if not select Linux as OS and version as Debian 8.x (since I am installing a 32bit, make it Debian 8.x64 if installing 64bit). Click on Next.
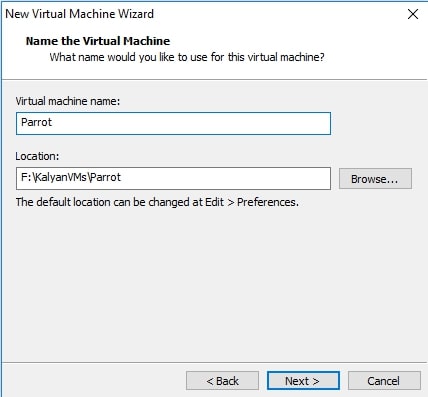
Choose the name of virtual machine and its location as you like. I named it Parrot. Click on “Next”.
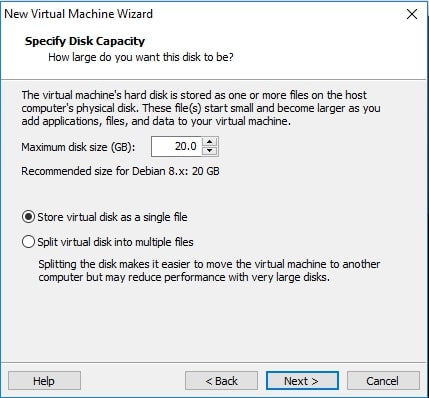
Allocate the hard disk memory for your virtual machine. Keep the minimum as 20GB. Click on Finish.
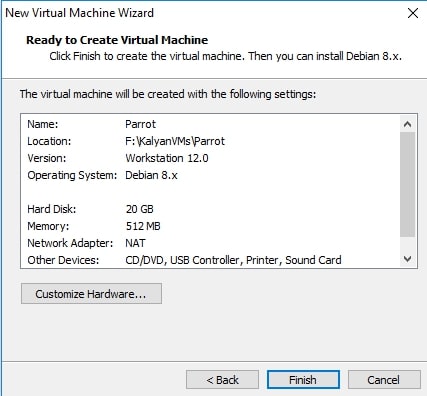
It will show you a summary of all the selections you made. If you want to make any changes, click on Customize hardware or else click on Next.
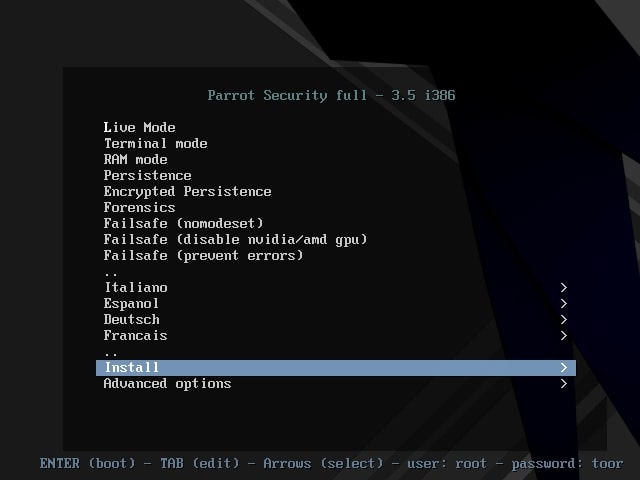
The virtual machine is created with the name you gave it. Power on the virtual machine. It will boot and take you to the interface shown below. Choose the “Install” option. In the next window select “Standard Installer”. You can select these options using “tab” button.
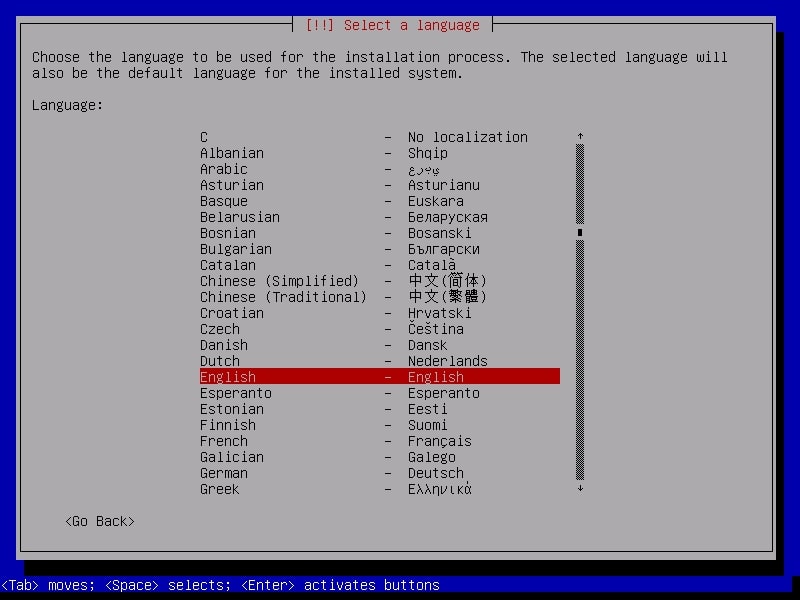
Select the language in which you want to continue the installation process.
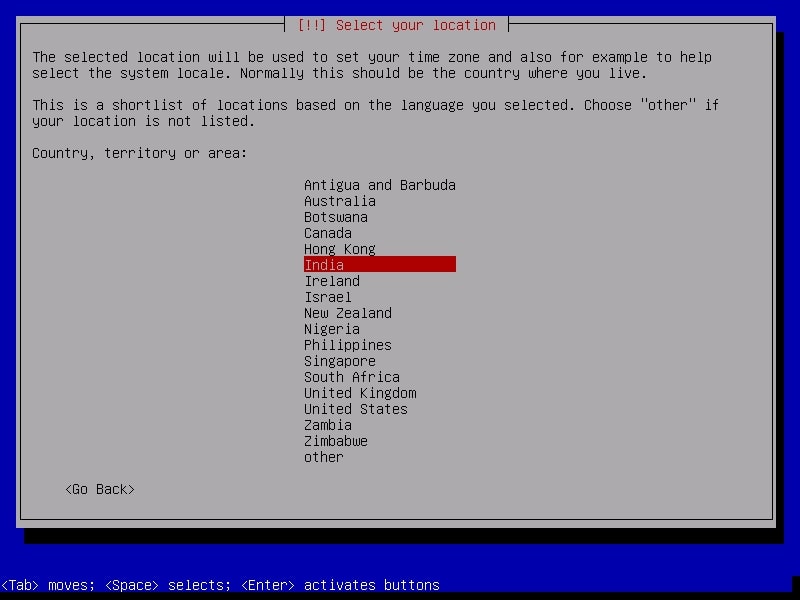
Select your country. For this article, I chose location as India.
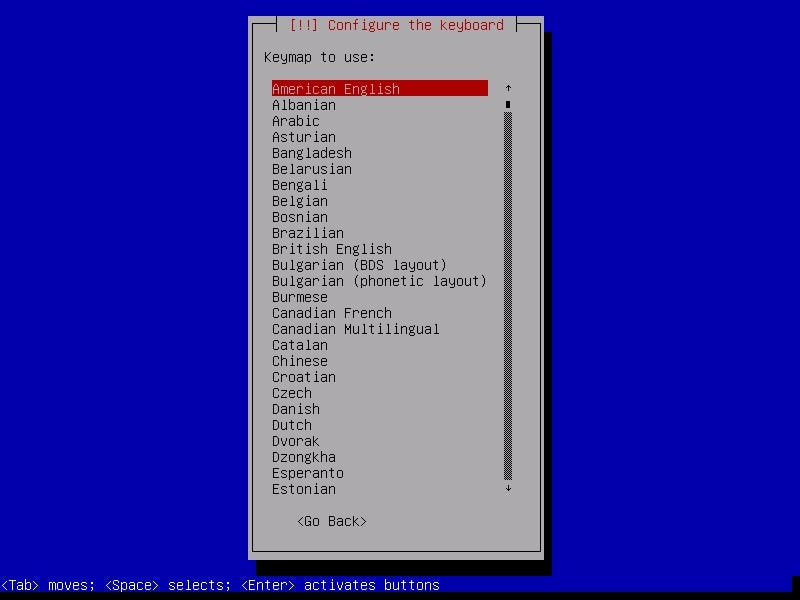
Select the keyboard configuration you want.
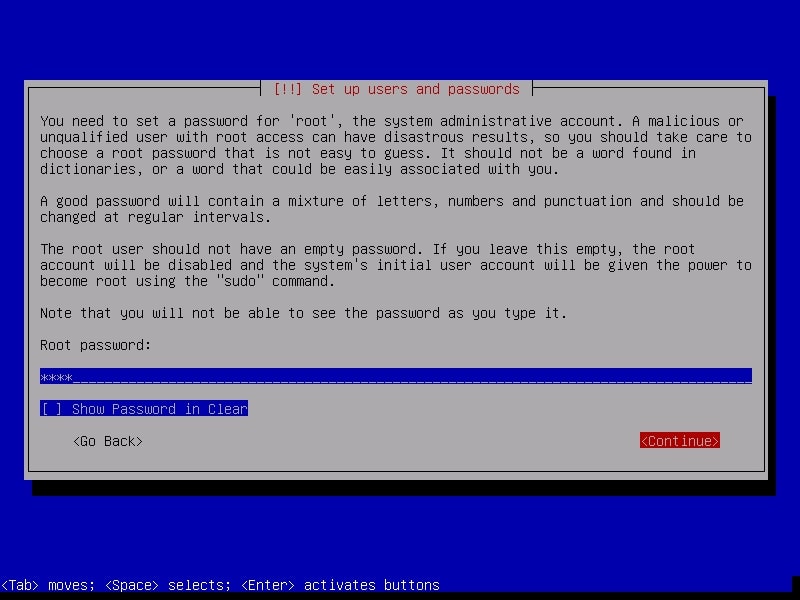
It is important to set the root password (no need to tell it is Linux’s most powerful account) for the machine before we do anything. Set a complex password. Read the suggestions before you set the root password.
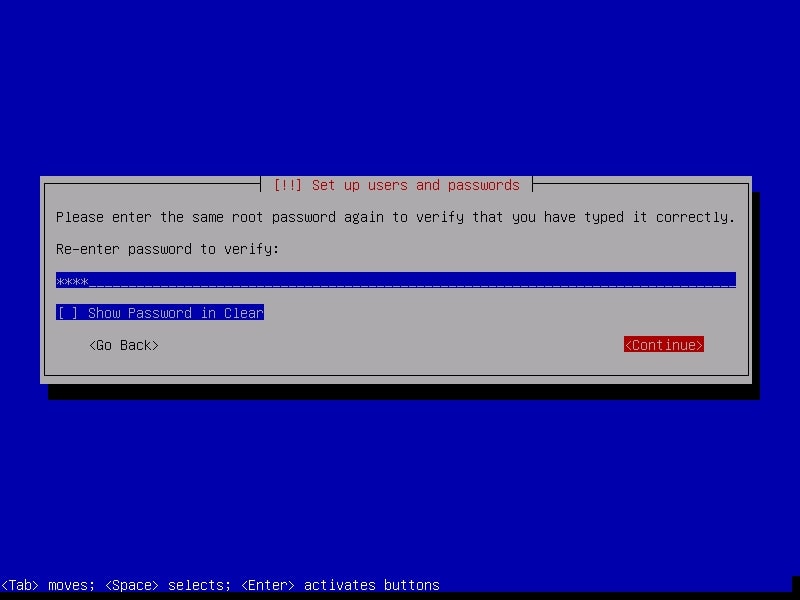
Re-enter the root password again to confirm it.
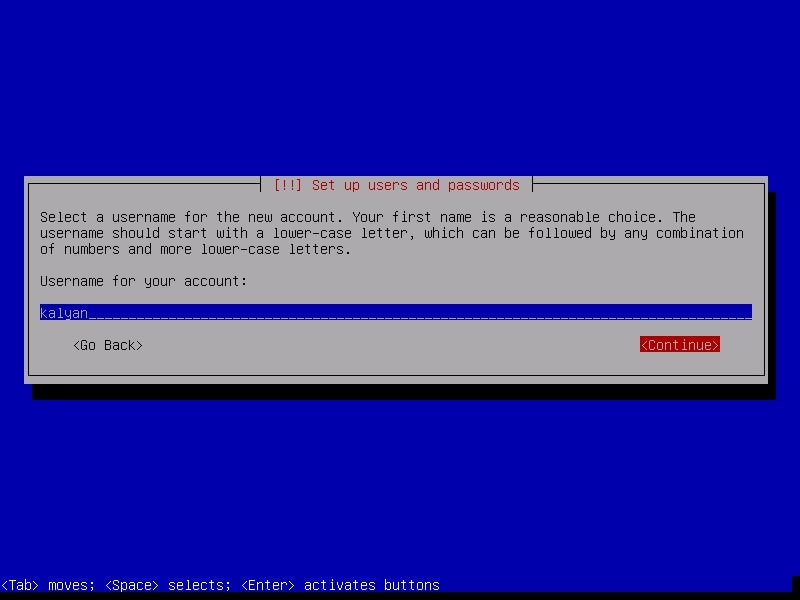
It is a good practice to use the system as a no -n root user. The system will prompt you to create a new user account for non-administrative activities. I am creating a user with name kalyan. I am giving the same name as username.
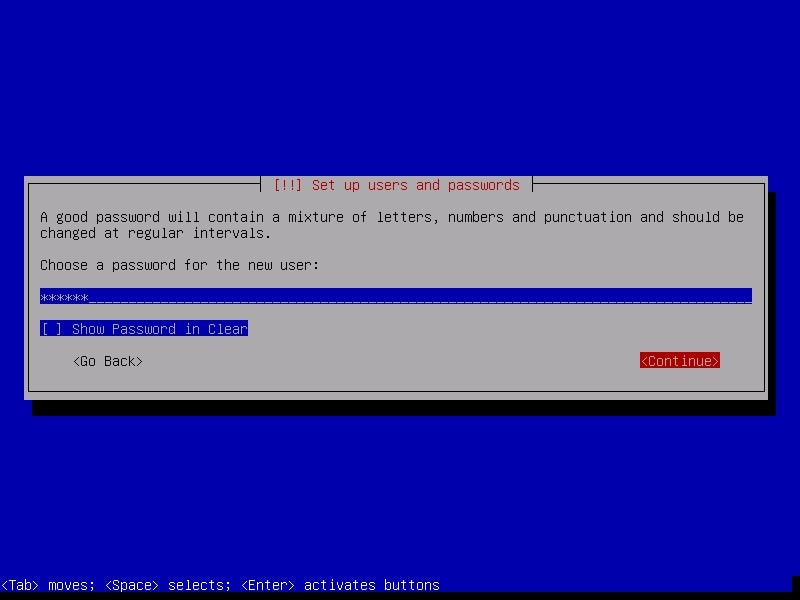
Create a password for the user account you just created. Make it a good password for security reasons.
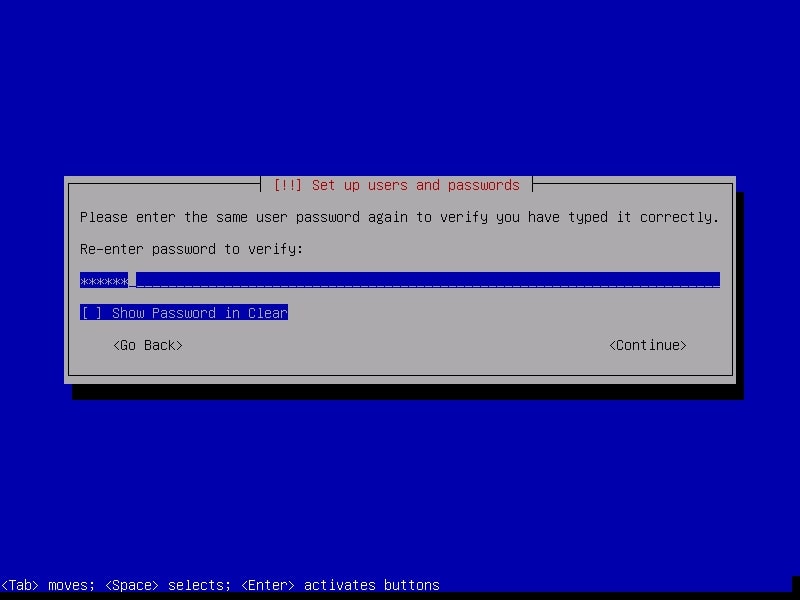
Re-type the password again to confirm the password you have assigned.
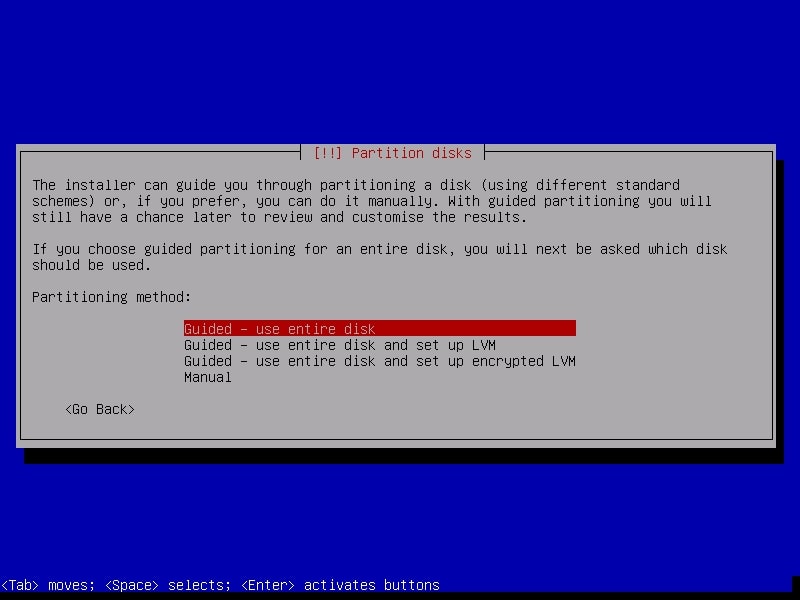
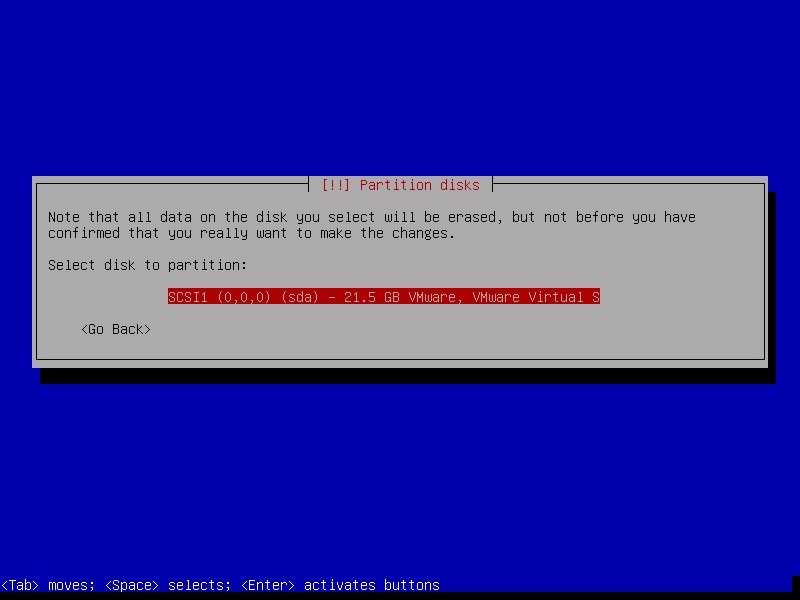
The next step is partitioning the hard disk. Unless you are an expert or want to try something different, use the entire disk.
The system will warn you before partitioning. Select the disk for partitioning.
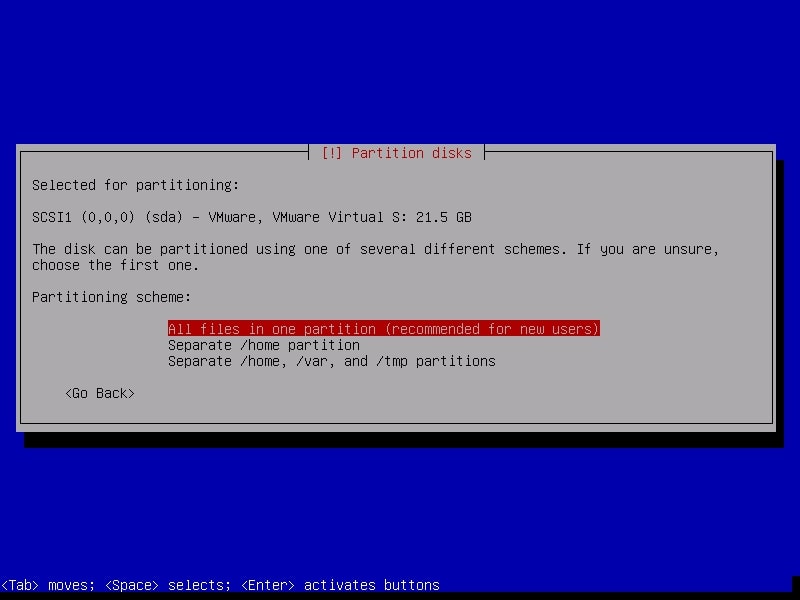
It will ask you to choose the partitioning scheme. Choose the first one. It is also recommended for users.
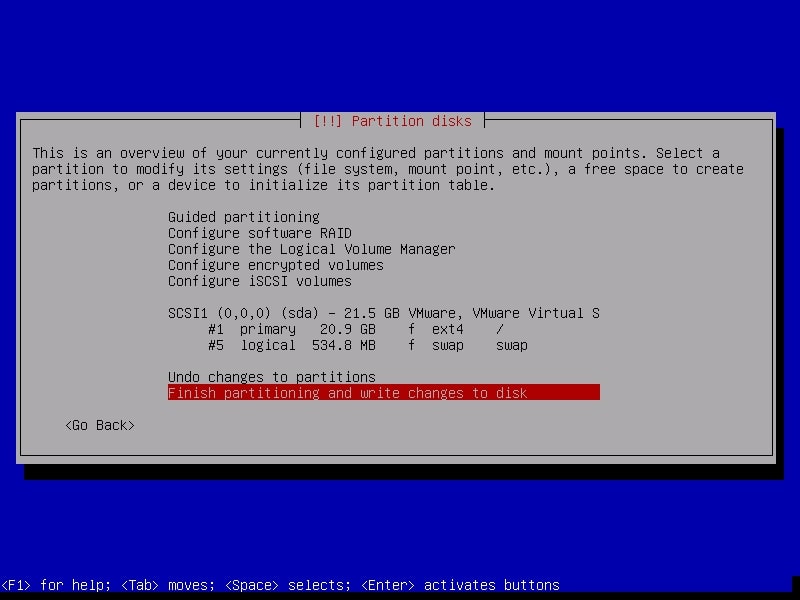
Next, it will show you changes you have configured before writing the changes to the disk. Select “Finish partitioning and write changes to the disk”.
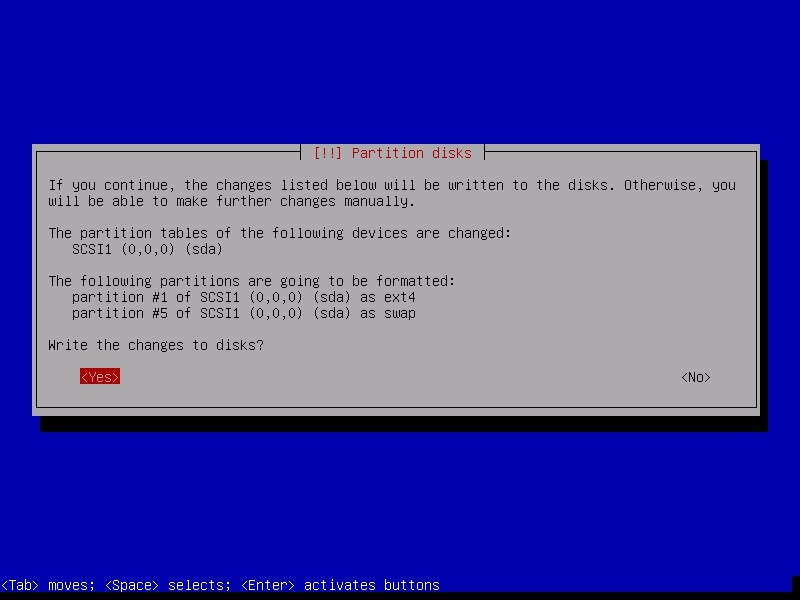
Confirm for one last time that you want to writ-e changes to the disk. Select “Yes”.
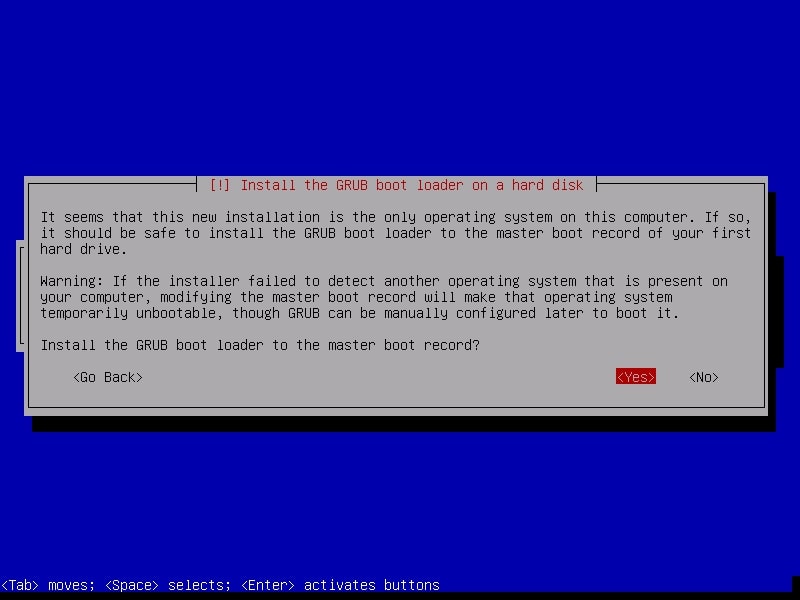
The installation process will start and may take some time. You can have snacks and come back. After installation finishes, it will prompt whether you want to install GRUB boot loader.
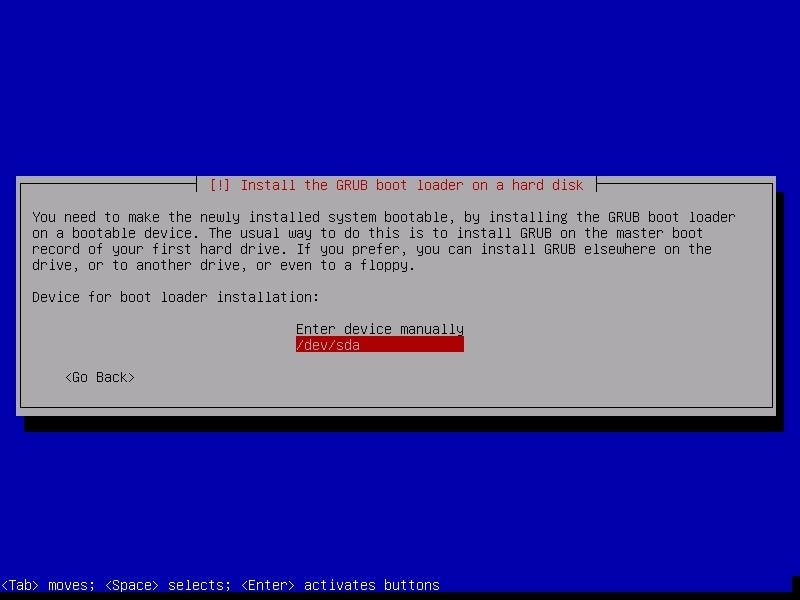
Select Yes. Then it will ask you where to install the boot loader. Select the /dev/sda disk.
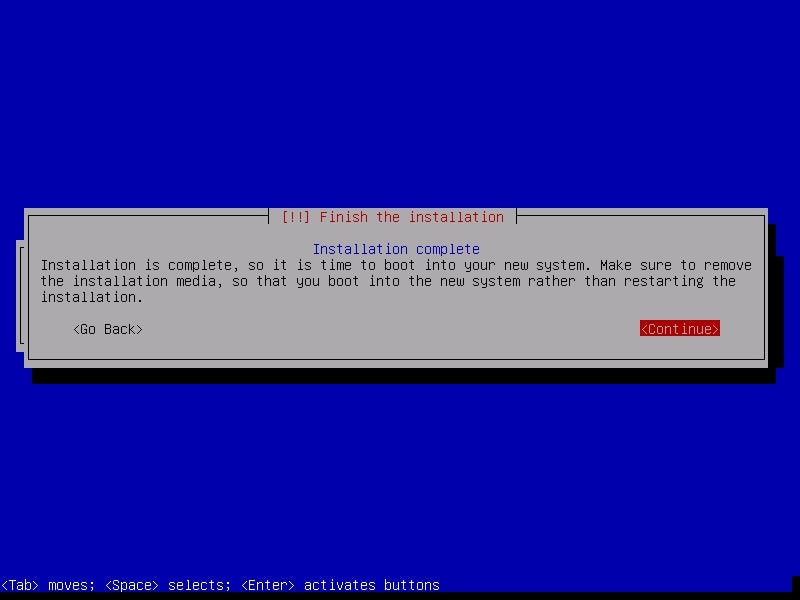
After the installation is finished, it will show you a message as shown below. It’s time to boot into your new system.
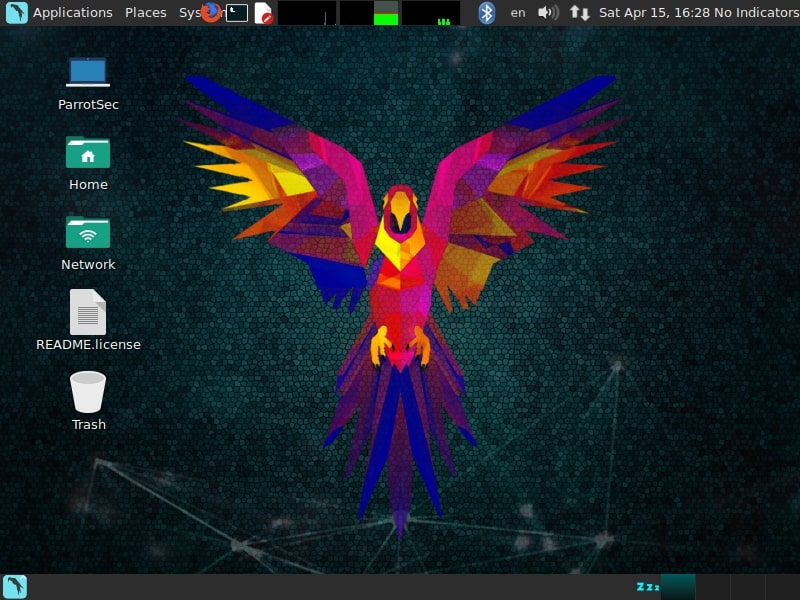
As the system boots, it will ask present you a login screen. You can login as either root or the new user you created it. Once you login, your new pen testing distro should look as below.