Hello, aspiring ethical hackers. In our previous blogpost on web application hacking, you have learnt about various vulnerabilities affecting web applications. In this article, you will learn about the most dangerous vulnerability among them all, SQL injection.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
If you’re just starting your journey into ethical hacking or web security, SQL Injection (SQLi) is one of the first vulnerabilities you need to understand. It’s easy to learn, incredibly powerful and still widely found in real-world applications. More importantly, mastering this vulnerability helps you understand how web applications interact with databases, a core concept in cybersecurity. In this article, you will learn what SQL injection is, how it works, types of attacks and how to detect and prevent this vulnerability.
What is SQL Injection?
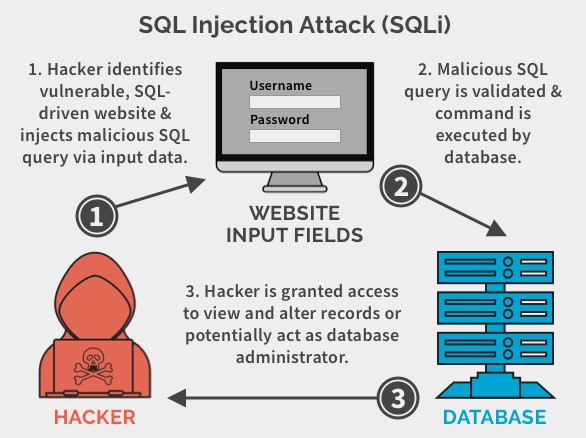
It is a vulnerability that allows attackers to manipulate database queries by injecting malicious SQL code into user inputs. These inputs could be login forms, search fields or even URL parameters.
Web applications often take user input and use it to build SQL queries. If that input isn’t properly handled, attackers can alter the query’s logic and gain unauthorized access to data.
How Does It Work?
These attacks typically occur when a web application does not properly validate user input, such as form data or user-generated content. An attacker can exploit this vulnerability by injecting malicious SQL statements into the input field, which are then executed by the web application’s database.
A Simple Example
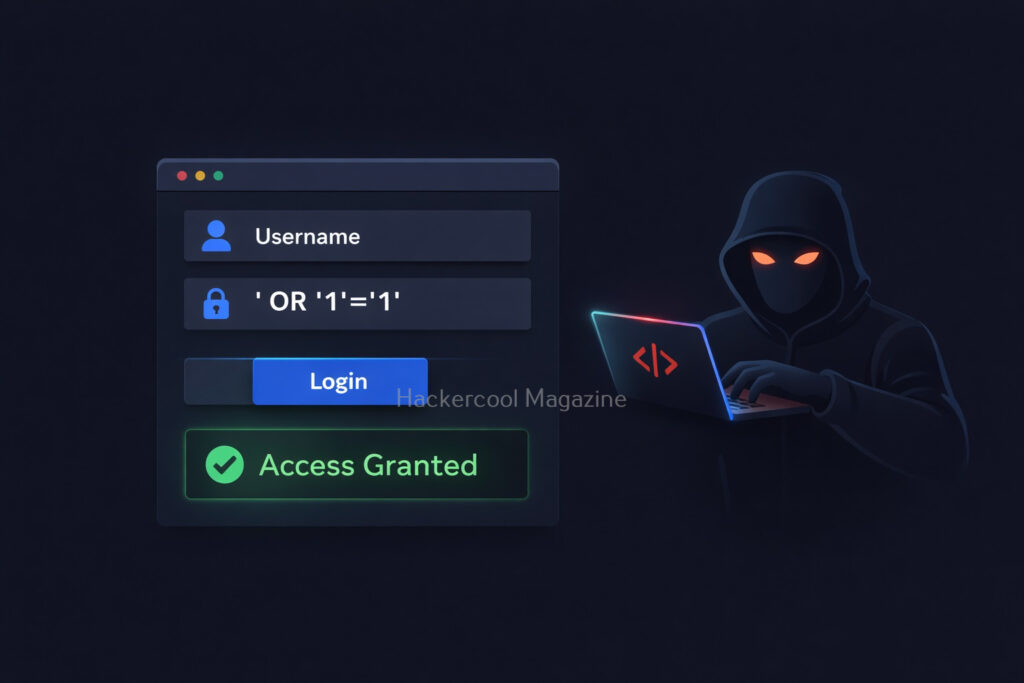
Let’s see SQL Injection with a simple example. Imagine a website login system that checks credentials using a query like this:
SELECT * FROM users WHERE username = 'user' AND password = 'pass';
This looks fine but only if the input is safe. Now, suppose an attacker enters:
Username: admin
Password: ' OR '1'='1
Then, the query becomes:
SELECT * FROM users WHERE username = 'admin' AND password = '' OR '1'='1';
Since ‘1’=’1′ is always true, the condition bypasses authentication. Uisng this, the attacker may log in without knowing user’s password.
This statement would trick the web application into believing that the attacker has a valid username, bypassing the need for a password. The double dash at the end of the statement serves as a comment delimiter which ignores any subsequent characters in the query. As a result, the attacker gains unauthorized access to the application and potentially sensitive data.
SQL Injection attacks can also occur through other input fields, such as search boxes, comment forms and URLs. An attacker can use a variety of techniques to inject malicious SQL statements, such as union queries, stacked queries and blind injection.
Types Of SQL Injection
There are various types of injection attacks. You don’t need to master every type immediately, but knowing the basics helps. They are,
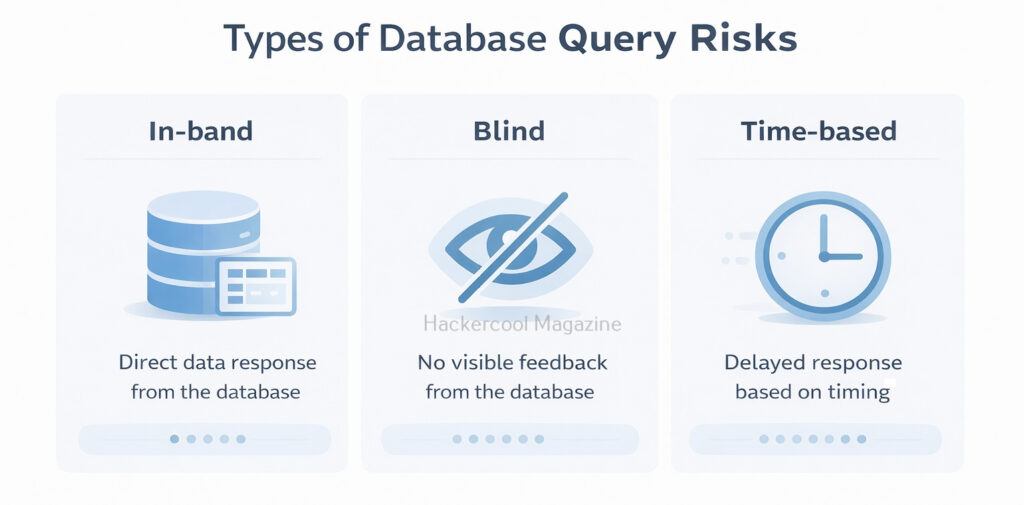
1. In-Band Injection:
This injection type is the most common type. The attacker sends a payload and gets results in the same response.
2. Blind Injection:
In this type of injection, no direct output is shown. Attackers rely on application behavior (like true/false responses or delays) to extract data.
3. Time-Based Injection:
A type of blind SQLi where attackers use delays (e.g., database sleep functions) to confirm vulnerabilities.
Why is SQL Injection Dangerous?
It is not just about logging in without a password. It can even lead to serious consequences. They are,
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
1. Access to Sensitive Data:
Attackers can retrieve user credentials, emails and financial data.
2. Modification or Deletion of Data:
Entire Databases can be altered or wiped.
3. Admin Access:
The attacker can get full control over the application.
4. Server Compromise:
In some cases, attackers can execute commands on the server.
Even today, it remains one of the top security risks because many applications still fail to handle user input securely.
Real-world Examples Of SQL Injection
Here are some of the SQL injection vulnerabilities and their exploitation cases in Real-world.
1. Freepik Data Breach:
In year 2022, hackers stole over 8.3million Freepik & Flaticon users by exploiting a SQL injection vulnerability in company website.
2. Tesla Motors:
In 2014, a security researcher found a blind injection vulnerability in the Tesla Motors Design studio tool. This vulnerability if exploited could have given anyone access to Tesla backend database including customer call records.
3. Heartland Hack:
A team of hackers exploited an injection vulnerability in Heartland and other company’s website to gain access to their network and plant packet sniffing tools and other malware on their network.
How Attackers Find SQL Injection
Attackers often find these vulnerabilities using simple testing techniques. They are,
- Entering special characters like ‘ or ” into input fields
- Trying basic payloads like ‘ OR 1=1–
- Observing error messages or unusual behavior
- Testing URL parameters (e.g., id=1 → id=1′)
More advanced testers use tools but manual testing helps you truly understand what’s happening.
How to Prevent SQL Injection
Here’s the good news. SQL injection is one of the easiest vulnerabilities to fix, if you follow best practices.
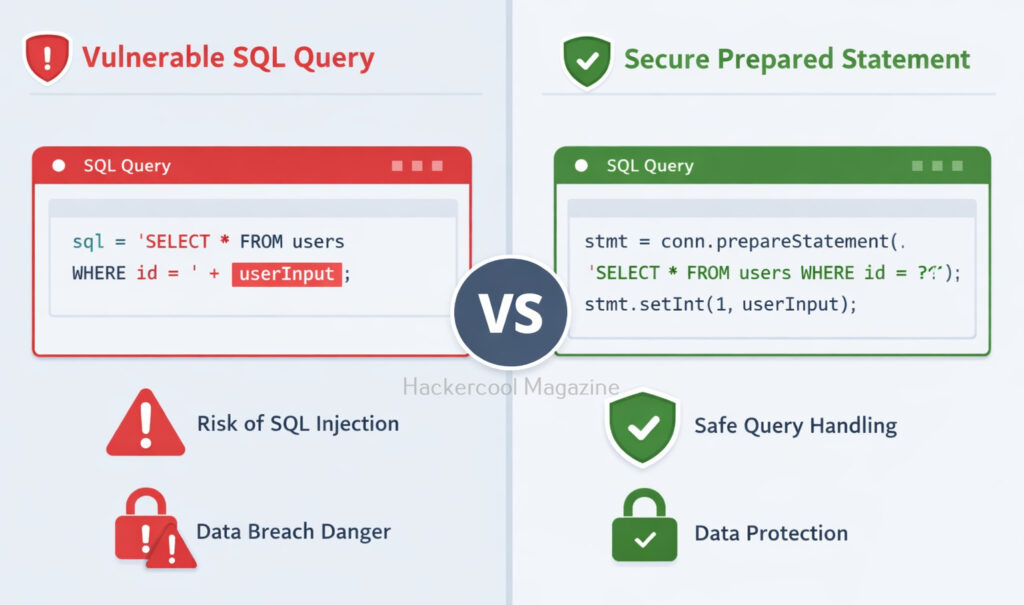
1. Use Prepared Statements:
Prepared statements ensure user input is treated as data, not code. For example,
$stmt = $pdo->prepare("SELECT * FROM users WHERE username = ? AND password = ?");
$stmt->execute([$username, $password]);
2. Validate Input:
This involves validating user input to ensure that it conforms to expected patterns or formats. Input validation can be implemented through client-side and server-side validation techniques.
3. Avoid Dynamic Queries:
Never build SQL queries by directly combining strings with user input. This involves using parameterized queries instead of dynamically generated SQL queries. Parameterized queries use placeholders for user input, rather than incorporating user input directly into the SQL query.
4. Use Secure Frameworks:
Modern frameworks (like Django or Node.js ORMs) handle many security concerns automatically.
5. Limit Database Permissions:
Make sure your application should never connect to the database with full admin privileges. This involves configuring the database server to restrict user access and ensure that each user has only the necessary access to perform their job functions. It also involves implementing strong passwords and two-factor authentication.
6. Hide Error Messages:
Detailed database errors can reveal valuable information to attackers. When a SQL error occurs, the database server may return an error message that includes sensitive information, such as the SQL query that caused the error or details about the database structure. An attacker can use this information to refine their attack and gain further access to the database. To prevent this, it’s important to configure error messages so that they do not reveal sensitive information.
7. Regular Updates:
This involves keeping web applications and database servers up-to-date with the latest security patches and updates.
8. Education and Training:
Regular education and training for developers, administrators and users is critical to preventing SQL Injection attacks. This includes training on secure coding practices, data security and password management.
Tools to detect SQL Injection
There are several tools available to help detect SQL Injection attacks. Some popular tools include:
1. SQLmap:
This is an open-source tool that automates the process of detecting and exploiting SQL Injection vulnerabilities. Learn how to perform sql injection with sqlmap.
2. Havij:
Havij is an automated SQL injection Graphical tool that helps penetration testers to find and exploit SQL Injection vulnerabilities.
3. SQLsus:
Sqlsus is an open-source MYSQL injection and takeover tool
4. Netsparker:
This is a web application security scanner that includes this injection detection and prevention features.
5. Acunetix:
This is another web application security scanner that includes this Injection detection and prevention features.
6. Burp suite:
This is a web application security testing tool that includes a SQL injection Scanner.
7. OpenVAS:
This is an open-source vulnerability scanner that includes this injection detection and prevention features.
Why Beginners Should Learn SQL Injection?
SQL injection is often the first real “aha” moment in ethical hacking. It teaches you,
- How databases work behind web applications
- How small coding mistakes create big vulnerabilities
- How attackers think and exploit systems
Practicing SQL injection in safe environments (like vulnerable labs) builds a strong foundation for more advanced topics like authentication bypass, privilege escalation and web exploitation.
Conclusion
SQL Injection may seem simple but its impact is massive. For beginners, it’s the perfect starting point to understand both offensive and defensive security. If you’re serious about ethical hacking, don’t just read about SQL injection. Practice it in controlled labs, experiment with payloads and learn how to fix it. This combination of attack and defense is what turns beginners into skilled professionals.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply