Hello, aspiring ethical hackers. In this article, you will learn how to start ethical hacking in 2026. The demand for ethical hackers has never been higher. As cyber threats evolve in sophistication, organizations across the globe are investing heavily in cybersecurity talent. For beginners, 2026 presents one of the best opportunities to enter this field—even without prior experience.
But here’s the truth: most beginners fail not because ethical hacking is too hard but because they follow the wrong path. This guide will give you a clear, practical and beginner-friendly roadmap to start learning ethical hacking from scratch in 2026.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What Is Ethical Hacking?
Let’s begin by explaning clearly what ethical hacking is. Ethical hacking is the practice of testing systems, networks and applications for vulnerabilities, with permission, to improve security. Unlike malicious hackers, ethical hackers:
- Follow legal guidelines
- Work with organizations to fix vulnerabilities
- Help prevent cyber attacks
Think of ethical hackers as security testers or digital bodyguards.
Why Learn Ethical Hacking in 2026?
Long gone are the days Cybersecurity has been optional. The constantly evolving threats have made it critical. Here are some of the reasons why this field is booming.
1. Massive Demand:
Companies need skilled professionals to defend against various kinds of hacking attacks like ransomware, data breaches and AI-driven attacks.
2. High Paying Careers:
Due to the massive demand, even entry-level cybersecurity roles offer strong salaries compared to many other tech fields.
3. Global Opportunities:
You can work remotely, freelance or participate in bug bounty programs worldwide.
4. Continuous Learning:
Ethical hacking is never boring. New vulnerabilities, tools and techniques emerge constantly and this presensts a continuous learning opportunity.
Skills You Need To Be an Ethical Hacker
You know what many beginners do when they want to start learning ethical hacxking. They jump straight into operating systems like Kali Linux, Parrot Security OS etc. This is a mistake. You need a foundation first.
1. Networking Basics:
Learning about networking basics is very important as you will not be hacking islolated single system as an ethical hacker. You will be hacking into networks. So, learn about
- IP addresses
- Subnets
- DNS
- HTTP/HTTPS
- TCP/UDP
If you don’t understand how networks work, hacking won’t make sense.
2. Operating Systems:
You will not only be working on Operating Systems almost all the time but also target operating systems in ethical hacking. So, learn about different operating systems and the differences between them.
Focus on:
- Linux (mandatory)
- Basic Windows internals
Inside different operating systems, Learn:
- File systems
- Permissions
- Command line usage
3. Basic Programming:
You don’t need to be a developer or an expert programmer to become an ethical hacker, but you should understand:
- Python (most important)
- Basic scripting
- Reading code
4. Web Fundamentals:
Most attacks today target web apps. So, learning fundamentals of web is very important.
Learn:
- HTML
- JavaScript basics
- How websites work
Set Up Your Hacking Lab
You can’t master ethical hacking justby studying theory. You need hands-on practice to do that. Never and never practice on real-world systems. Create a safe lab environment.
What You Need:
- A laptop (8GB+ RAM recommended)
- Virtualization software (VirtualBox / VMware)
- Kali Linux
Targets for Practice:
- Intentionally Vulnerable machines like Metasploitable.
- Capture-the-flag platforms
This is where real learning happens.
Learn the Core Areas of Ethical Hacking
Ethical hacking is a broad field. Learn it by focusing on the key areas shown below.
1.Reconnaissance (Information Gathering):
This is the first step of any hacking attack. In this, you learn how to:
- Find subdomains
- Gather public data
- Identify attack surfaces
2. Scanning & Enumeration:
In this phase, you use tools to help you identify:
- Open ports
- Services
- Vulnerabilities
3. Exploitation:
This is where actual hacking happens. In this phase, you learn:
- How vulnerabilities are abused
- How attackers gain access
Once inside a system or network, you will focus on:
- How to gain admin/root access
In this phase, the following actions are performed.
- Maintaining access
- Extracting data
- Covering tracks (for learning purposes)
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Best Learning Path for Beginners (Step-by-step)
Here’s a clear roadmap you can follow to learn ethical hacking.
Step 1: Learn Basics (2-4 Weeks):
Focus on learning:
- Networking
- Linux basics
- Web fundamentals
Step 2: Start Hands-On Practice (4-8 Weeks):
Practice on platforms that simulate real-world environments.
Focus on:
- Basic vulnerabilities
- Understanding attack flow
Step 3: Learn Tools (Don’t Overdo It):
Begin learning some hacking tools. Start with:
Important: Tools are useless without understanding concepts.
Step 4: Practice Real-world Scenarios:
Start practising:
- Capture-the-Flag challenges
- Vulnerable machines
This builds real skill, not just theory.
Step 5: Specialize (After 3-6 Months):
As already mentioned, ethical hacking is a wide field. Choose one path among many. Some of them are given below.
- Web hacking
- Network security
- Cloud security
- Red teaming
A Simple Weekly Study Plan
Here’s how to schedule your week properly to learn.
- 2 days → Theory
- 3 days → Hands-on practice
- 1 day → Review & notes
- 1 day → Break / light learning
How Long Does It Take?
Many people ask how long does it take to learn ethical hacking. Realistically speaking:
- 3 months → Basic understanding
- 6 months → Hands-on skills
- 12 months → Job-ready (if consistent)
Consistency matters more than speed.
How to Practice Like a Real Hacker?
Here are some tips to accelerate your learning and practice like a real hacker.
Think Like an Attacker:
While learning, ask yourself questions like:
- What can go wrong here?
- Where is the weakest point?
Break Things (Safely):
- Misconfigure systems
- Try exploiting them
Document Everything:
Keep notes of:
- Commands
- Techniques
- Mistakes
Repeat and Improve:
Repetition builds mastery.
Career Paths in Ethical Hacking
Once you build your skills, you can choose one of the career paths in ethical hacking. Some of the paths you can take as an ethical hacker are.
Penetration Tester:
A penetration tester simulates real-world attacks on systems and networks.
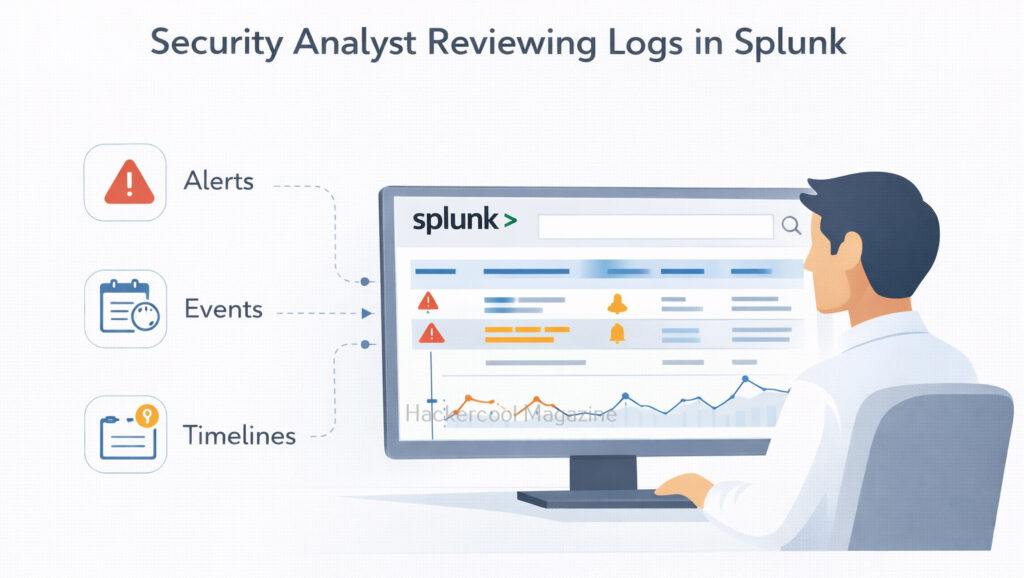
Security Analyst:
A Security Analyst is a person who monitors and defends systems.
Bug Bounty Hunter:
A Bug Bounty Hunter finds vulnerabilities and gets paid for reporting them responsibly.
Red Team Operator:
A Red Team Operator plays advanced offensive security role.
Do You Need Certifications?
Certifications can help in you getting a job but they’re not mandatory. Here are some of the certifications beginners can opt for.
- Basic cybersecurity certifications
- Practical hacking certifications
But remember: Skills matter more than certificates.
Common Mistakes Beginners Make (Avoid These)
Here are some of the most common mistakes almost all beginners make while learning ethical hacking. Please try to avoid making these mistakes.
Jumping into tools too early:
Trust me, ff you do this, you’ll become a “script kiddie” with no real skills.
Skipping fundamentals:
You may think by skipping fundamentals you will go faster but this slows your progress massively.
Watching tutorials without practice:
Passive learning doesn’t work here. What may work in a tutorial may not work in practice.
Trying to learn everything at once:
Focus on one area at a time as trying to learn everything at once may lead to confusion.
Giving up too early:
Ethical hacking has a steep learning curve so prepare for long haul to master it properly.
Ethical & Legal Responsibility
This is critical. Never:
- Hack systems without permission
- Access unauthorized data
Always:
- Practice in legal environments
- Follow ethical guidelines
Remember. Your reputation is everything in cybersecurity.
Final Advice (Most Important Section)
If you remember only a few things, remember these:
👉 Focus on fundamentals first
👉 Practice more than you watch
👉 Be patient—it takes time
👉 Stay consistent daily
👉 Build real skills, not just knowledge
Conclusion
Ethical hacking in 2026 is one of the most exciting and rewarding career paths you can pursue. But success doesn’t come from shortcuts. It comes from structured learning, hands-on practice and persistence. Start small. Stay consistent. Build your skills step by step.
If you follow this roadmap, you won’t just “learn hacking”, you’ll become someone who understands how systems break and more importantly how to secure them.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply