Hello, aspiring ethical hackers. In our previous blogpost, you learnt about pen testing. In this article, you will learn about Red Teaming or Red team hacking.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is Red Teaming?
In today’s digital landscape, cyber threats are constantly evolving becoming more sophisticated and more dangerous day-by-day. Organizations can no longer rely solely on traditional security measures like a simple pen test, technologies like firewalls, antivirus software etc to keep their organization secure. To stay ahead of potential attackers, a proactive, adversarial approach to cybersecurity is needed. This approach is known as Red teaming or Red team hacking.
Red Teaming is a simulated cyberattack conducted by cybersecurity professionals who emulate the tactics, techniques and procedures (TTPs) of real-world hackers like threat actors, cyber criminal groups and Advanced Persistent Threats (APTs). A Red team operation mimics real-world attacks to uncover vulnerabilities in an organization before malicious hackers do. The goal of a Red Team test is to test how well an organization can detect, prevent and respond to an actual cyberattack. It goes beyond typical penetration testing by focusing not just on vulnerabilities, but on people, processes, and technology—the three pillars of organizational defense.
To perform a Red team test, usually multiple members with various skills are required. They are together called as a Red team. Unlike vulnerability scans, pen tests or compliance audits, Red Team exercises are unannounced and designed to test the organization as a whole. This includes the security team’s ability to detect intrusions, the effectiveness of incident response protocols and even the awareness of non-technical staff.
Phases of a Red Team Exercise
Just like a pen test, a Red team exercise or operation has different phases. They are,
- Setting objective (s): A Red team exercise begins by setting a specific goal first. The goal could be exfiltration of organization’s data, taking full control of the network or particular device etc.
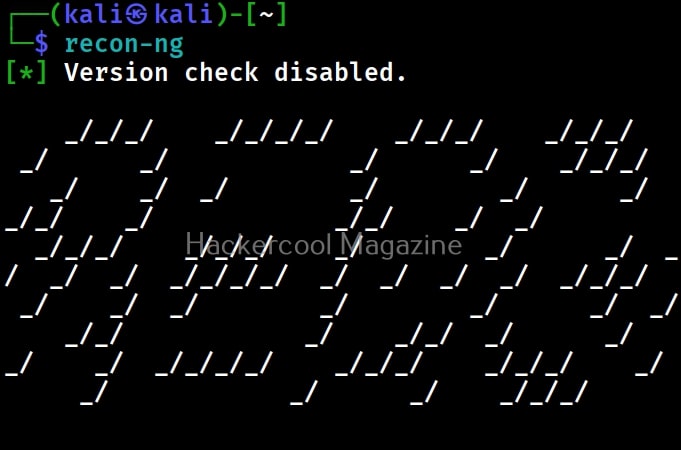
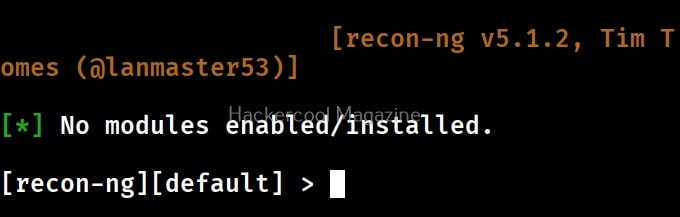
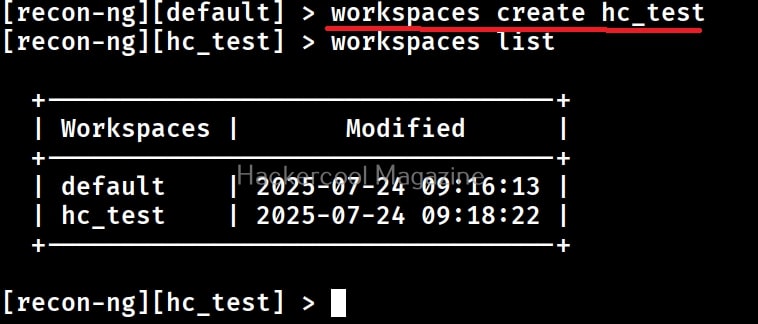
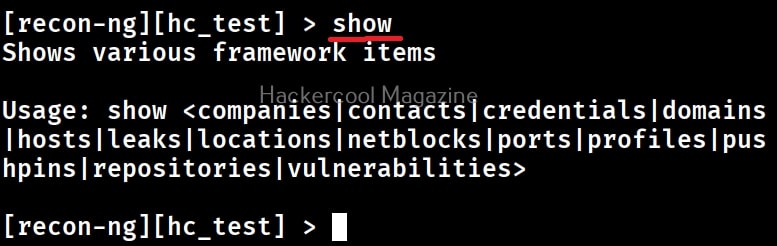
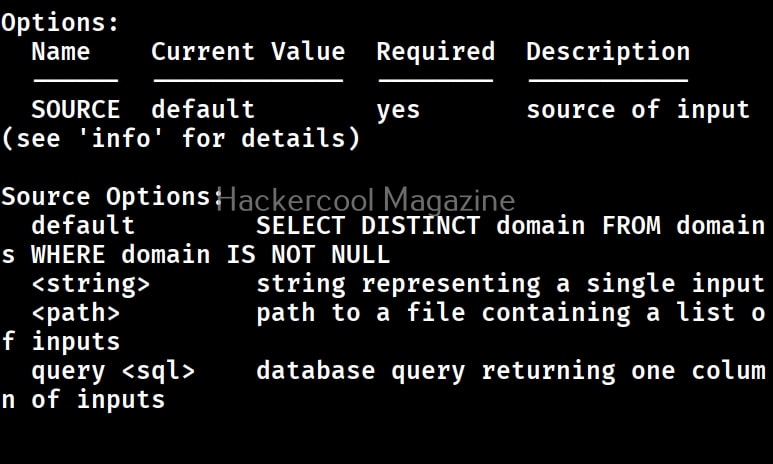
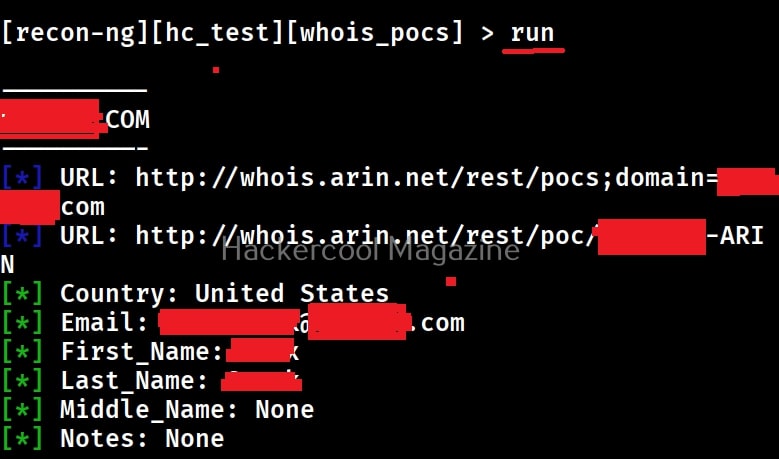
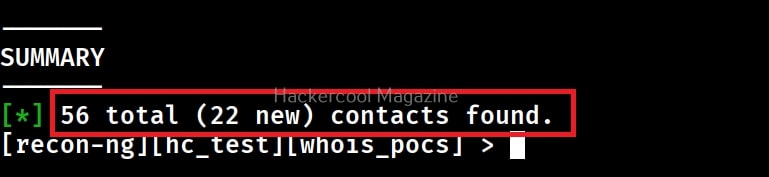
- Reconnaissance: After seeing the goal, the next step involves gathering as much information about the target organization such as public records, information available in social media and any other source. Needless to say, the acquired information should assist in the next step.
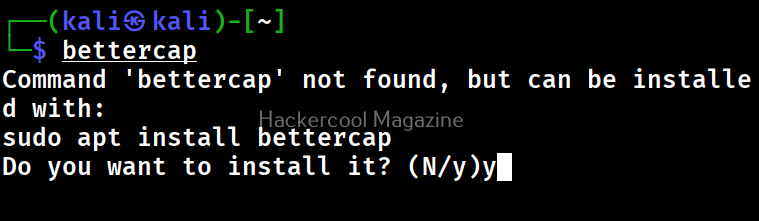
- Initial access: Gaining initial access to the target organization either by using phishing, malware or by exploiting a vulnerability.
- Privilege escalation: After gaining initial access, elevating privileges from a low-privileged user account to higher-level access is the next step.
- Lateral movement: Once, high privileges are acquired, the next step is to pivot through the target network to reach valuable assets.
- Completing objective: Achieving the goal of the operation such as data exfiltration, domain control or persistence.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Importance of Red Teaming
The primary objective of Red Teaming is not just to gain initial access but to demonstrate the potential impact of a successful breach. This helps organizations to,
- Identify real-world risks: By emulating actual adversaries, Red Teams reveal how a breach could happen in real-world, not just in theory.
- Improve detection and response – Red Team exercises highlight gaps in monitoring and response, allowing organizations to improve their security operations.
- Test assumptions – Many organizations overestimate their defensive capabilities. Red Teaming provides a reality check.
- Enhance training – These exercises serve as hands-on experience for defenders, offering invaluable lessons that go beyond textbooks and simulations.
- Validate controls – Red Teaming puts controls like firewalls, IDS, IPS etc to the test.
Red Teaming vs Penetration Testing
Although they are often used interchangeably, Red Teaming and penetration testing have a lot of differences. They are,
Red Team vs Blue Team
In cybersecurity, just like “Red Team” there is another team called “Blue Team”. While “Red Team” represents the attackers, “Blue Team” represents the defenders—the organization’s internal security staff. In some scenarios, there is also a “Purple Team” that acts as a bridge between “Red Team” and “Blue Team”, facilitating communication and helping both sides learn from the exercise.
While penetration testing is great for uncovering known vulnerabilities in systems, Red Teaming is about thinking like an attacker and exploiting weaknesses across the organization in a stealthy, goal-oriented way.
Ethical and Legal considerations
Red Teaming, just like penetration testing must be conducted under strict rules of engagement (ROE). These rules define what is and isn’t allowed, ensuring that the simulation doesn’t disrupt business operations or violate legal or ethical boundaries. Consent from senior leadership is essential, and the results must be handled with confidentiality and care. Next, learn about Blue teaming.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply