Hello, aspiring ethical hackers. In our previous blogposts, you learnt about Blue Teaming and Red Teaming. In this article. you will learn what is Purple Teaming, why it matters and how to get started in Purple teaming.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
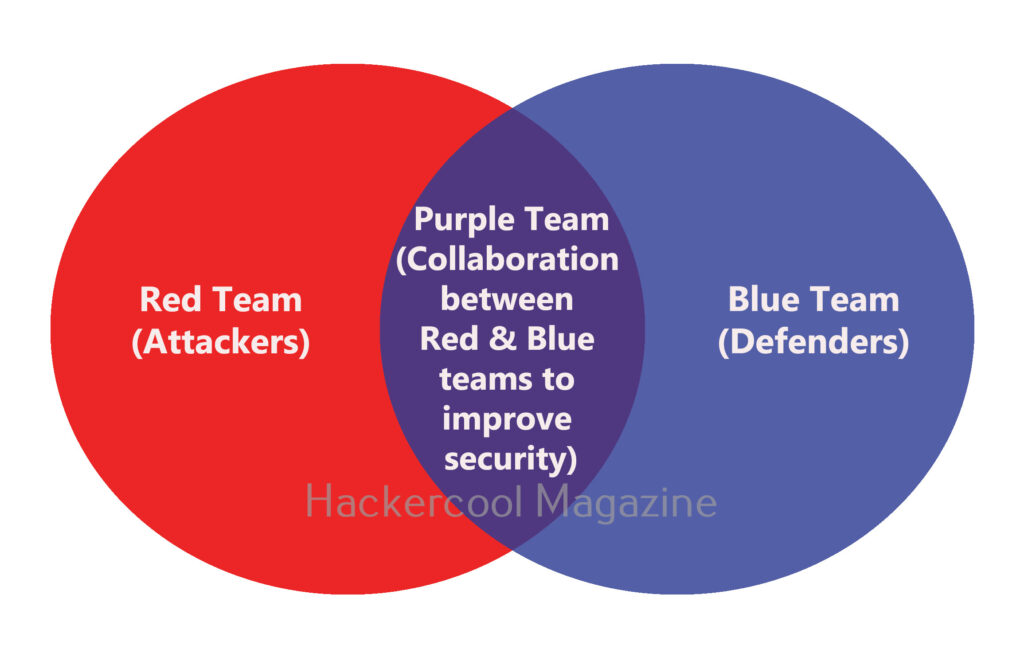
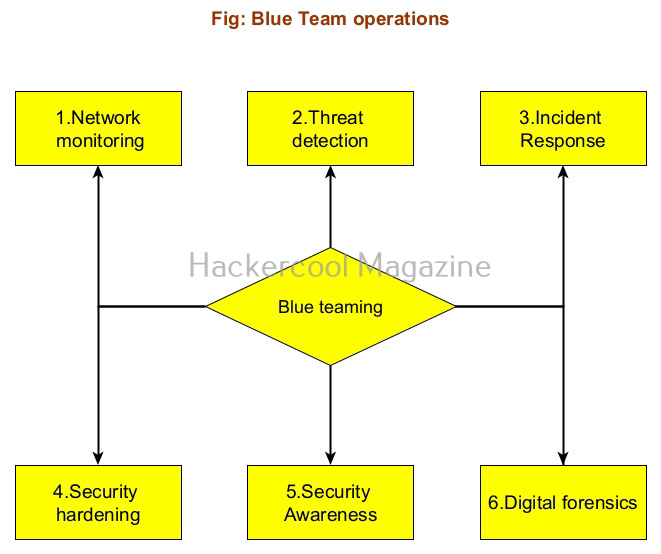
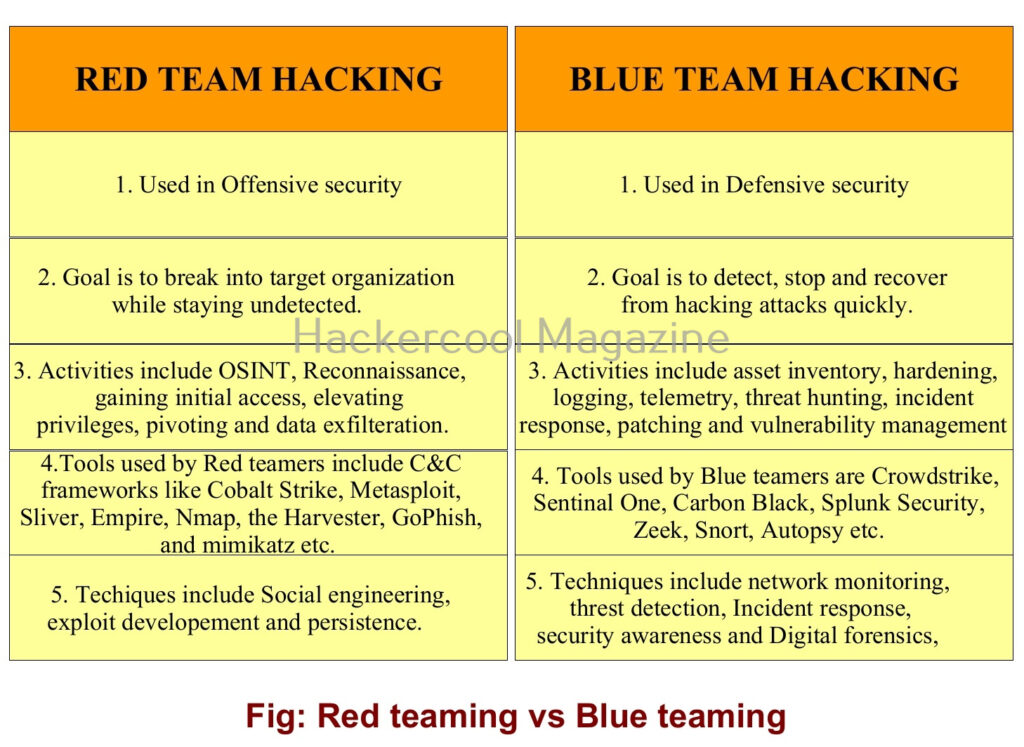
In the ever-evolving world of cybersecurity, staying ahead of attackers is a constant challenge. Traditionally, organizations split their security efforts between two distinct groups: the Red Team, who simulate attacks to find vulnerabilities, and the Blue Team, who defend networks and respond to incidents. But what if these two teams worked together — seamlessly sharing insights and strategies to build a stronger, smarter defense?
What is Purple Teaming?
Purple Teaming is the practice of combining the offensive tactics of the Red Team with the defensive strategies of the Blue Team. The name comes from mixing the colors red and blue to create purple, symbolizing the integration of attack and defense.
Unlike a traditional Red Team vs. Blue Team setup, where each group operates somewhat independently, the purple team approach fosters ongoing communication and collaboration. This way, vulnerabilities discovered by the Red Team can be immediately addressed by the Blue Team and defensive measures can be tested and refined in real-time.
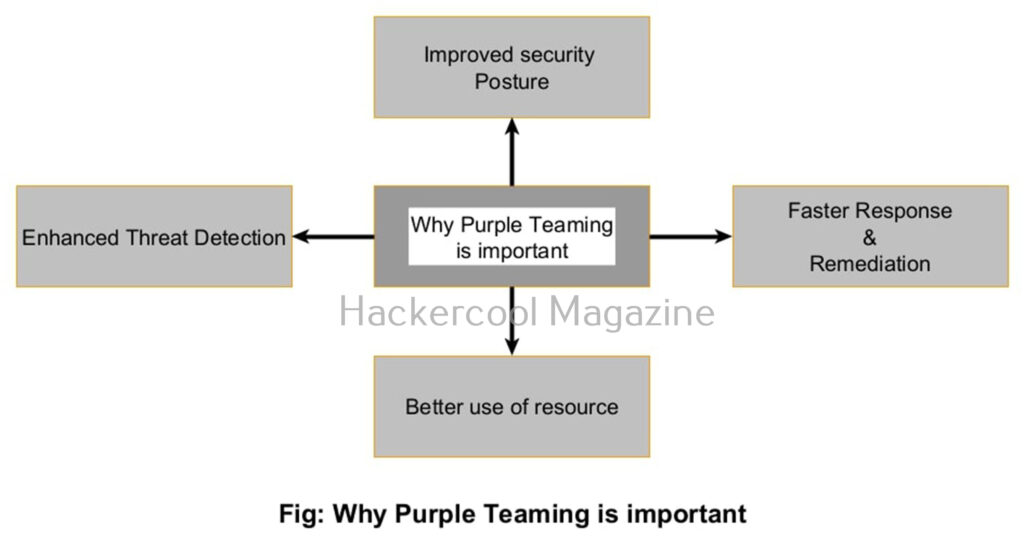
Why is Purple Teaming important?
Here are a few reasons purple teaming is becoming essential in cybersecurity.
1. Improved Security Posture:
By combining insights from both attackers and defenders, purple teams help organizations identify and close gaps faster. It’s no longer a matter of “who found what,” but rather how both teams can learn from each other to build a stronger security posture.
2. Faster Response and Remediation:
When the Red Team discovers an exploit or attack path, the Blue Team can instantly develop countermeasures. This reduces the window of vulnerability and minimizes potential damage from real attackers.
3. Enhanced Threat Detection:
Purple teams help fine-tune detection tools like SIEMs (Security Information and Event Management) and EDRs (Endpoint Detection and Response) by testing alerts against real-world attack techniques. This reduces false positives and sharpens the team’s ability to spot genuine threats.
4. Better use of resources:
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Instead of working in silos, purple teams leverage each other’s skills and tools. This not only improves efficiency but also fosters a security culture focused on shared goals.
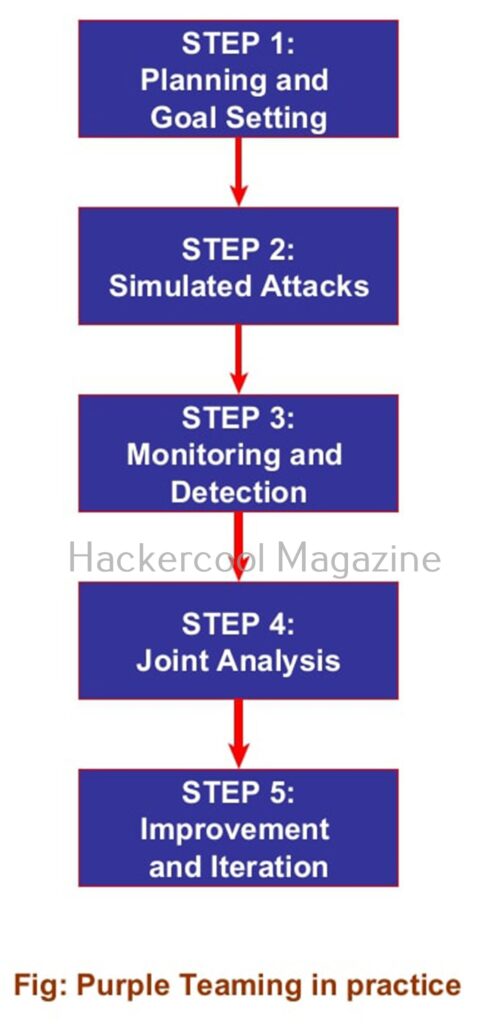
How does Purple Teaming work in practice?
Purple teaming isn’t a just a formal job title or role — it’s a collaborative process that involves people, tools and workflows. Here’s what it typically looks like:
1. Planning and Goal setting:
Red and Blue teams agree on objectives — for example, testing the effectiveness of phishing defenses or evaluating how well the network detects lateral movement.
2. Simulated Attacks:
The Red Team performs controlled attack simulations based on agreed scenarios. They might try phishing campaigns, exploit vulnerabilities, or attempt privilege escalation — all in a monitored environment.
3. Monitoring and Detection:
The Blue Team watches the network, endpoint and security tools to see if the simulated attacks are detected, blocked or logged. They gather data on alerts, response times and gaps in coverage.
4. Joint Analysis:
Both teams review the results together. The Red Team explains attack techniques and where they succeeded or failed. The Blue Team shares how they detected or missed events and discusses improvements.
5. Improvement and Iteration:
The Blue Team adjusts detection rules, hardens defenses or changes response workflows. The Red Team adapts tactics based on updated defenses. This cycle repeats continuously improving the organization’s security.
Tools used in Purple Teaming
Purple teaming doesn’t have separate tools for itself. Tools like Cobalt Strike, Metasploit or open-source frameworks like Atomic Red Team are used by Red Teams to emulate real-world attacks while solutions such as Splunk, ELK Stack or Microsoft Sentinel help Blue Teams analyze logs and tune alerts. Communication and documentation tools like Jira, Confluence or even shared chat platforms like Slack enable smooth teamwork. Emerging tools such as Verodin (acquired by FireEye) and SafeBreach provide automated purple teaming workflows, bridging attack simulations with defense validation.
The future is Purple
Purple teaming represents a shift in cybersecurity mindset — from adversarial to collaborative. By breaking down silos between Red and Blue teams, organizations gain faster insights, stronger defenses and a proactive security culture. Next, learn about Threat Hunting.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply