Hello, aspiring Ethical Hackers. In our previous blogpost on Footprinting, you learnt that hackers gather information about their targets using search engines. In this blogpost you will learn about Google Hacking or Google Dorking. Who doesn’t know what Google is. Just for this article’s sake, let me define what it is. Google is the most popular Search Engine that provides answers for anything we want, almost anything. Just a click away.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
Google is already an awesome search engine but to make the search engine more precise it has some advanced operators. In other words, searching with some special operators allows Google to provide exact information we want. These are known as Google Dorks. The basic syntax of a Google Dork is,
Operator : term to search or URL
Ex: intitle:hackercool
Some of the important Google operators are.
- intitle
- allintitle
- inurl
- related
- allintext
- cache
- define
- allinurl
- intext
- site
Let’s learn about each of them in detail.
1. intitle
This query will return all the webpages which have term “hackercool” in the title of the webpage.
2. allintitle
Same as “intitle” but will show pages containing all the multiple keywords specified.
3. inurl
The “inurl” query returns all the webpages containing the specified keywords in their URL.
4. allinurl
Same as “inurl” but can be used to search for multiple keywords in the URL.
5. define
The “define” query can be used to search for a definition of any keyword you specify. For example, let’s search for the definition of hackercoolmagazine.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
6. related
The “related” dork of Google is used to search for a website similar to the site you specify.
For example, in the above image, we search for sites related to Facebook and Google has returned similar networking sites like Twitter, Pinterest, LinkedIN. Note that this google dorks only takes websites as keywords.
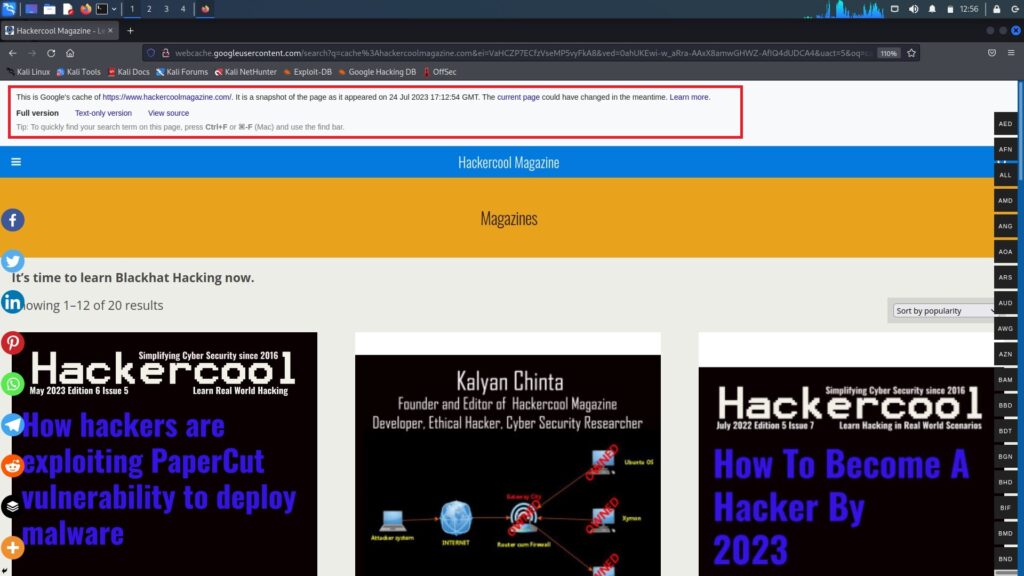
7. cache
The cache query returns the latest cached version of the website Google has stored. This dork too needs website as keyword.
8. intext
The “intext” query returns all the webpages having like specified “text” in their content.
9. allintext
The “allintext” query is same as “intext” but can be used to search webpages having multiple keywords in their content.
10. site
The “site” query is useful in limiting your search to a particular website.
Read Part 2 of Google Hacking.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply