Hello aspiring ethical hackers. In this article, you will learn how to install Parrot OS in VirtualBox. Parrot Security OS, also popularly known as Parrot OS is an operating system specifically designed for pen testing similar to Kali Linux. It is a free and open source GNU/Linux distribution based on Debian designed for security experts, developers and privacy aware people. It includes a full portable arsenal for IT security and digital forensics operations.
In this article, we will show you two methods to install Parrot OS in VirtualBox. They are,
- 1. Using a OVA file
- 2. Using an ISO file
1. Using a OVA file
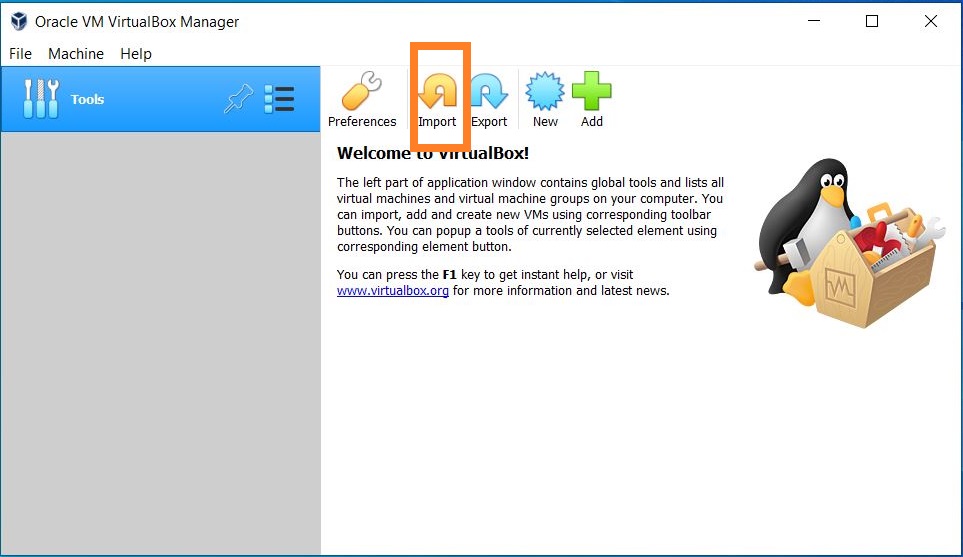
The makers of Parrot OS are providing pre-built images for hypervisors like VMware and VirtualBox. You can download the OVA file of Parrot Security OS from here. Once the OVA file is finished downloading, Open VirtualBox and click on “Import”.
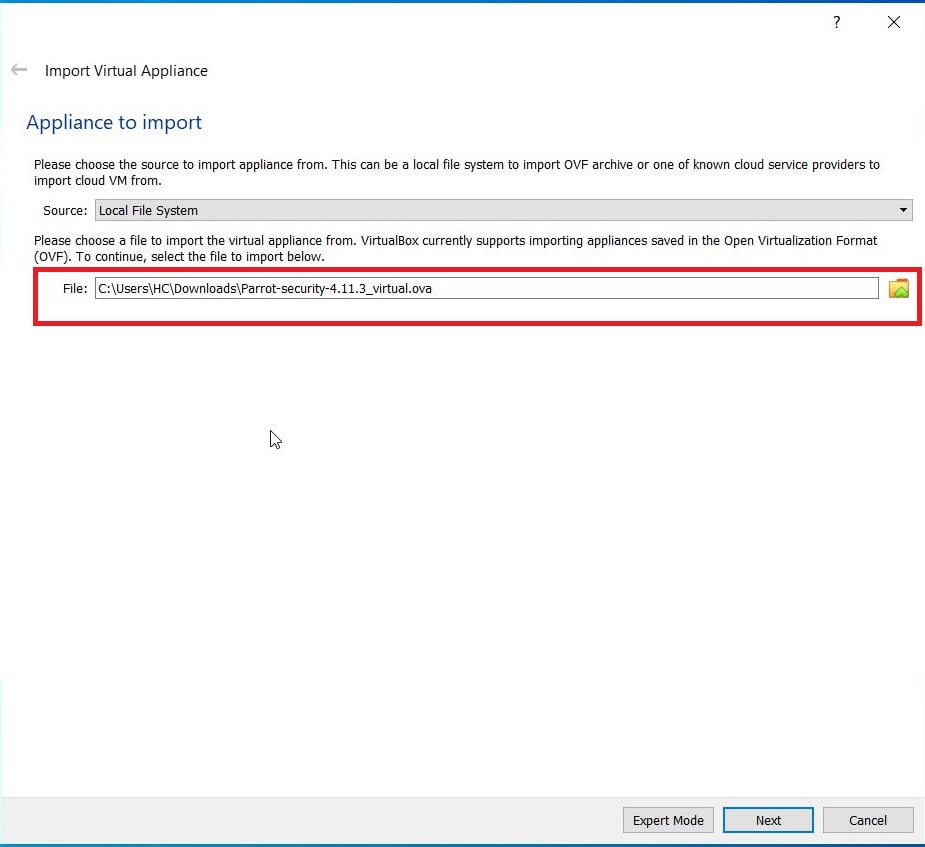
Naviagte to the OVA file we just downloaded and click on “Next”.
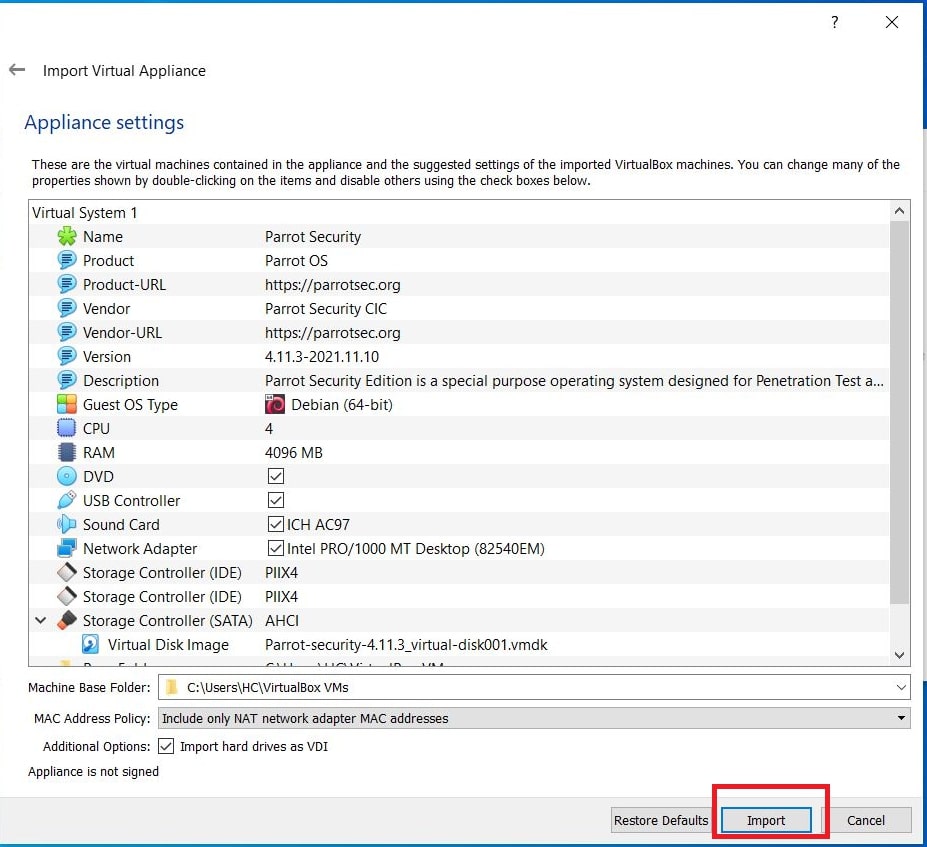
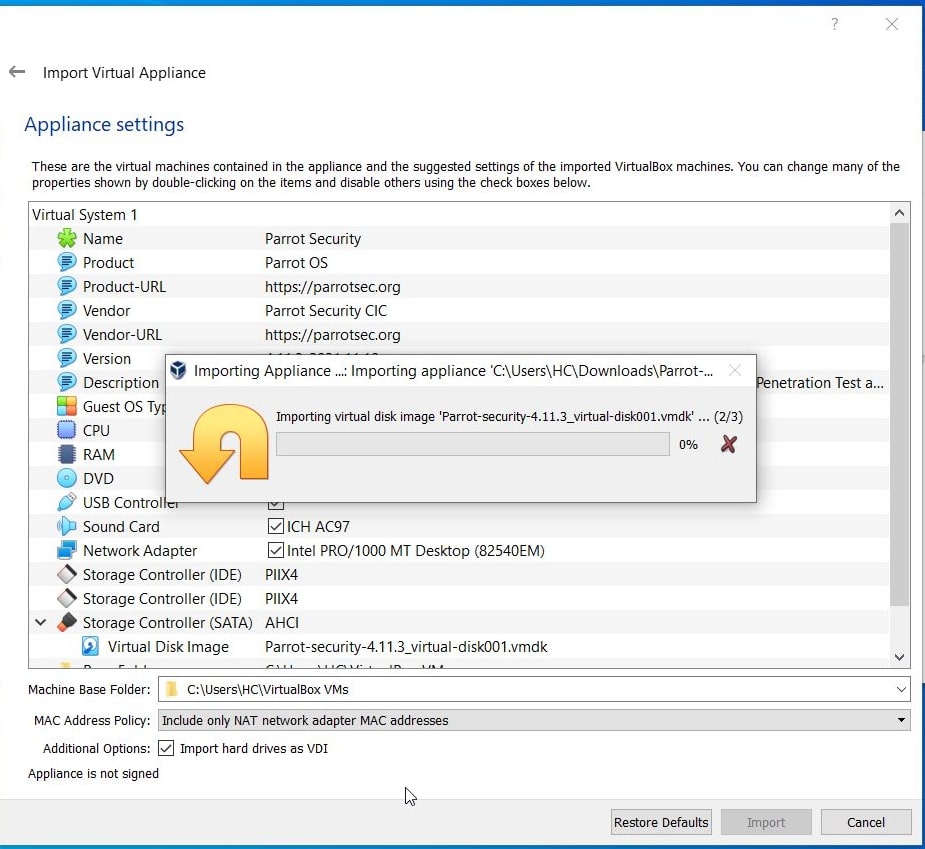
All the settings applied to the virtual machine are displayed. Change any settings if necessary and click on “Import”.
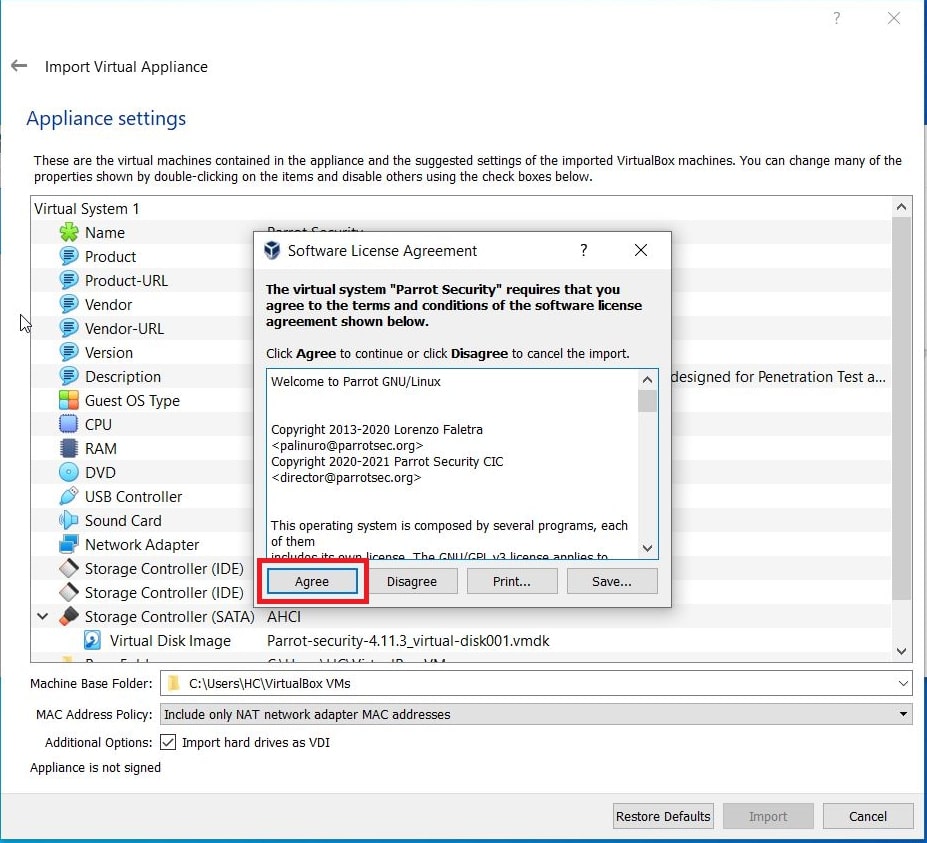
When Software License Agreement is displayed, Click on “Agree”.
VirtualBox will start importing the Parrot Security OS virtual appliance as shown below.
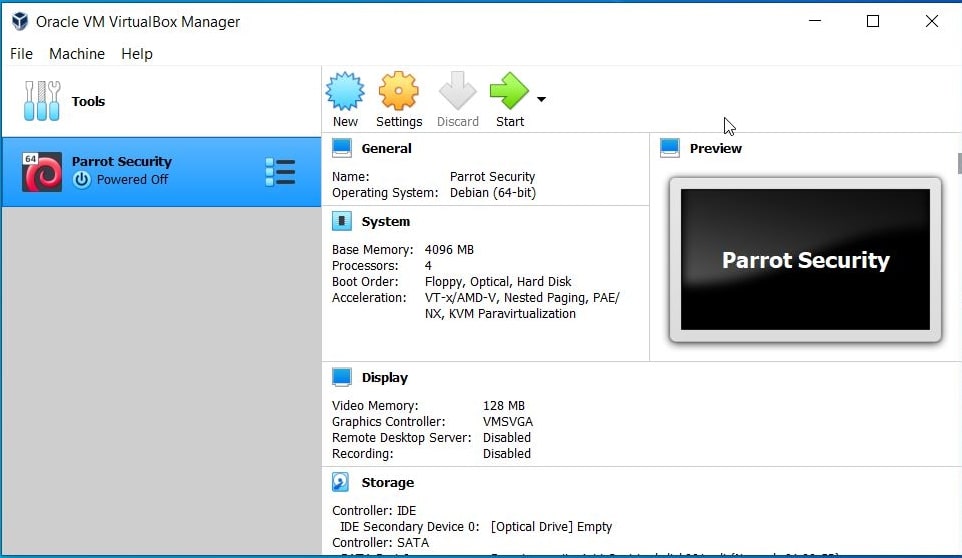
After the import is complete, it will be displayed in the list of virtual machines as shown below.
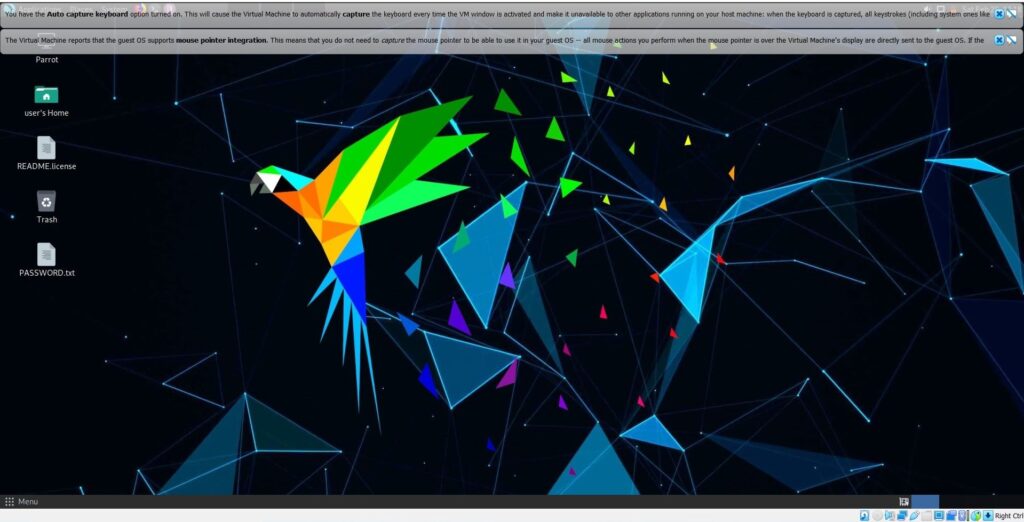
We just need to power it up and the our Parrot OS is ready for pen testing.
2. Using iso file
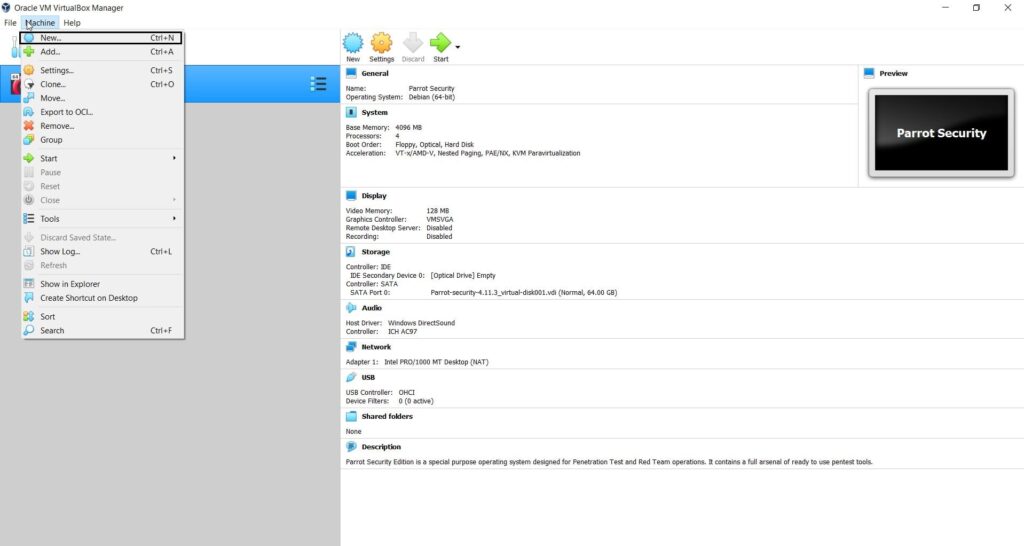
Now, readers will see how to install Parrot Security OS in VirtualBox using ISO file. Download the Parrot security ISO file from here. Once ISO file is finished downloading, open VirtualBox, go to Machine > New or hit CTRL+N.
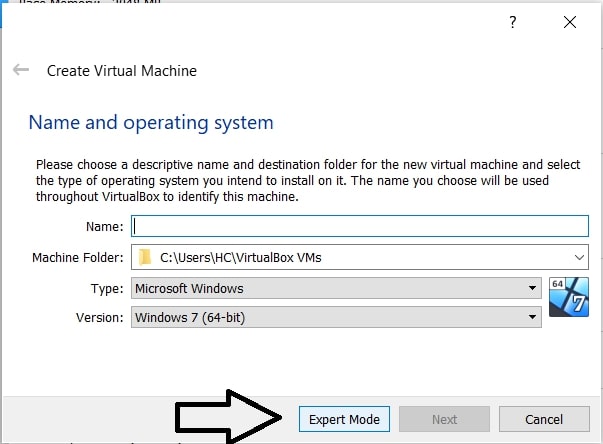
A new window will open as shown below.
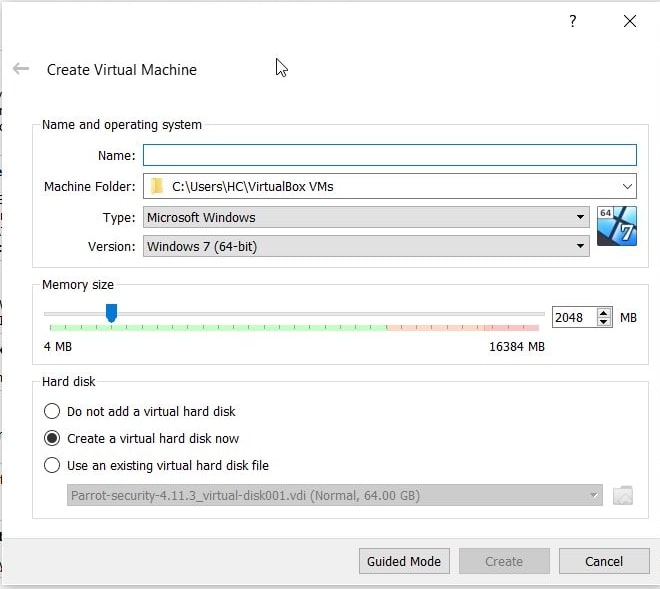
Click on “Expert mode”.
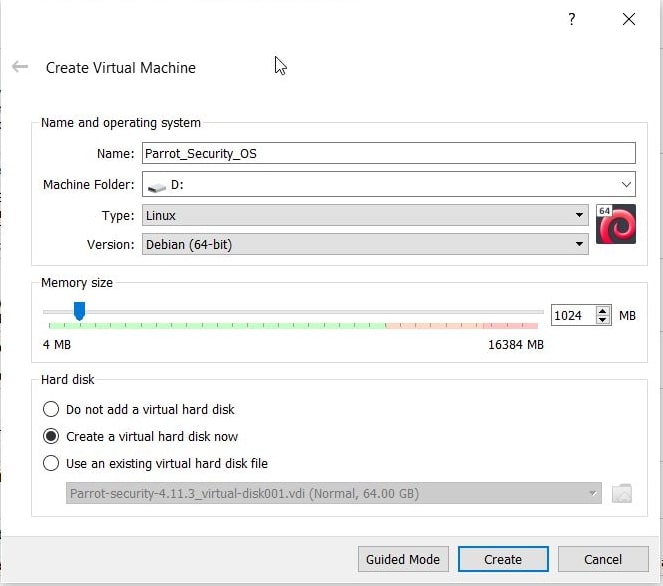
Fill up the details. Configure the machine folder, type of OS, version etc and allocate the RAM (RAM should be minimum 2GB). Once everything is configured, Click on “Create”.
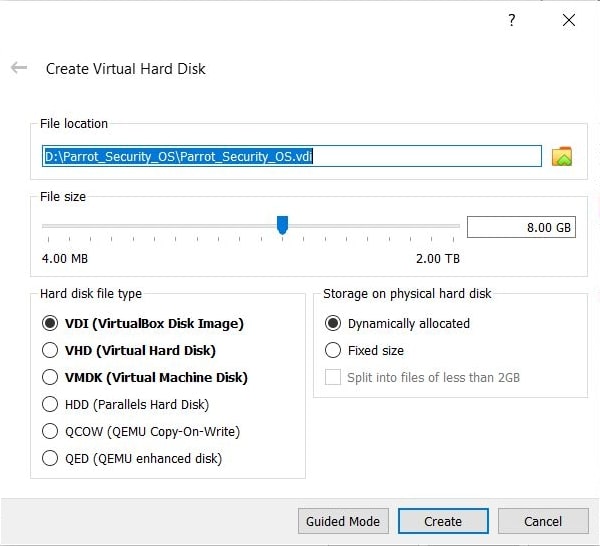
Allocate the hard-disk size (minimum 16 GB is the minimum requirement but keep it at least 20 GB). Set the other options as shown below. Click on “Create”.
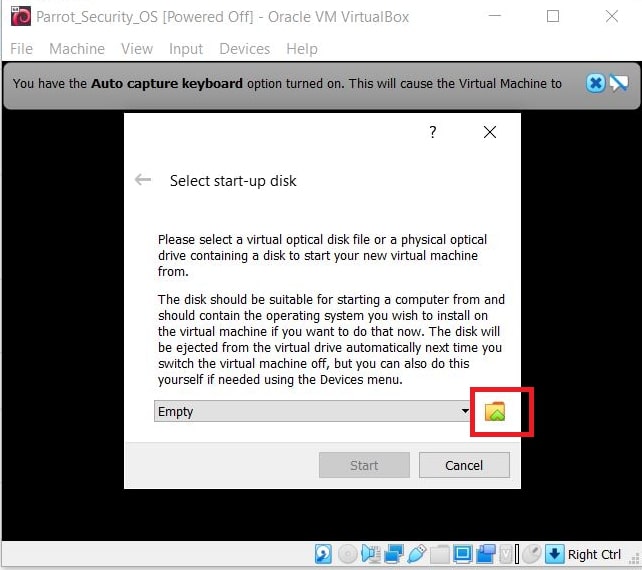
The virtual machine is created. Start the newly created virtual machine. It should start as shown below.
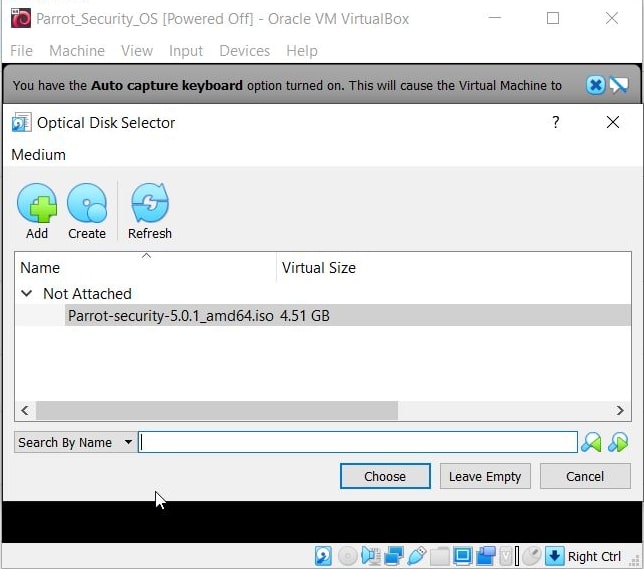
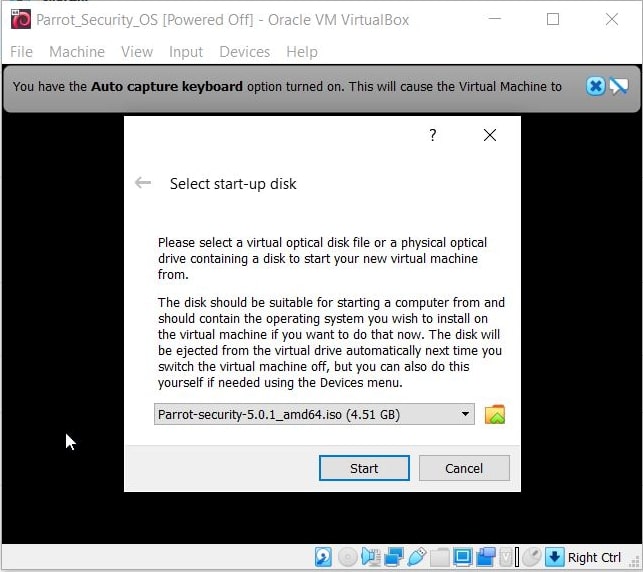
Browse to the ISO file we downloaded earlier and add it as shown below. Then, click on “Start”.
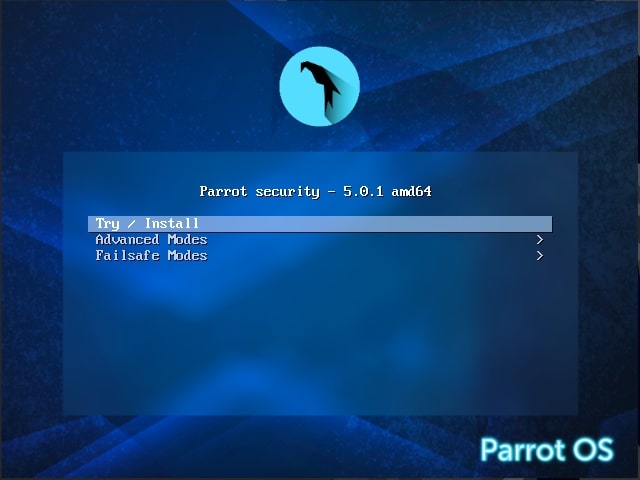
The interface changes as shown below. Click on “Install”.
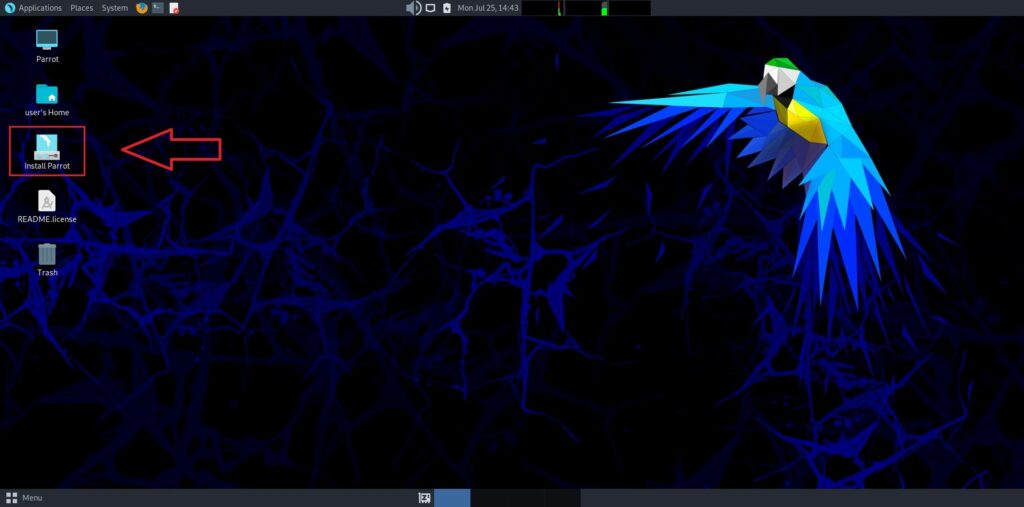
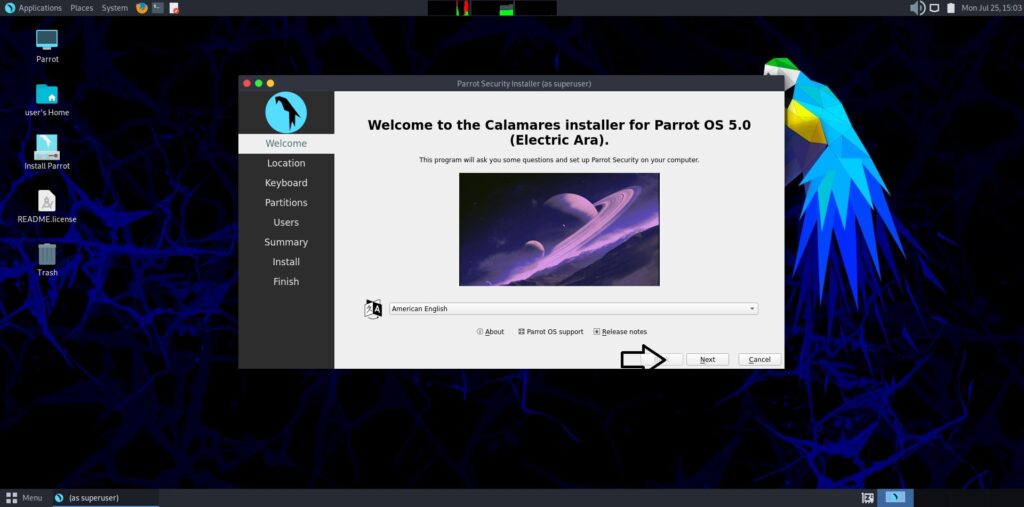
Once you are at the OS interface, click on “Install Parrot “. The Calamares Installer opens.
Click on “Next “. Select Location and click on “Next”.
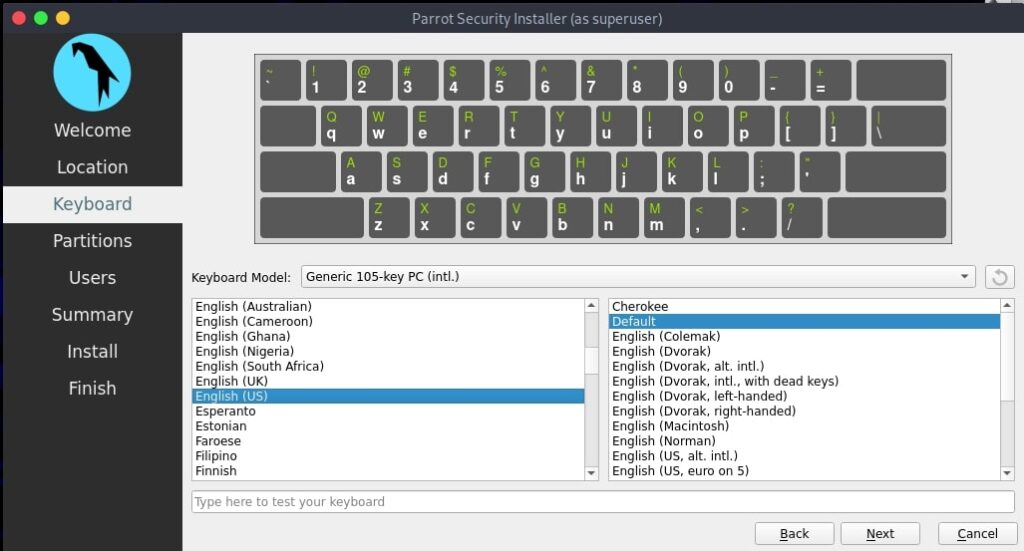
Select the keyboard mode and click on “Next”.
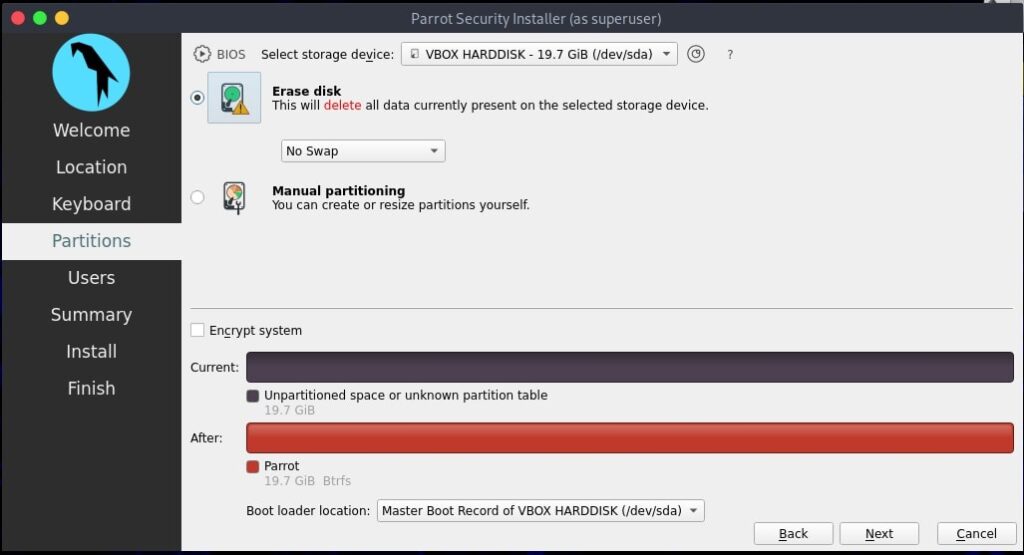
Set the partition. Select “Erase disk” and click on “Next”.
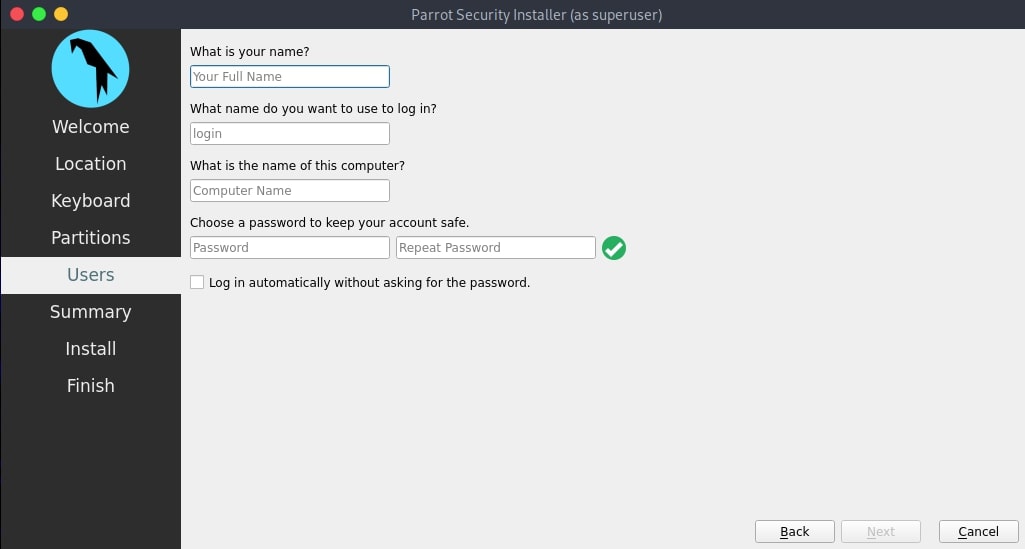
Create a user and set credentials to the newly created user.
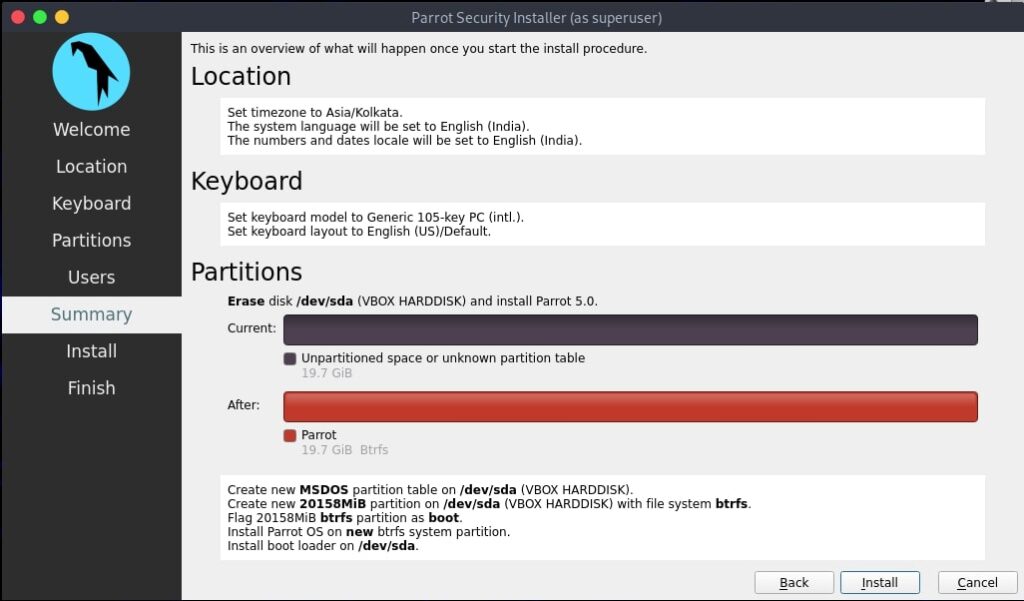
Review all the settings and click on “Install”.
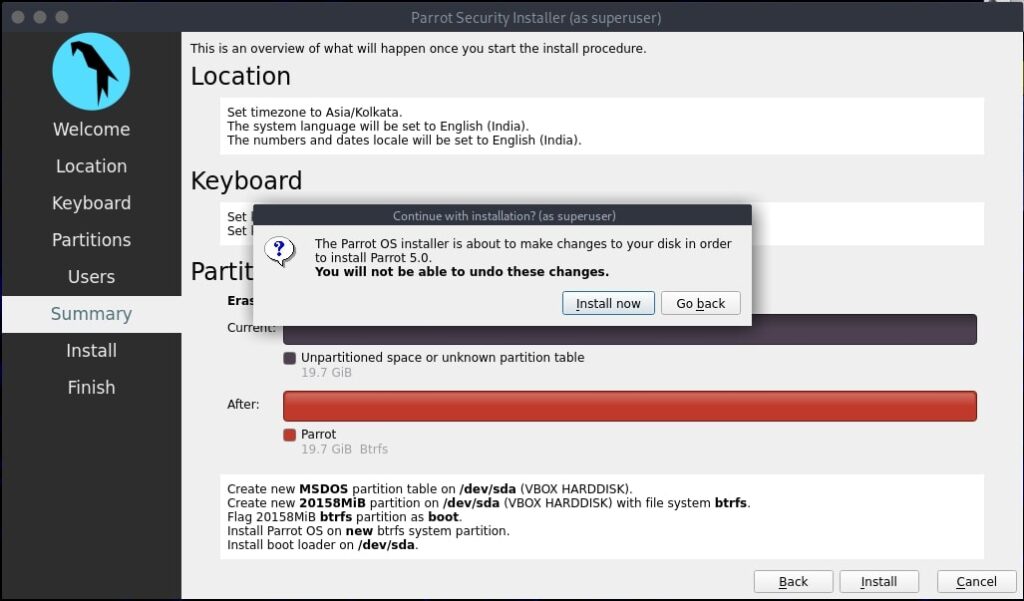
Click on “Install Now.”
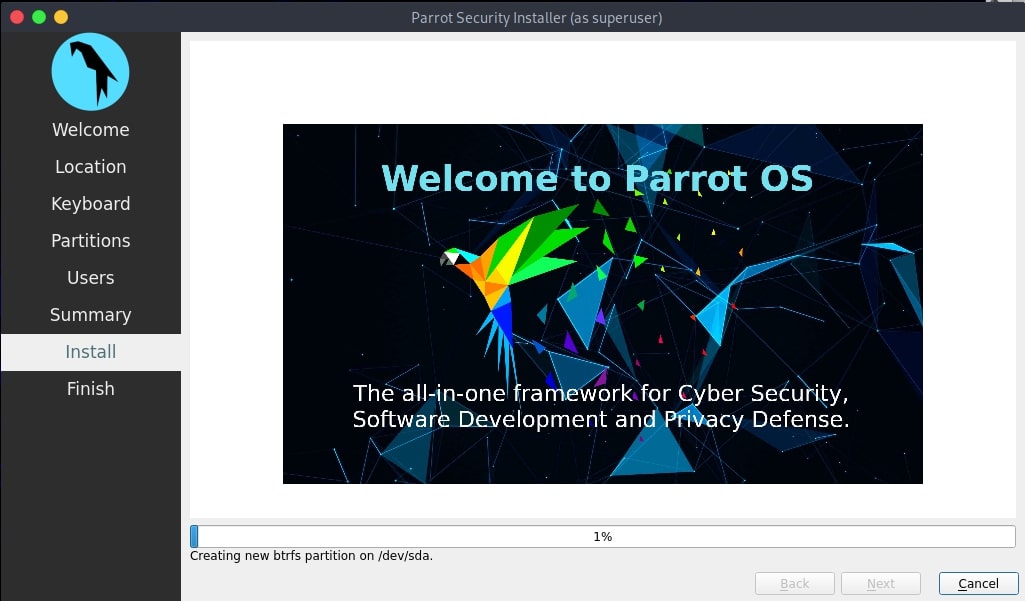
The system starts installing as shown below.
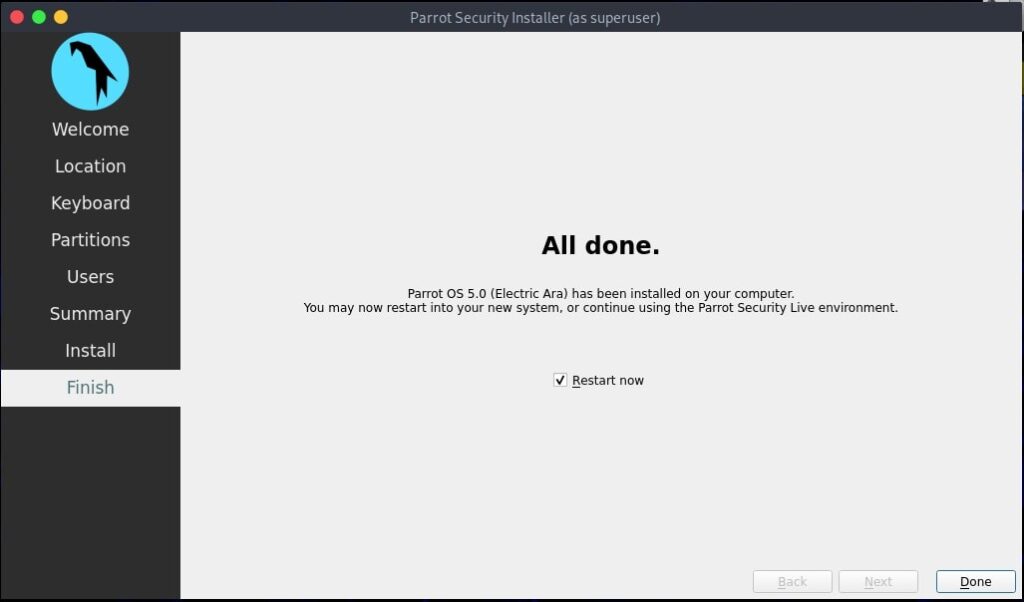
Once the system has finished installing as shown below, click on “Done” .
This will restart the system and will take you to the Login screen. Login using credentials of the newly created user and you are good to go. Happy ethical hacking. Next, see how to install Parrot OS in VMware.