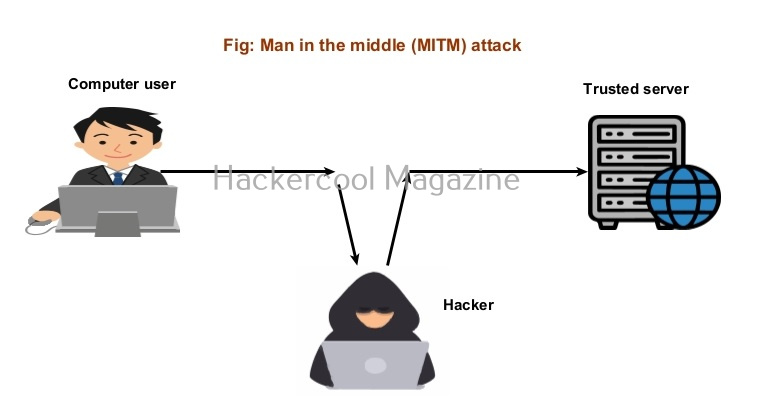
Hello aspiring ethical hackers. In this blogpost, you will learn about Man in the Middle (MITM) attack. You know how does normal communication take place in cyber world. For example, you as a user communicate with a trusted server or resource thinking that the data you send is safely received by the trusted server and vice versa. What if its not.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is Man in the middle attack (MITM)?
In Man in the middle (MITM) attack, a hacker intercepts the communication between a trusted user and server. The information he/she intercepts can be used for malicious purposes.
There are different types of MITM attacks. They are,
1. IP spoofing:
In this attack, the hacker spoofs the IP address of the normal user. Learn more about IP spoofing.
2. Wi Fi MiTM:
In this attack, hackers setup a fake wireless access point that is open. Learn more about evll twin attack.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
3. Sniffing passwords:
If the credentials are being transmitted in cleartext without any encryption in the network, they can be viewed by hackers. Learn more about password sniffing.
In this type of MiTM attack, the session is hijacked. Learn more about session hijacking.
5. HTTPS spoofing:
HTTPS is considered secure as data is transmitted in encrypted format in this. However, even this can be spoofed.
Learn how to perform a variety of MiTM attacks using Websploit.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply


