Hello, aspiring Ethical Hackers. In this blogpost, you will learn about Heartbleed vulnerability. If you’re learning cybersecurity or ethical hacking, you’ll often hear about famous vulnerabilities that changed how the internet works.
One of the most important and dangerous was the Heartbleed vulnerability. Don’t worry if it sounds complicated. In this beginner-friendly guide, you’ll learn:
- What Heartbleed is
- How it works
- Why it was so serious
- What should we learn from it
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is the Heartbleed Vulnerability?
The Heartbleed vulnerability was a major security flaw discovered in 2014 in a widely used software called OpenSSL. OpenSSL is responsible for securing internet communications using encryption (like HTTPS). Heartbleed allowed attackers to read sensitive data from a server’s memory.
Why Was Heartbleed So Dangerous?
Heartbleed was not just another bug. It was a critical vulnerability. Here’s why:
It Exposed Sensitive Data:
Using this vulnerability, attackers could steal:
- Passwords
- Private keys
- User data
- Session cookies
It Left No Trace:
One of the scariest parts:
Attacks didn’t leave logs or evidence.
It Affected Millions of Websites:
Since OpenSSL was widely used, many major websites were vulnerable.
It Could Be Repeated:
Attackers could exploit it multiple times to gather more data.
How Heartbleed Works?
Let’s break HeartBleed down in a way that’s easy to understand.
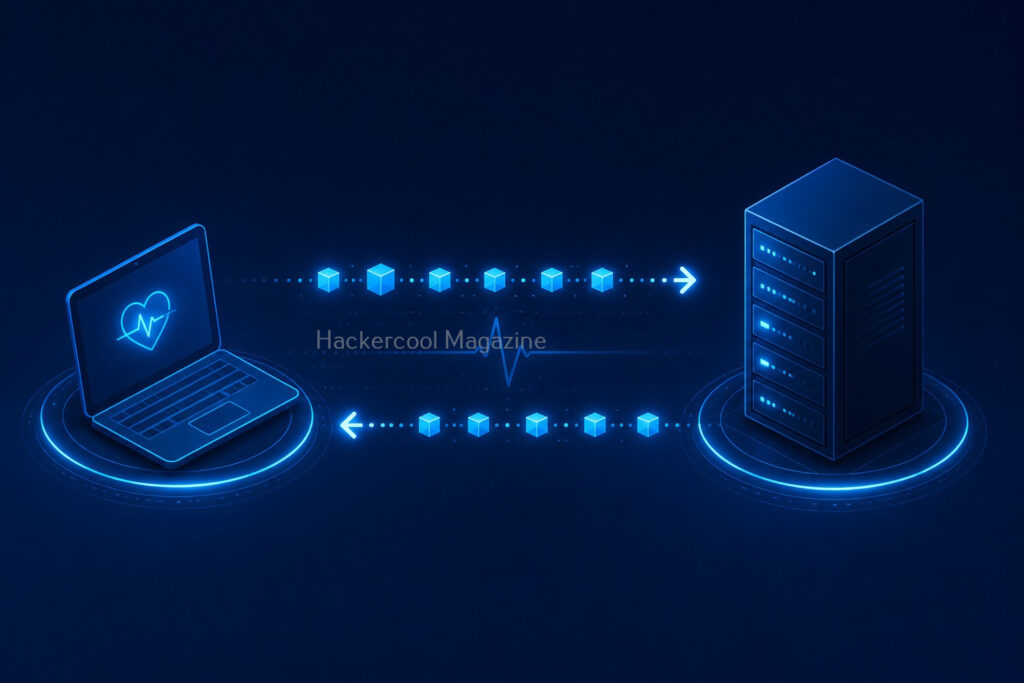
The Idea Behind “Heartbeat”:
OpenSSL has a feature called heartbeat. It works like this:
- A client sends a small message
- The server replies with the same message
This is used to check if the connection is still alive.
The Bug:
The problem was that the server trusted the size of the message sent by the client.
So if an attacker:
- Sent a small message
- But claimed it was larger
The server would respond with:
- The message
- PLUS extra data from memory
The Result:
This extra memory could include:
- Private keys
- Passwords
- Sensitive information
In simple terms, the server accidentally leaked its own secrets.
Practical Walkthrough
Let’s see how this works practically. For demonstrating this, I will be using a Vulhub lab shown in our Hacking Labs to setup a vulnerable instance of Heartbleed as shown below.
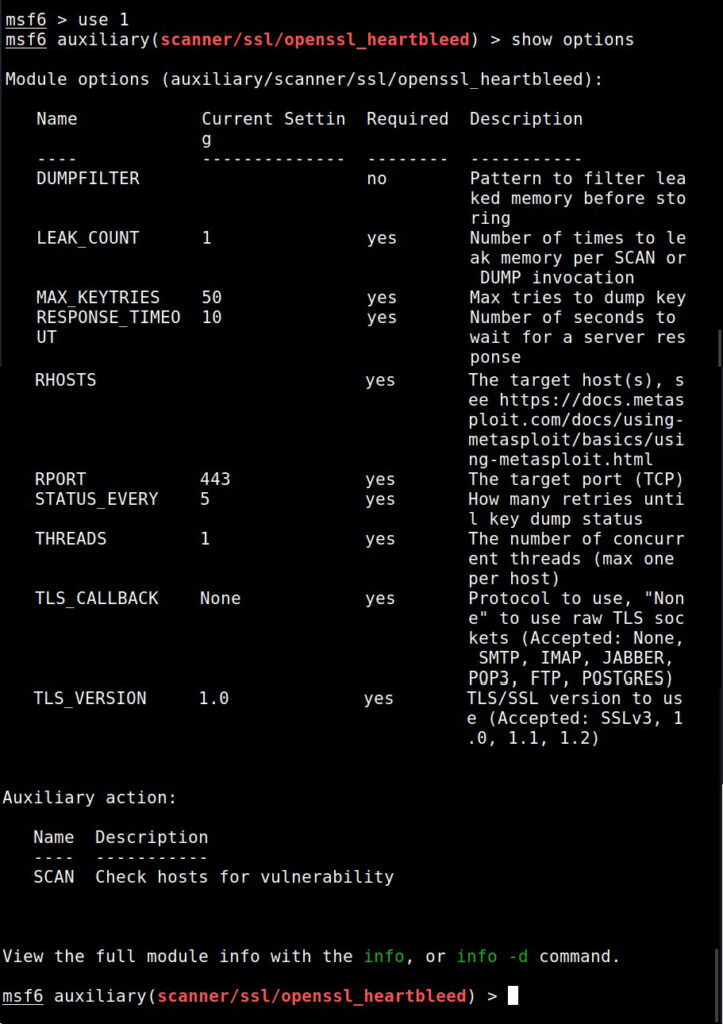
Once the vulnerable instance is ready, I start Metasploit & load the Heartbleed module.
I set the IP address and execute the module.
The module is by default set to scan for the vulnerability and it does exactly that. Apart from this action, this module has other actions.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
For example, the “dump” action dumps the content of the memory.
When we set the action to “key”, the private key of the SSL server gets dumped as shown below.
Real-World Analogy
If that was too technical for you to understand, let me give you a non -technical example. Imagine this scenario: You ask a shopkeeper:
“Give me this 5-page document.”
But the document only has 1 page.
Due to a mistake, the shopkeeper gives:
- That 1 page
- PLUS 4 random pages from confidential files
That’s exactly how Heartbleed worked.
Real-world Exploitation Examples
At the time of public disclosure of this vulnerability, almost 17% of total web servers were found vulnerable to heartbleed, including those belonging to Google, Yahoo, DropBox, Facebook etc. Here are some Real-world explaoitation examples of the heartbleed bug.
Mumsnet:
Mumsnet is a parenting site in United Kingdom. Cyber thieves have obtained passwords and personal messages from Mumsnet by exploiting heatbleed in 2014. Mumsnet has over 1.5 million registered members and there is no idea how many details got hacked.
Canada Revenue Agency:
Social Insurance members of over 900 taxpayers were stolen from Canada Revenue Agency by exploiting heartbleed bug within a 6 hours period on 8 April 2014.
What Systems Were Affected?
Any system using vulnerable versions of OpenSSL are vulnerable to this bug. This included:
- Websites
- Email servers
- VPNs
- APIs
That’s why the impact was massive.
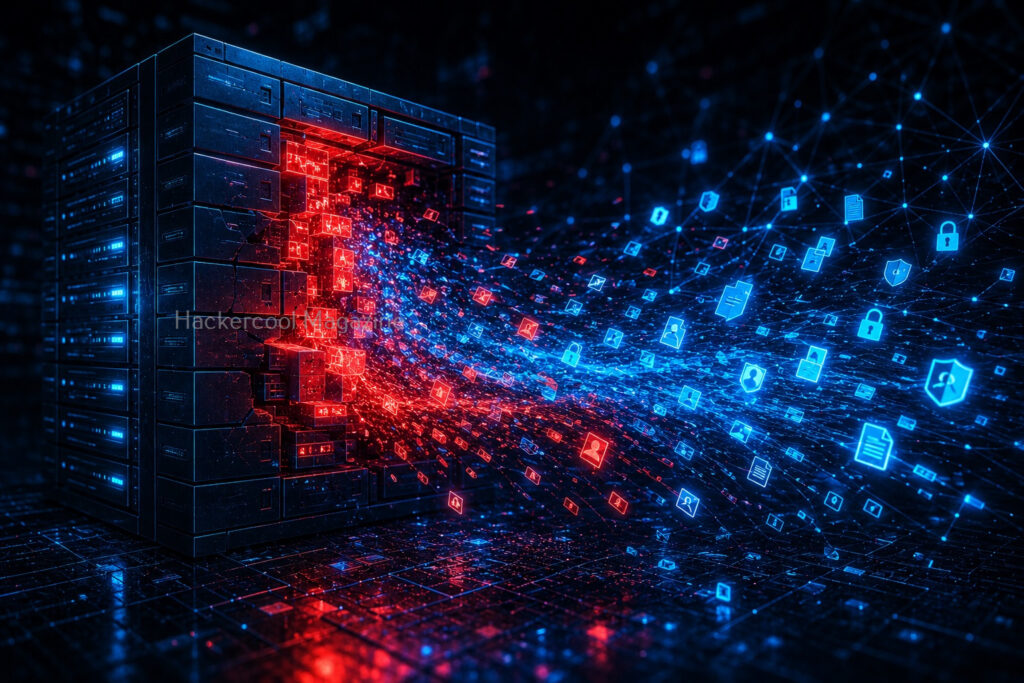
What Data Could Be Stolen?
Heartbleed exposed:
- Private encryption keys
- User passwords
- Session cookies
- Emails
- Confidential data
With private keys, attackers could:
- Impersonate servers
- Decrypt secure communications
Why It Was Hard to Detect?
Unlike many attacks, Heartbleed didn’t:
- Modify files
- Leave logs
- Trigger alerts
This made it:
- Silent
- Stealthy
- Extremely dangerous
How Was It Fixed?
Once discovered, developers:
1. Released Patches:
Updated versions of OpenSSL fixed the bug.
2. Replaced Keys:
Organizations had to:
- Generate new SSL certificates
- Revoke old ones
3. Forced Password Resets:
Users were advised to:
- Change passwords
Fixing Heartbleed required major global effort.
Lessons from Heartbleed (Very Important)
Heartbleed taught the cybersecurity world valuable lessons. They are
1. Even Trusted Software Can be vulnerable:
OpenSSL was widely trusted but still had a critical flaw.
2. Code Auditing is Essential:
Small bugs can cause huge damage.
3. Patch Quickly:
Delays increase risk.
4. Encryption Alone is Not Enough:
If keys are exposed, encryption fails.
5. Security is Continuous:
You must:
- Monitor
- Update
- Improve
Can Beginners Practice Heartbleed?
Yes, but safely.
Use Lab Environments:
Practice on:
- Vulnerable virtual machines
- Training platforms
Never Test on Live Systems:
Without permission, this is illegal. Always stay ethical.
Common Beginner Mistakes
Here are some common mistakes beginners make about HeartBleed vulnerability.
Thinking it’s “Just an Old Bug”:
Even though being an old vulnerability, Heartbleed still teaches important concepts.
Ignoring Memory-Based Attacks:
Not all attacks target websites directly.
Skipping Fundamentals:
Understanding how protocols work is key.
Why You Should Learn About Heartbleed?
Even though it’s old, it helps you understand:
- How vulnerabilities work
- Why validation is important
- How attackers think
It builds your security mindset.
Conclusion
The Heartbleed vulnerability is one of the most important lessons in cybersecurity history. It shows that a small mistake in code can expose millions of systems.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply