Hello, aspiring ethical hackers. In this blogpost, you will learn about Remote Code Execution (RCE) vulnerability. RCE is considered one of the most dangerous vulnerability that can impact systems or software.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is remote code execution (RCE)?
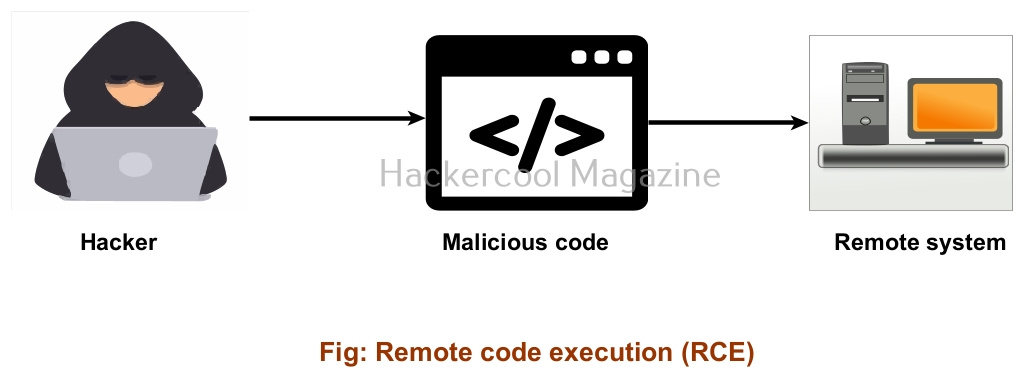
Remote code execution vulnerability allows an attacker to execute code or commands on a remote machine. Code execution on the local system is itself dangerous. Consider hackers having remote access to the machine and about to execute arbitrary commands on the system. As it is a hacker, you can consider that the code being executed is always malicious. This code can be anything like malware, payloads etc.
Vulnerabilities that lead to remote code execution
Any vulnerability that can lead to hackers being able to execute code on the remote machine leads to remote code execution.
- Local File execution
- Buffer overflow
- SQL Injection
- Cross site scripting (XSS)
- Deserialization
- Command Injection
- File upload
- CSRF
- Out of Bounds write
- SSRF
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Impact and execution
Remote code execution can have a dangerous impact that can lead to gaining access, privilege escalation etc. For this reason, it is always considered a CRITICAL vulnerability. Some of the examples of RCE vulnerabilities are,
- ms08_067 vulnerability
- EternalBlue
- PrintNightmare
- Log4shell.
- Spring4shell.
- Shellshock.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply