Hello aspiring Ethical Hackers. In our previous blogpost, footprinting guide, you lave learnt what is footprinting and various types of footprinting techniques. In this article, you will learn in detail about WHOIS footprinting.
If you’re starting your journey in ethical hacking, one of the easiest and most powerful skills you can learn is WHOIS footprinting. It’s simple, beginner-friendly and gives you valuable information about a target without doing anything risky. In my opinion, Whois footprinting is the first method of footprinting that should be used while starting information gathering.
In this guide, you’ll learn:
- What WHOIS footprinting is
- Why it’s important
- How to do it step by step
- What to look for as a beginner
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What is WHOIS?
WHOIS is actually a protocol running on port 43. When you or any organization register a domain (eg: example.com), a record is created. This record is known as WHOIS record and is created by an organization called Internet Corporation for Assigned Names and Numbers (ICANN) which regulates domain name registration and ownership. WHOIS records are maintained by Regional Internet Registries (RIR’s). At present, there are five RIR’s allocated to specific regions.
- American Registry for Internet Numbers (ARIN)
- African Network Information Center (AFRINIC)
- Asia Pacific Network Information Center (APNIC)
- Reseaux IP Europeens Network Coordination Centre (RIPE)
- Latin American and Caribbean Network Information Center (LACNIC)
What is WHOIS Footprinting?
WHOIS footprinting is the process of collecting information about a domain name using WHOIS databases. As already explained, every website (like example.com) is registered somewhere and that registration contains details.
Using WHOIS, you can find:
- Domain owner (although sometimes hidden)
- Registration and expiry dates
- Name servers
- Registrar details
In simple terms: WHOIS tells you who owns a website and how it’s set up.
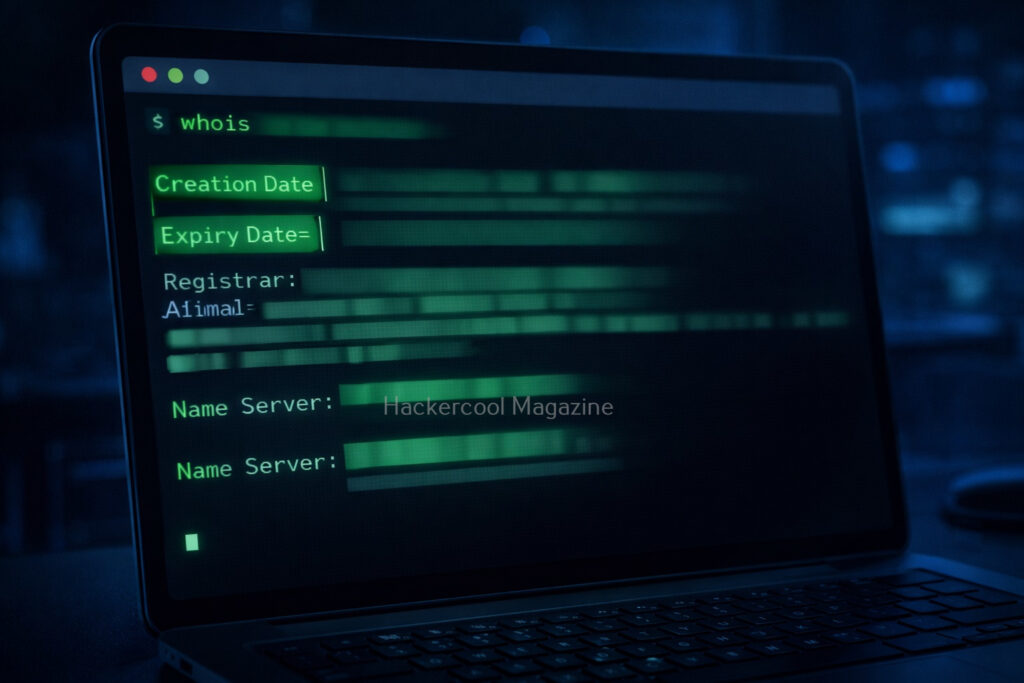
What information does WHOIS reveal?
When you run a WHOIS lookup, you’ll see a lot of data. Let’s simplify the important parts for you.
1. Creation Date:
Shows when the domain was registered. This reveals if the domain is older or new. This is important because older domains may have:
- Legacy systems
- Outdated security
2. Expiry Date:
This tells you when the domain will expire. Expired domains can sometimes be,
- Re-registered
- Misused
3. Registrar:
This gives you information about the company where the domain is registered. Examples of some domain registrars are GoDaddy, Namecheap etc.
4. Name Servers:
Nameservers are specialized servers within the DNS that act as the internet’s phonebook, translating human-readable domain names (e.g., example.com) into numerical IP addresses (e.g., 192.0.2.1). These tell you where DNS is managed. This information is Important for understanding:
- Hosting setup
- Infrastructure
5. Registrant Information:
This gives you information about the person or entity who registered the domain. It may include:
- Name
- Organization
However, in most cases it is hidden due to privacy protection.
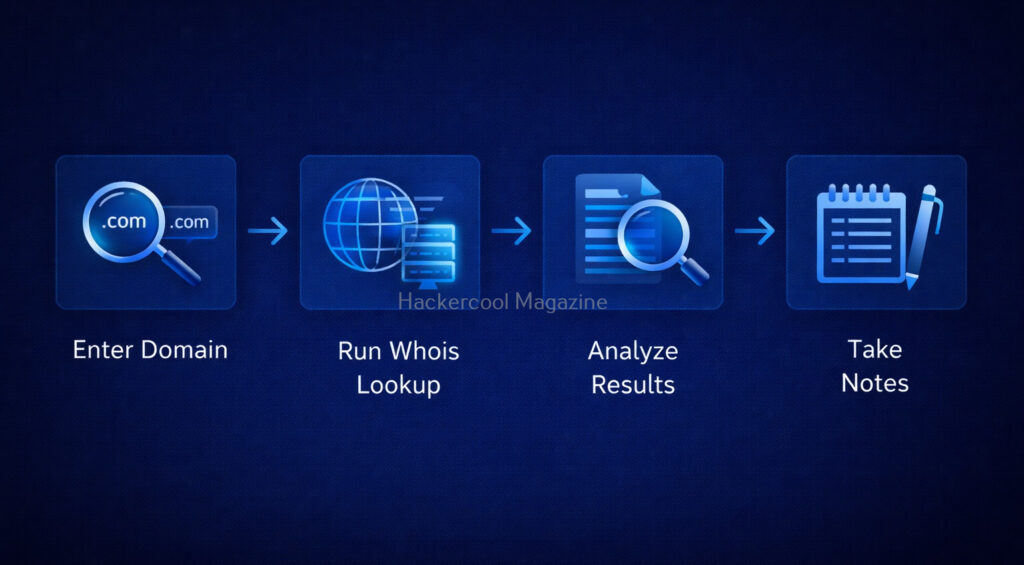
How to Perform WHOIS Footprinting (Step-by-Step)?
Let’s look at step-by-step process of performing WHOIS Footprinting.
Step 1: Choose a Target Domain
Start with something simple like your own website or a test domain. Remember, always stay within legal boundaries.
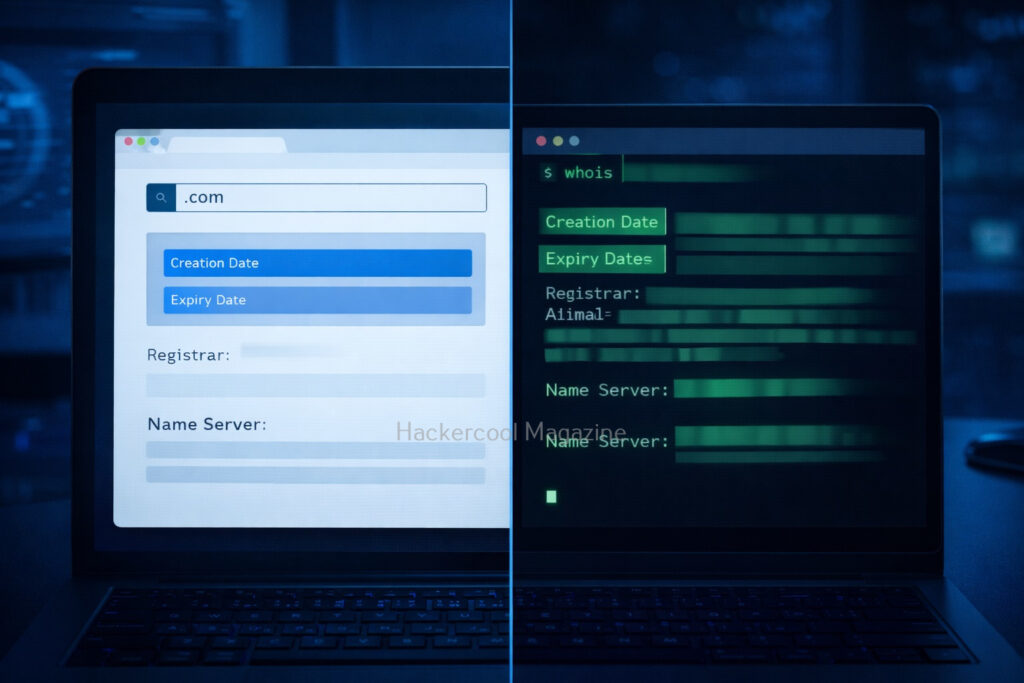
Step 2: Use a WHOIS Lookup Tool
Do a simple Google search for WHOIS Lookup tools. Not only there are many tools for this but also there are many online services providing this service.
Step 3: Enter the Domain Name
Once you select a tool or service, enter the domain name. For example,
example.com
- example.com
Then, run the lookup.
Step 4: Analyze the Results
The lookup runs and displays the results. After the results are out, analyze the results. Focus on:
- Registration dates
- Name servers
- Registrar
Don’t try to understand everything at once.
Step 5: Take Notes
It is a very good practice to take notes in your journey of ethical hacking. Write down:
- Interesting findings
- Patterns
This helps you build investigation skills.
Let’s see a simple example of what you might discover after performing WHOIS lookup. From a simple WHOIS lookup of a domain, you might find:
- The domain is 10 years old
- It uses specific name servers
- The registrar is a known provider
What does it tell you? This tells you that infrastructure might follow certain patterns. The system may be stable but possibly outdated.
How to Use WHOIS Effectively?
Here’s how you can use WHOIS more effectively.
1. Look for Patterns:
Always Check for:
- Similar domains
- Same name servers
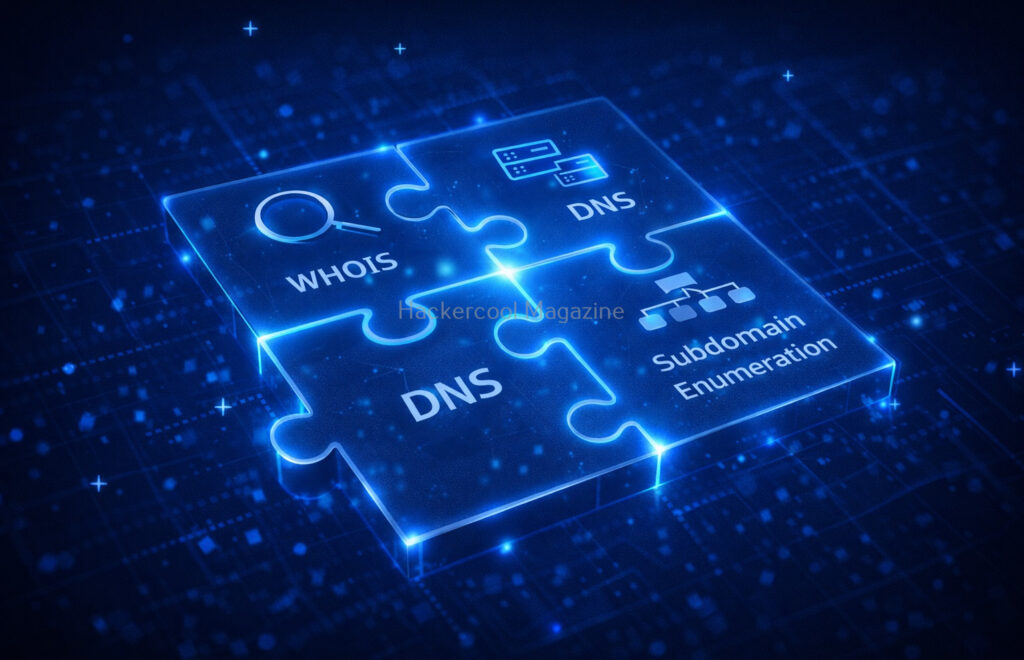
2. Combine with Other Techniques:
WHOIS footprinting in itself will not give you complete information about the target domain. It is best to combine WHOIS with:
- DNS footprinting
- Google searching
3. Practice Regularly:
Try WHOIS on:
- Different websites
- Practice labs
Tools for WHOIS Footprinting
You will not need complex tools to perform WHOIS Lookup as a beginner. You can start with:
- Online WHOIS lookup websites like whois.com, who.is.com etc
- Linux whois command
- Sysinternals Whois command utility for Windows.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Why is WHOIS Important in Ethical Hacking?
With all said and done how to perform WHOIS footprinting, let’s see the importance of this in ethical hacking. WHOIS is often the first step in reconnaissance (footprinting). Here’s why it matters:
1. Understand the Target:
You get basic information about:
- Your target organization
- Their Domain structure
2. Discover Infrastructure Clues:
WHOIS can reveal information about:
- Hosting providers
- Name servers
This information helps you map the system.
3. Find Related Assets:
In some cases, it helps you to identify other domains owned by the same organization.
4. Detect Weak Points:
In some cases, it can reveal weak points in an organization. Old domains or misconfigured records can indicate poor security practices.
Common Mistakes Beginners Make
Many beginners make some common miastakes while performing this footprinting. Please avoid these mistakes.
1. Expecting Too Much Data:
If fotprinting is the first stage of ethical hacking, then WHOIS footprinting is the first stage of footprinting itself. So, may be due to excitement or something else, beginners expect too much data to be revealed. But this may not be the case in real-world. Many domains use privacy protection. Don’t worry, this is normal.
2. Ignoring Small Details:
In footprinting, even minute details matter. Even simple data like name servers can be useful.
3. Not connecting collected information:
WHOIS is just one piece of the puzzle. Combine it with:
- DNS analysis
- Subdomain discovery
4. Skipping Documentation:
Always write down your findings.
Legal & Ethical Reminder
WHOIS footprinting is generally safe but you must still follow some rules.
Never and NEVER:
- Use information obtained through WHOIS for illegal purposes
- Target systems without permission
Always:
- Practice ethically
- Stay within legal limits
Conclusion
WHOIS footprinting is one of the simplest and most powerful starting points in ethical hacking. It teaches you how to:
- Gather information
- Analyze systems
- Think like an investigator
And the best part? You can start learning it today with zero risk.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply