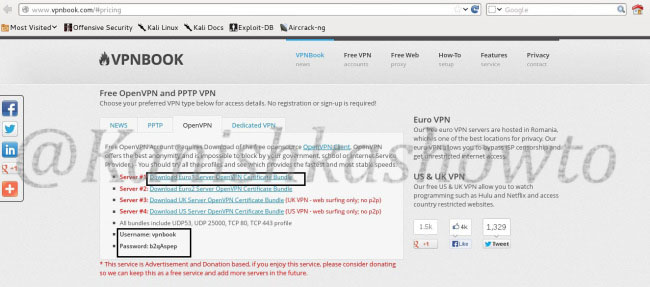
Kali Linux is the most advanced penetration testing distribution with a number of tools. While using these tools a measure of anonymity is required. Today we are going to see how to spoof your IP address in Kali Linux. First, check your IP address by visiting any website which shows your IP address ( http://www.whatismyip.com ). Then go to the site www.vpnbook.com.
Download the Euro1 Server OpenVPN certificate bundle as shown below. Note down the username and password given. We will need it in later steps.
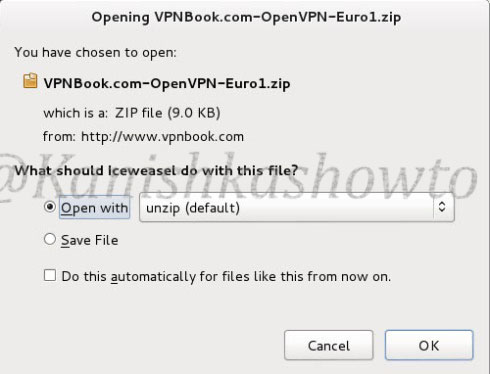
When you click on the download link, the following window opens. Since it is a zip package, system will prompt whether to open it with unzip ( the default option ). Click on “OK”.
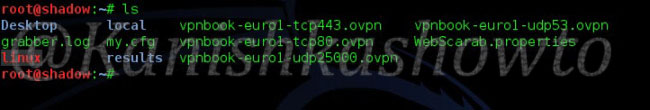
Open the terminal and navigate to the directory where the contents of the zip archive have been unzipped. Type the command “ls” to see the unzipped files. We are going to use the vpnbook-euro1-udp53.ovpn package.
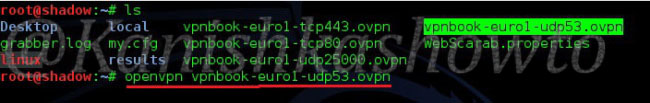
OpenVPN has been installed by default in the Kali Linux distribution. Type the command “openvpn vpnbook-euro1-udp53.ovpn” to start the process.
The installation starts. Enter the username and password we noted above when prompted.
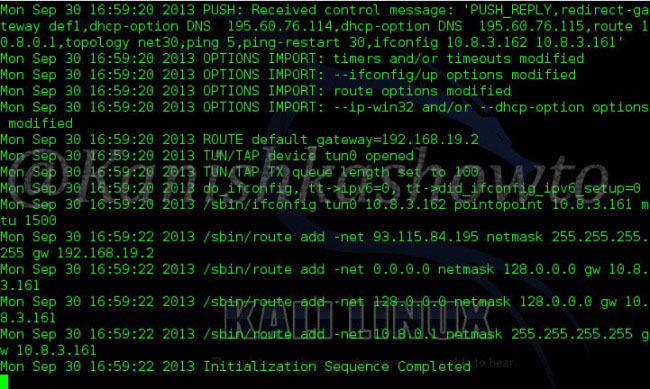
After a short time, the process is completed. Check your IP address again. If everything goes well, your IP address will be changed.