Hello, aspiring Ethical Hackers. In our previous blogpost, you learnt what is enumeration, why it is important in pen testing and what are the various types of enumeration. In this blogpost, you will learn about LDAP enumeration.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is LDAP?
Lightweight Directory Access Protocol (LDAP) is a protocol that enables users to locate data about the organization, users and other resources like files and devices in a network. LDAP is also used as a central server for authentication. LDAP runs on port 389. Learn how LDAP works.
What information does LDAP enumeration reveal?
By enumerating LDAP, attackers can gather important information like valid usernames, addresses and other data about organization that can help as the hack progresses.
How to perform LDAP enumeration?
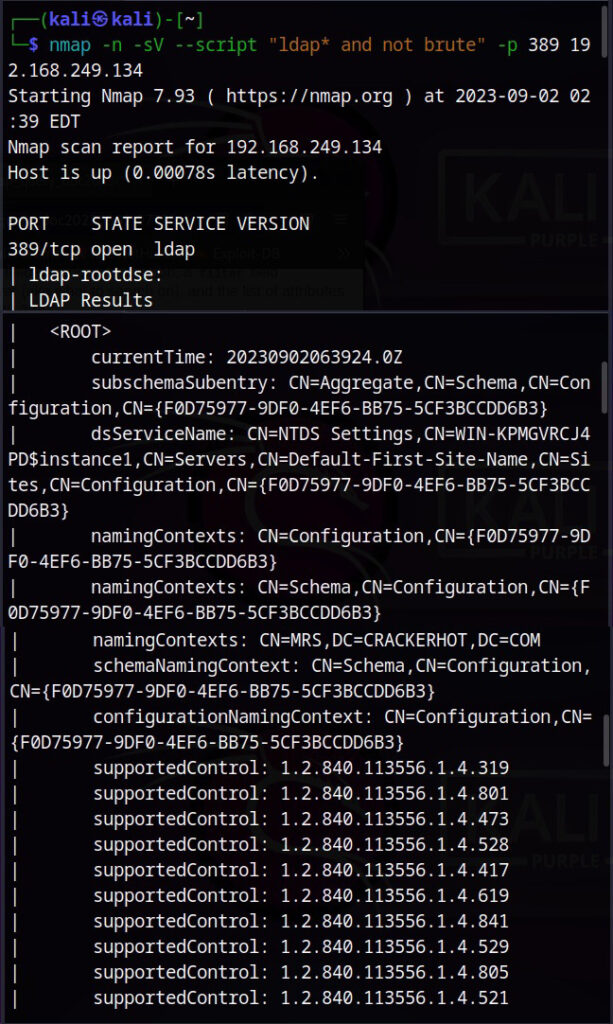
There are many tools that can be used to enumerate LDAP. For this article, let’s see how to perform it using a Nmap script. The script we use is “ldap and not brute”.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply