Hello, aspiring Cyber Forensic Investigators. In our previous blogpost on Computer Forensics, you learnt what is Imaging and its importance. In this article, you will learn about Guymager, a tool used for reliable disk imaging.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
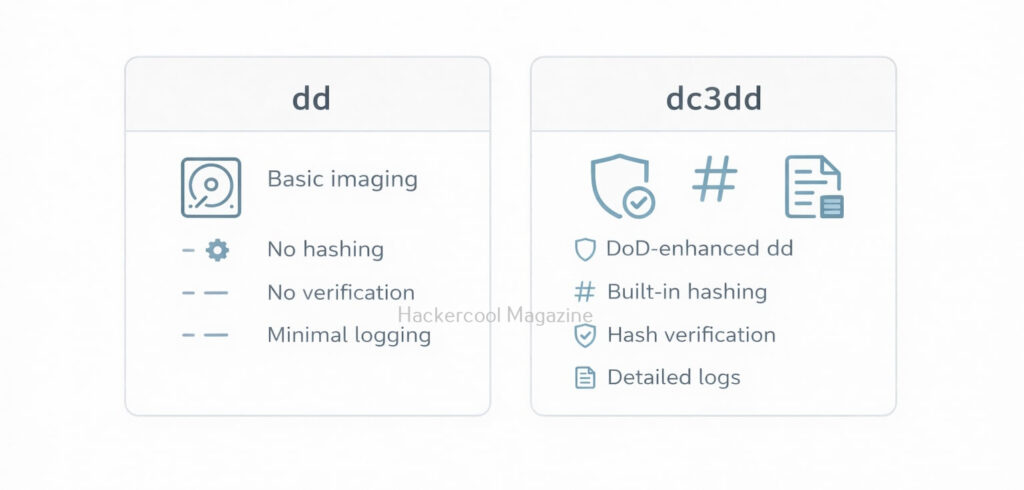
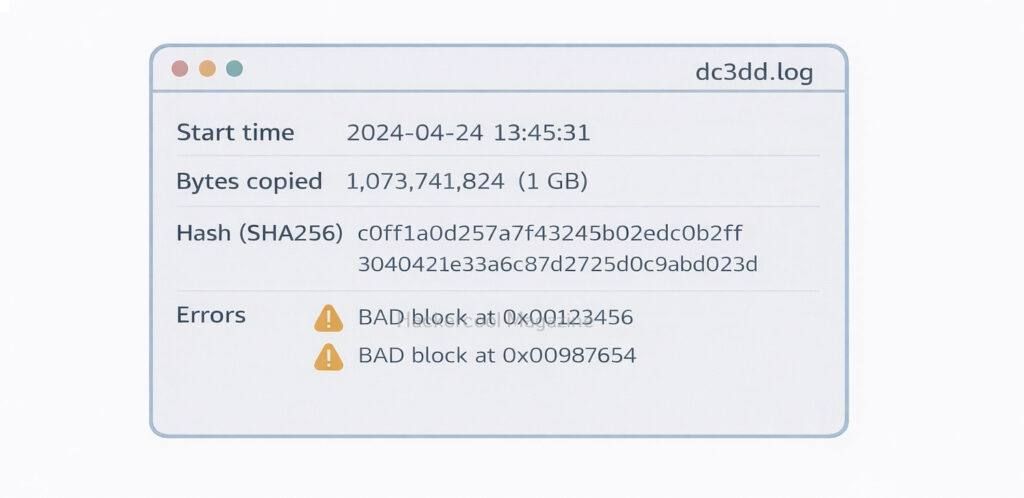
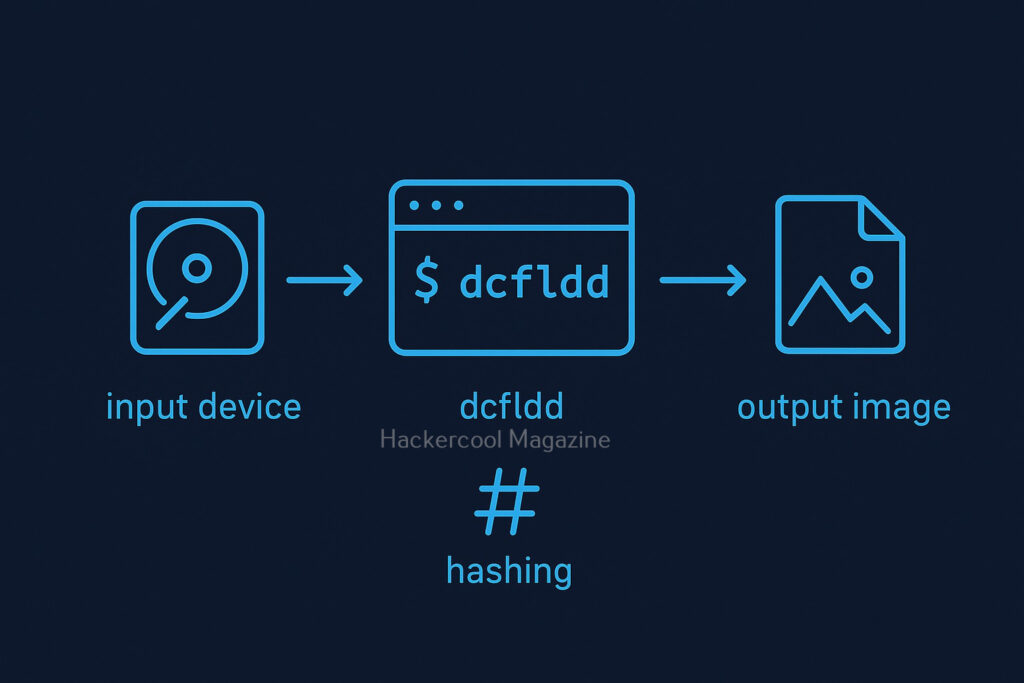
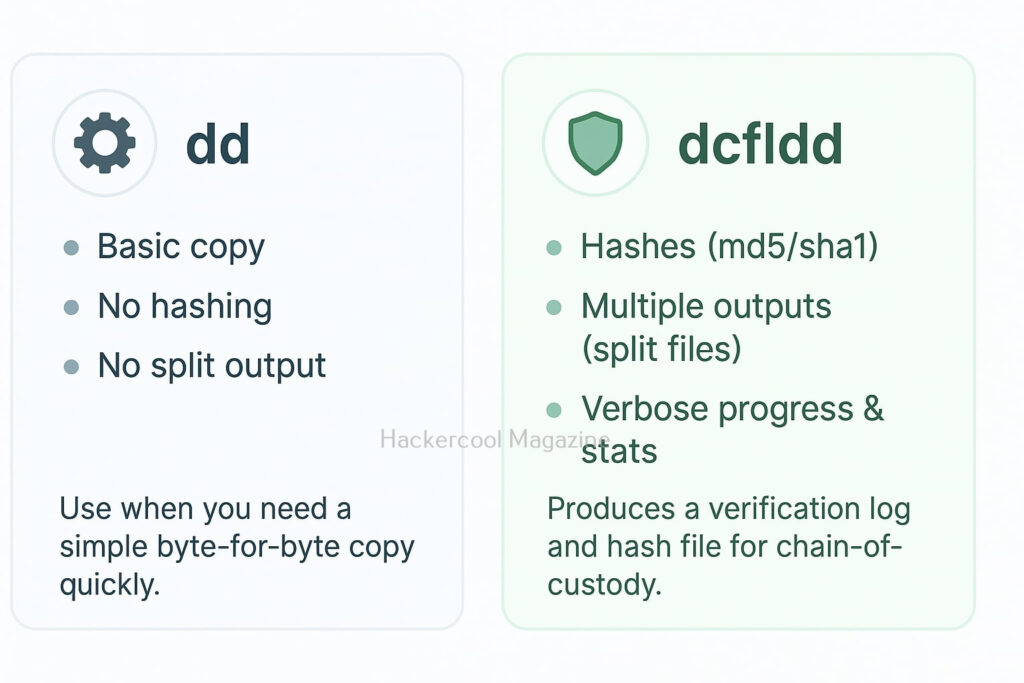
When it comes to digital forensics, few tools are as clean, fast and beginner-friendly as Guymager. Unlike command-line imaging tools such as dd, dcfldd or dc3dd, Guymager provides a powerful graphical interface, making it perfect for new forensic investigators who want to perform reliable evidence acquisition with minimal complexity. Despite its simplicity, Guymager is highly respected in professional labs for its speed, hashing accuracy, detailed logging and support for common forensic image formats.
In this blog post, we’ll break down what Guymager is, why it’s used in digital forensics and how beginners can start using it including sample commands and workflows.
What is Guymager?
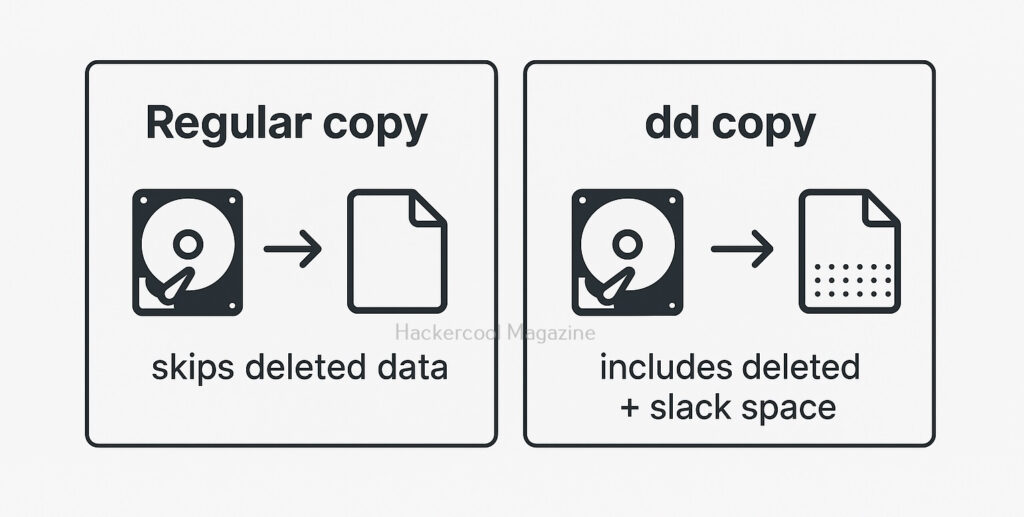
Guymager is an open-source forensic imaging tool for Linux, designed to create exact clones of storage devices while preserving integrity. It is widely used for:
- Creating forensic disk images
- Hashing drives with MD5, SHA-1, SHA-256
- Performing bit-for-bit cloning
- Generating detailed acquisition logs
- Producing EWF (E01), AFF, or Raw (.dd) images
Its user-friendly GUI makes it suitable for students, interns and analysts who are new to imaging procedures.
Why Use Guymager?
Here are the main reasons forensic teams rely on Guymager:
1. Graphical Interface
Being a GUI tool, there is no need to memorize long commands while using this tool. Simply select the drive, choose an output format and start imaging.
2. Very Fast Imaging Engine
Guymager is optimized for multi-threading and often outperforms traditional imaging tools.
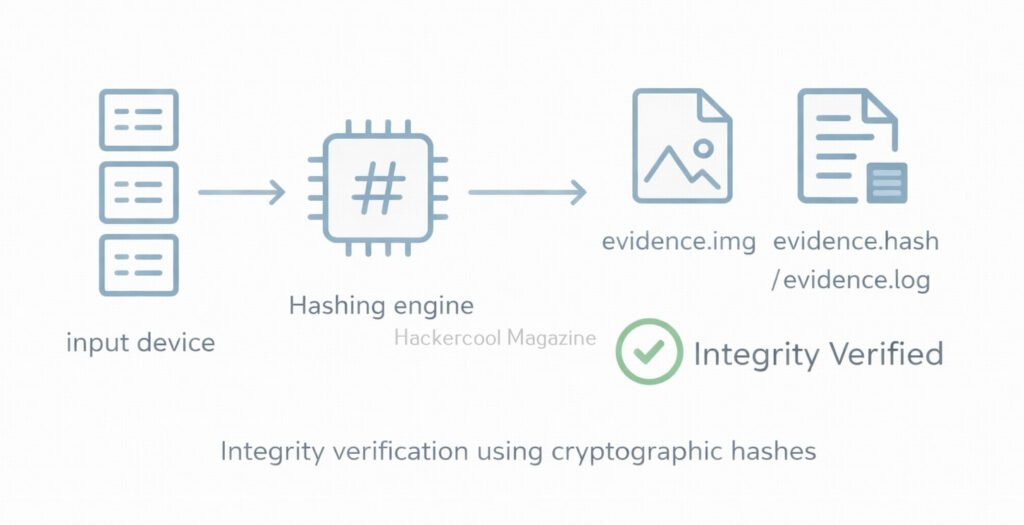
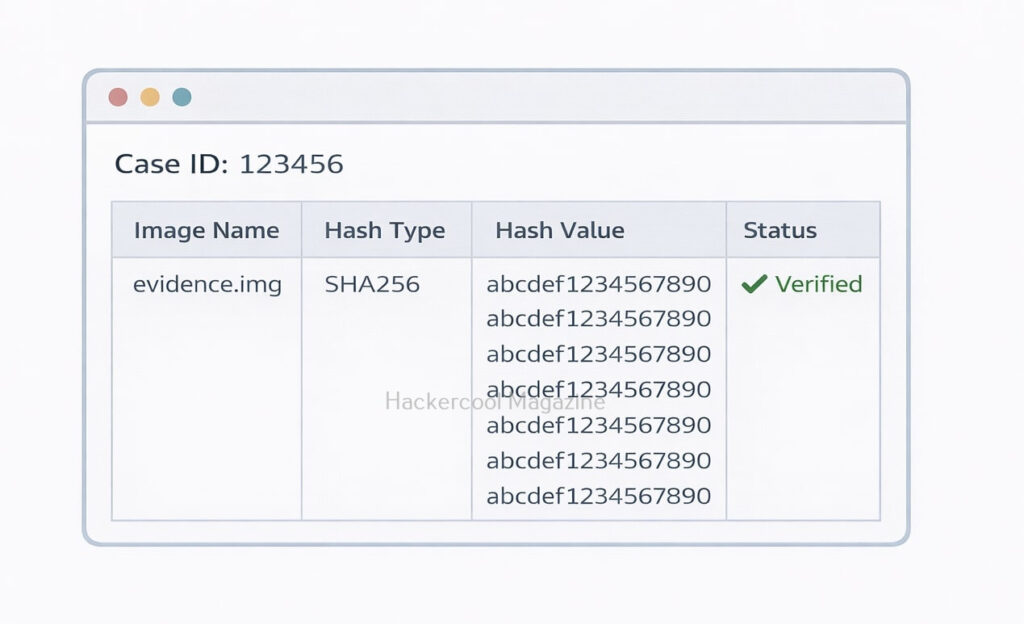
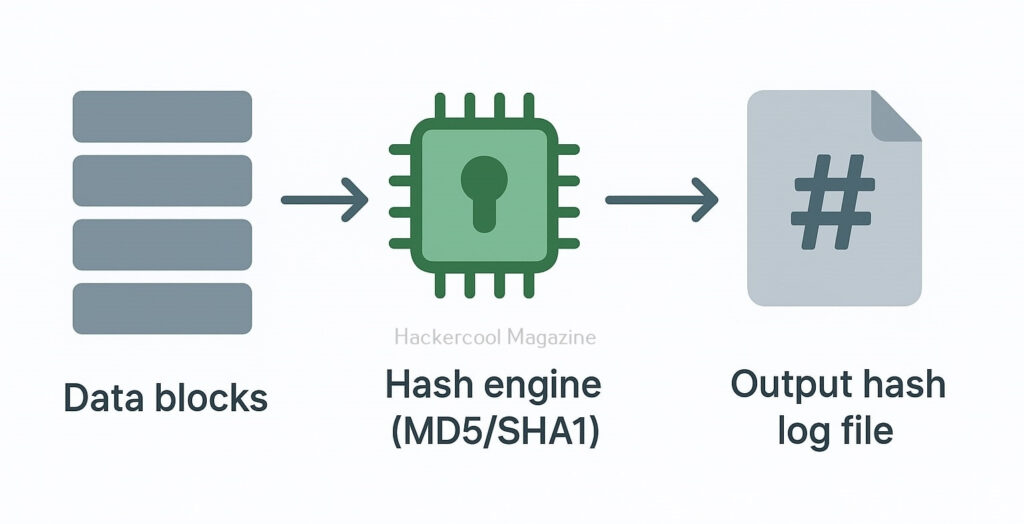
3. Automatic Hashing and Logging
Every image created comes with:
- Pre- and post-imaging hashes
- Complete logs of the imaging session
- Information about the device metadata
4. Supports Write-Blocking
Guymager automatically prevents writes to the source drive when used with hardware write blockers.
5. Stable, Trusted and Open-Source
Frequently found in forensic Linux distros like DEFT, CAINE, and Kali Linux.
Installing Guymager
On most Linux systems (Debian, Ubuntu, Kali), you can install this tool using commands shown below.
sudo apt update
sudo apt install guymager
You can start this tool using command shown below.
sudo guymager
Running as root is necessary because Guymager interacts directly with disk devices.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Step-by-Step Guide to use this tool
STEP 1: Launch the Tool
After starting guymager, the GUI will open and automatically scan for available devices.
It displays:
- Device name (e.g.,
/dev/sdc) - Size
- Serial number
- File system information (if available)
- Read-only status
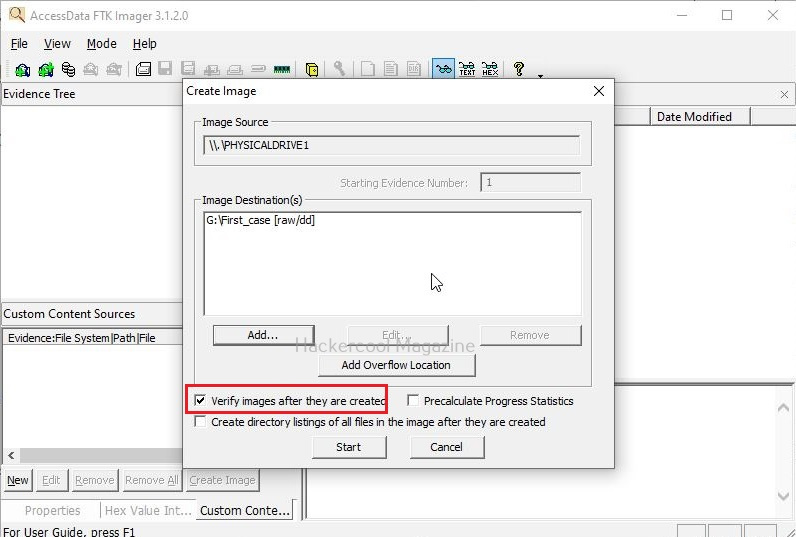
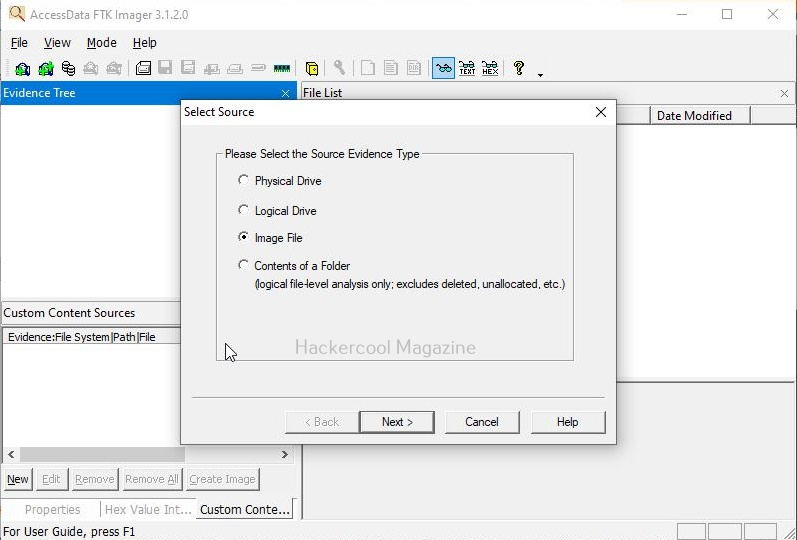
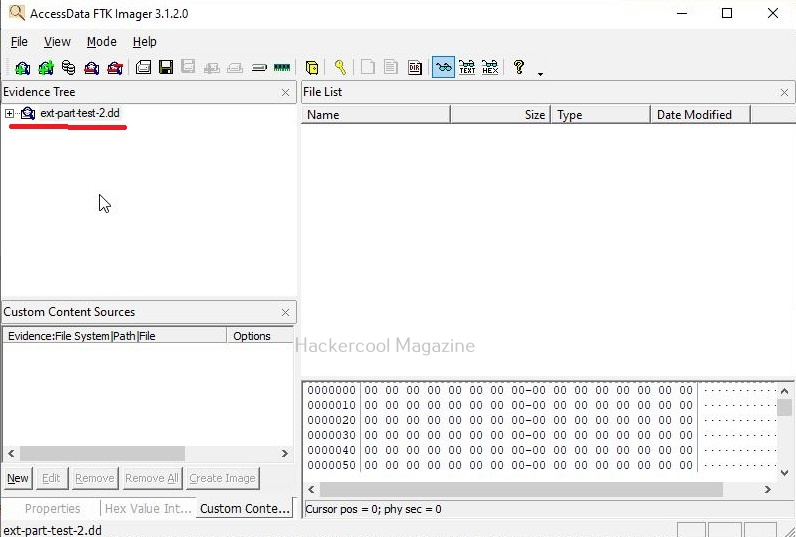
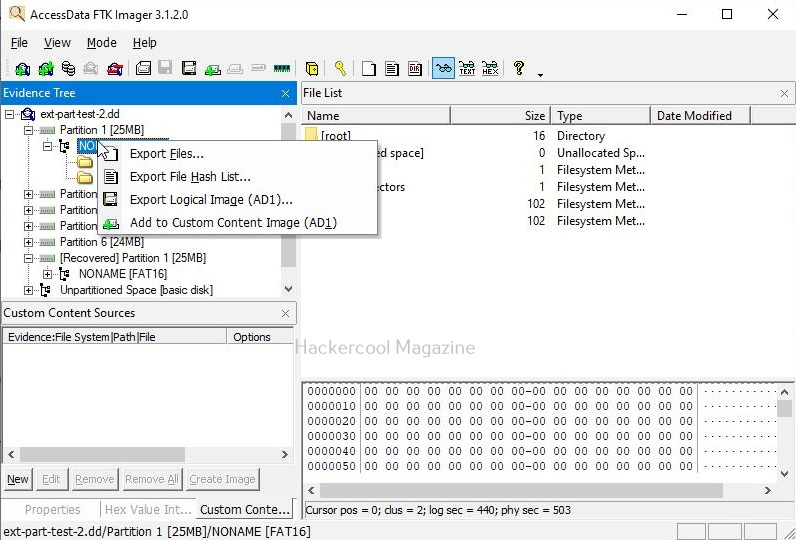
STEP 2: Select the Drive to Image
Right-click on the device and choose “Acquire Image”.
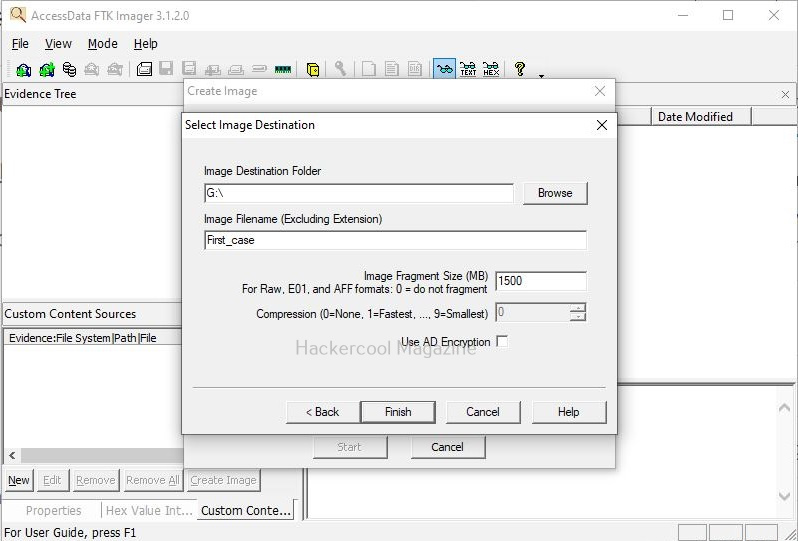
Now pick:
- Output format (EWF-E01, AFF, RAW)
- Output directory
- Case metadata (optional but recommended)
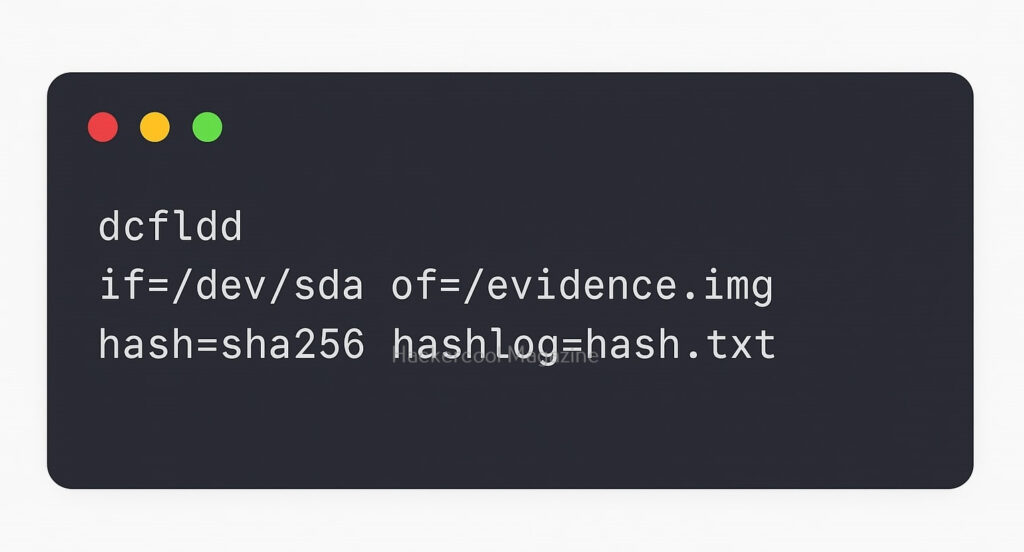
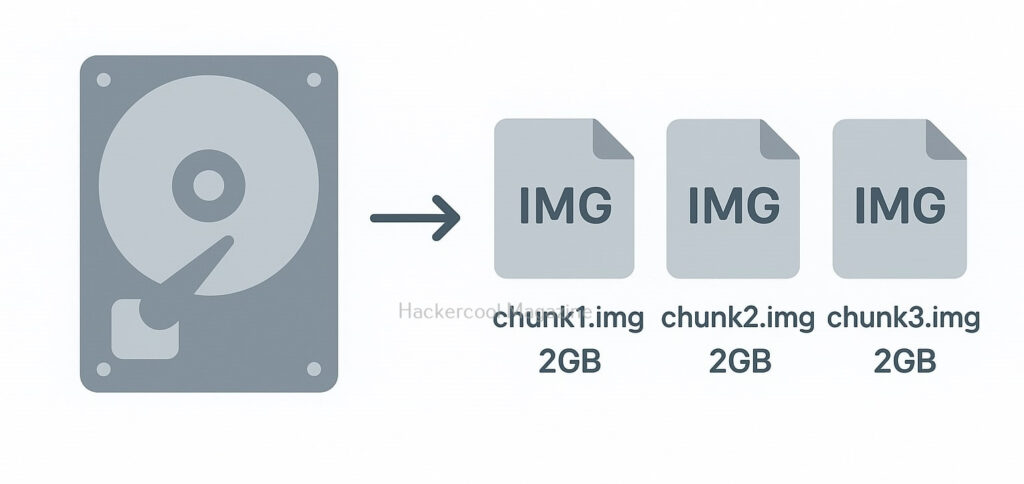
STEP 3: Configure Imaging Options
You can enable:
- MD5 / SHA-1 / SHA-256 hashing
- Compression (for E01 images)
- Segment size
- Automatic log creation
For beginners, the default settings are usually enoigh.
STEP 4: Start Imaging
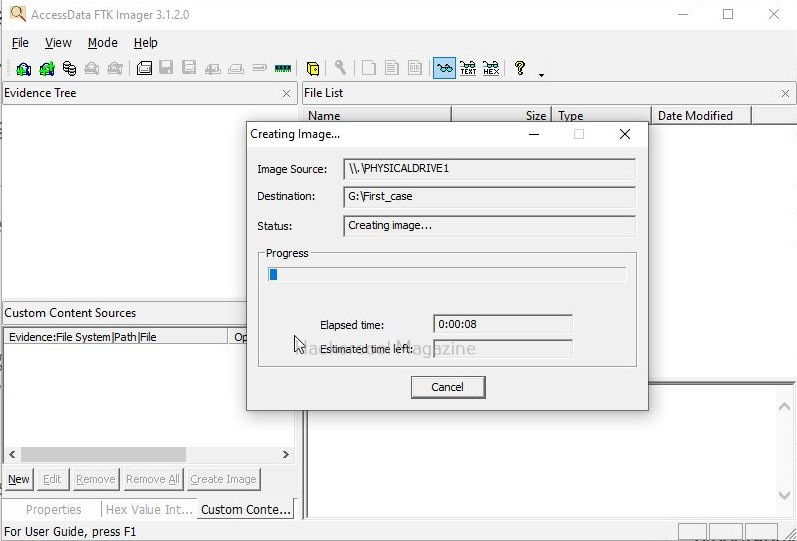
Click on “Start”.
Guymager will display:
- Imaging speed
- Remaining time
- Hash values
- Log progress
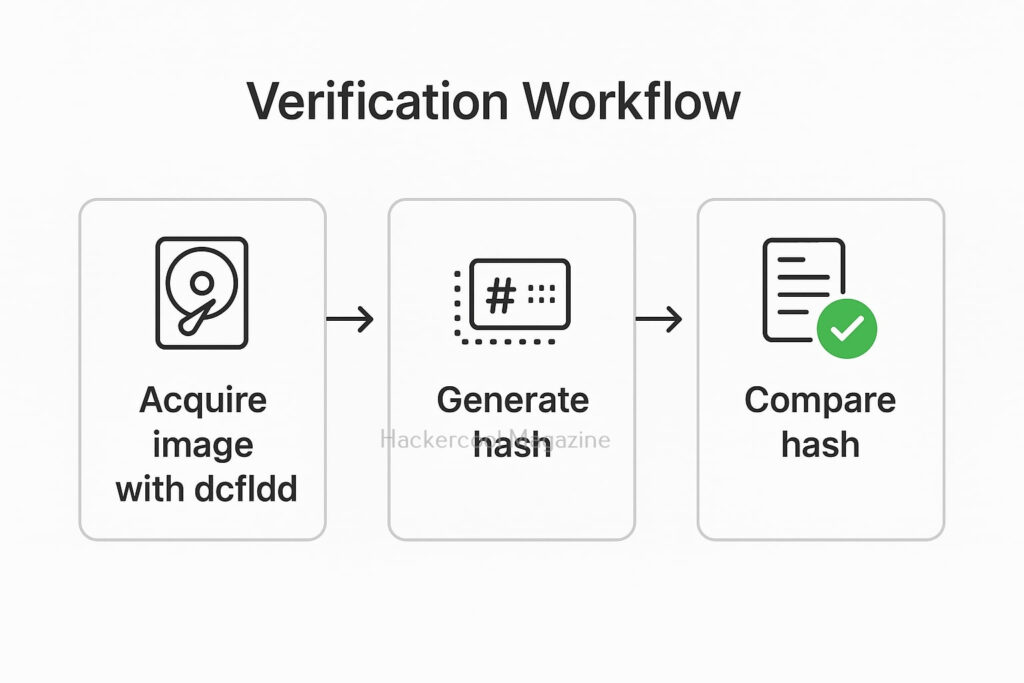
When complete, the tool verifies the image by comparing pre- and post-acquisition hashes.
Useful Commands for Beginners
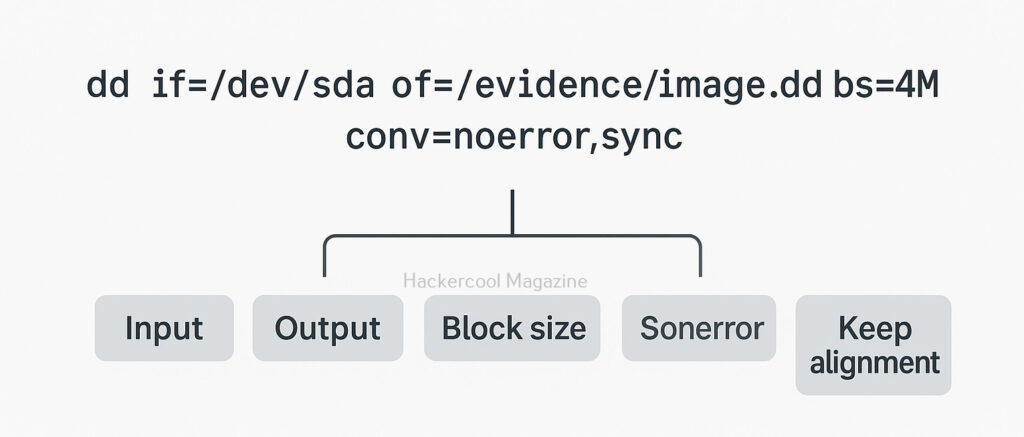
Even though Guymager is GUI-based, you can still interact with imaging results using standard Linux commands. Here are some useful commands for beginners while interacting with this tool.
1. Verify Image Hashes
If you choose RAW imaging (.dd), you can verify the image using:
md5sum image.dd
sha256sum image.dd
2. Mounting the Forensic Image (Read-Only)
You can mount the forenisc image with Guymager using command shown below.
sudo mount -o loop,ro image.dd /mnt/image
3. Viewing Logs
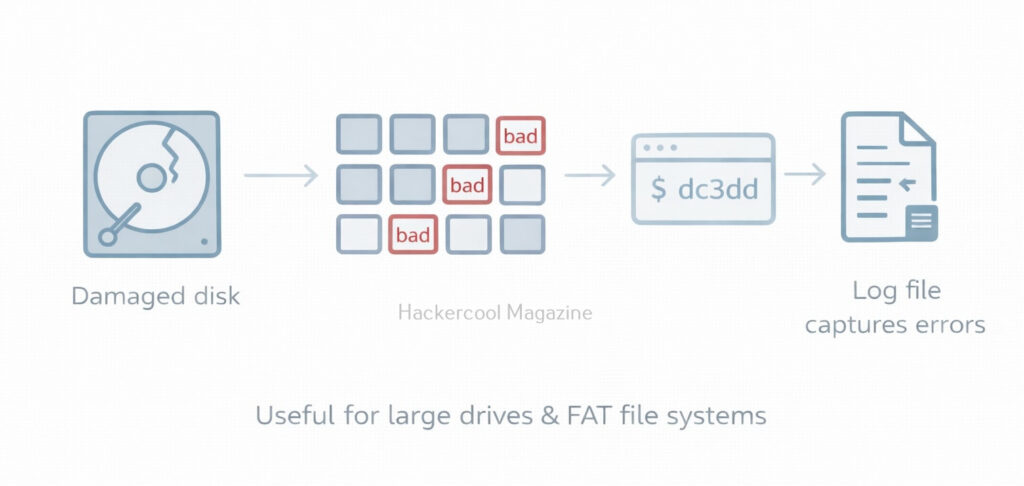
While using this tool, each imaging session generates a .log file. You can view this log file using command shown below.
cat case123.log
4. Checking information about Acquired Image (E01 Format)
You can view information belonging to the acquired Forensic Image by using ewf tools as shown below.
Install ewf-tools:
sudo apt install ewf-tools
Then view metadata:
ewfinfo evidence.E01
Beginner Tips for using Guymager
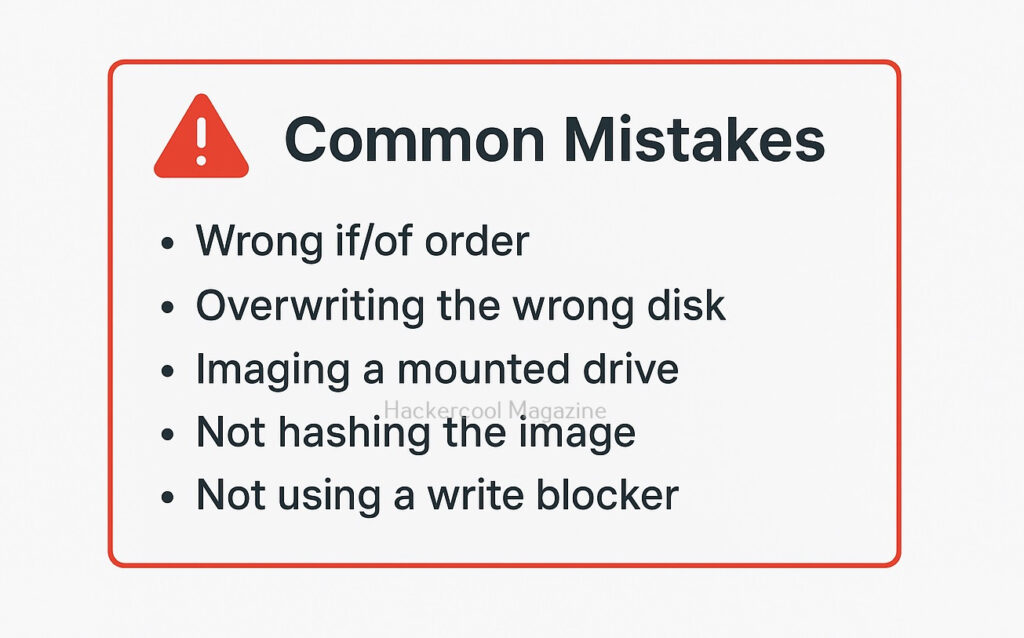
1. Always use a Write Blocker:
Always and always use a Write Blocker while using this tool. This ensures the original evidence drive is never modified.
2. Save Images on a Different Drive:
Never store the forensic image on the same drive you are imaging from.
3. Document Everything:
Always document everything about the Imaging process. Maintain a record of the Case number, device details, serial numbers, hash values etc. Although Guymager logs help, you should always keep personal notes too.
4. Prefer E01 for Real Cases:
While using this tool for imaging in Real-world cases, always prefer E01 format. This format stores metadata, hashes and compression which is ideal for investigations.
5. Use RAW(.dd) format for Training:
Always prefer RAW (.dd) format for training. This is simpler, easier to mount and widely supported.
Conclusion
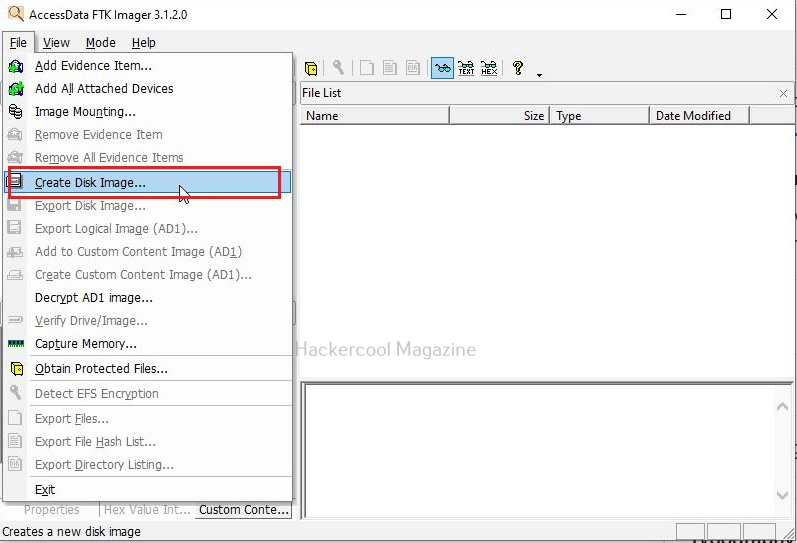
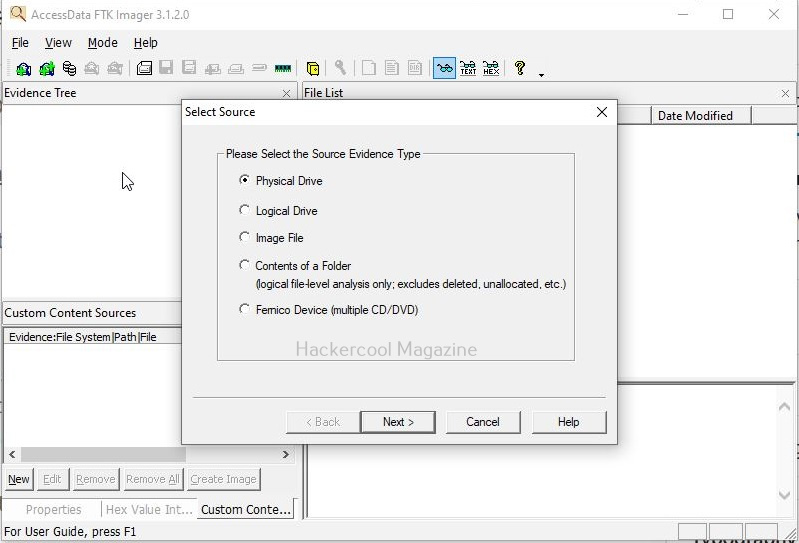
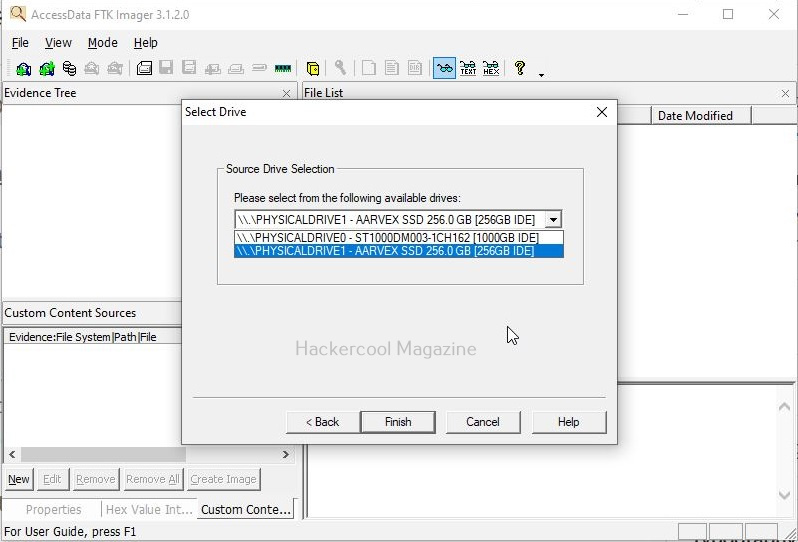
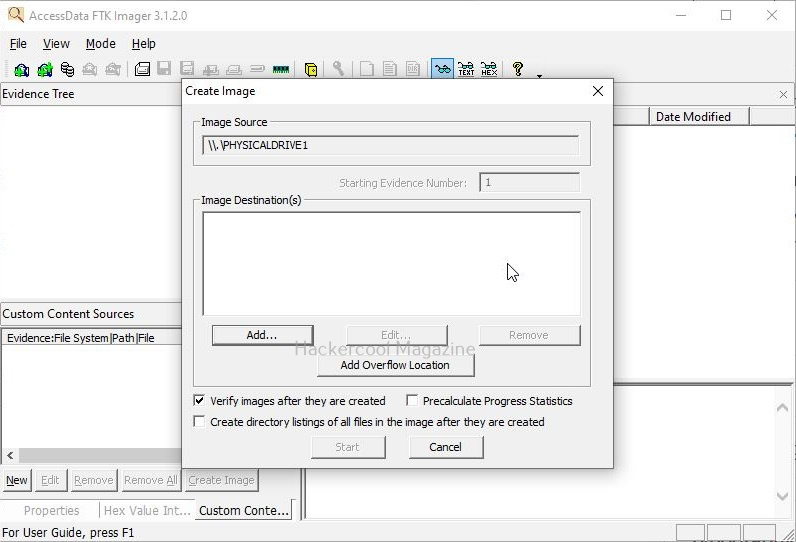
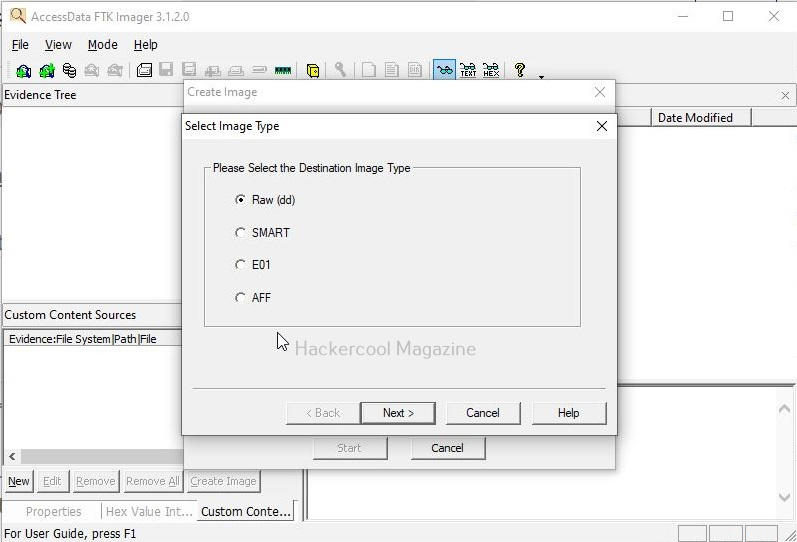
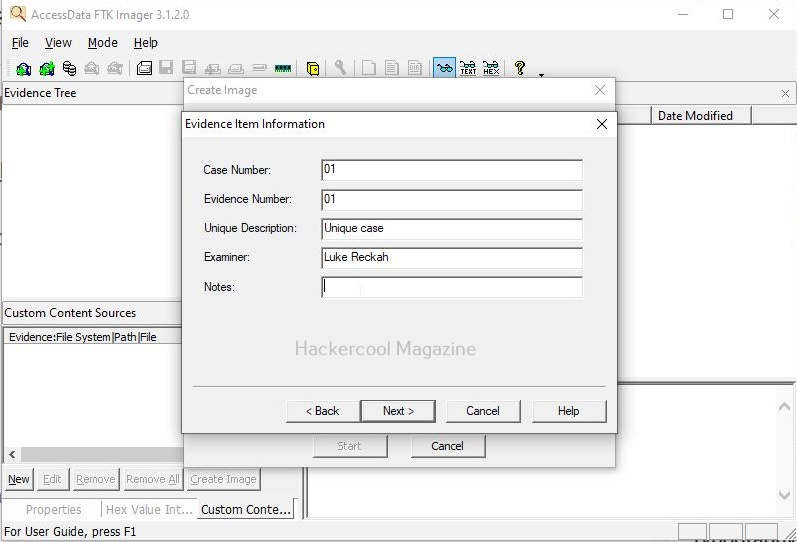
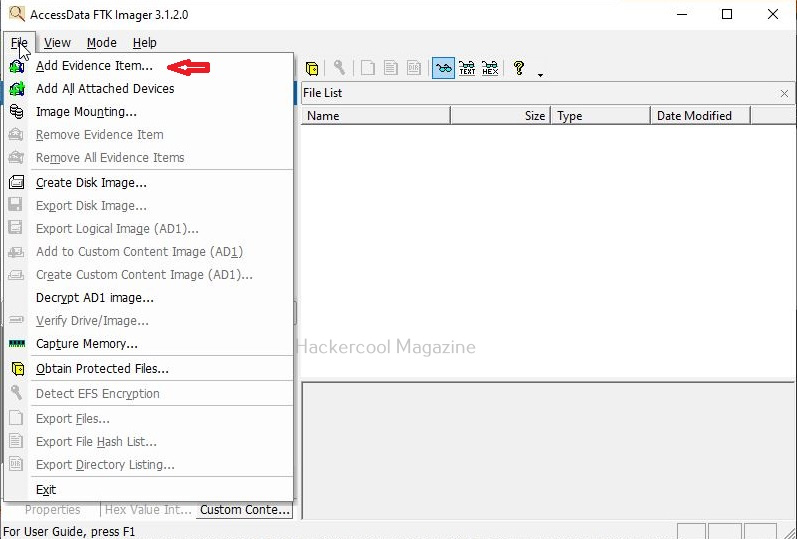
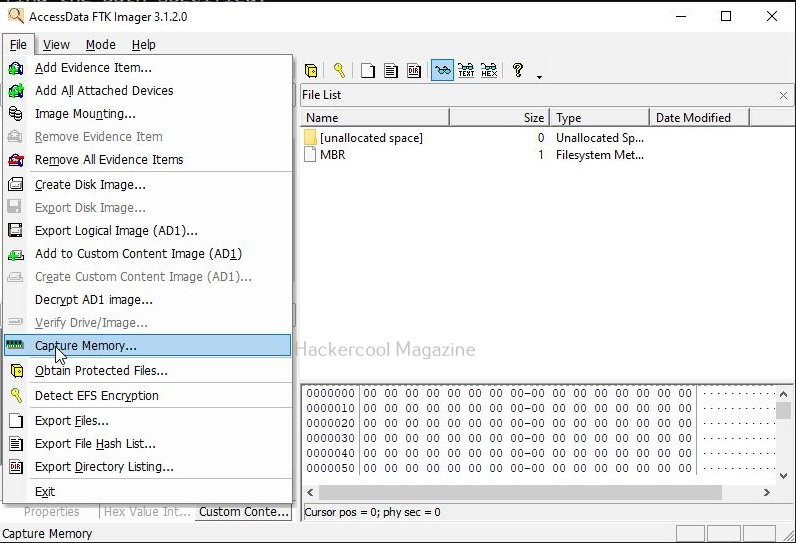
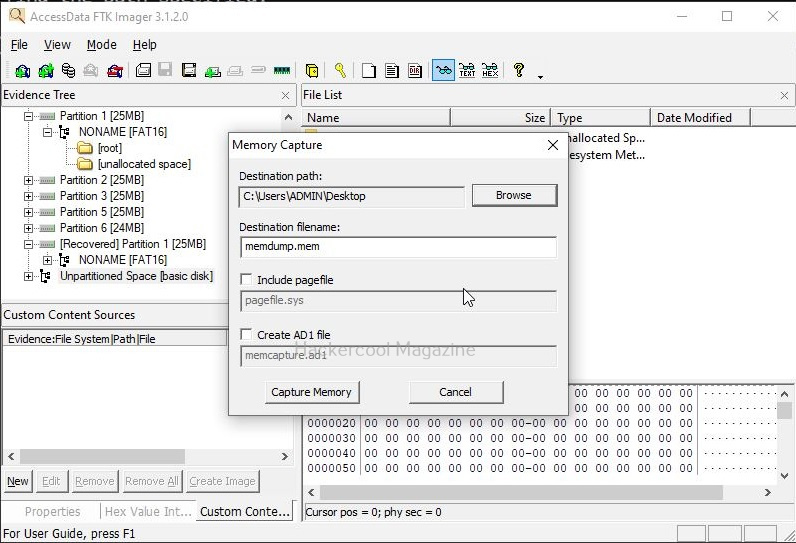
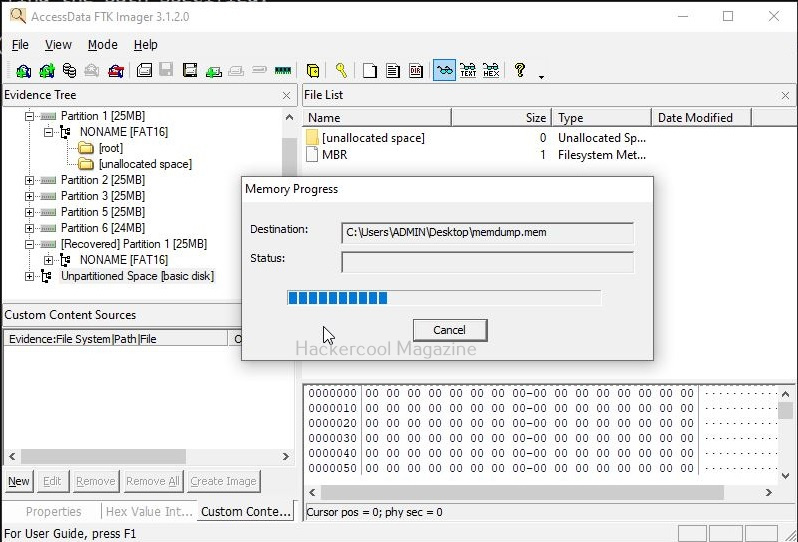
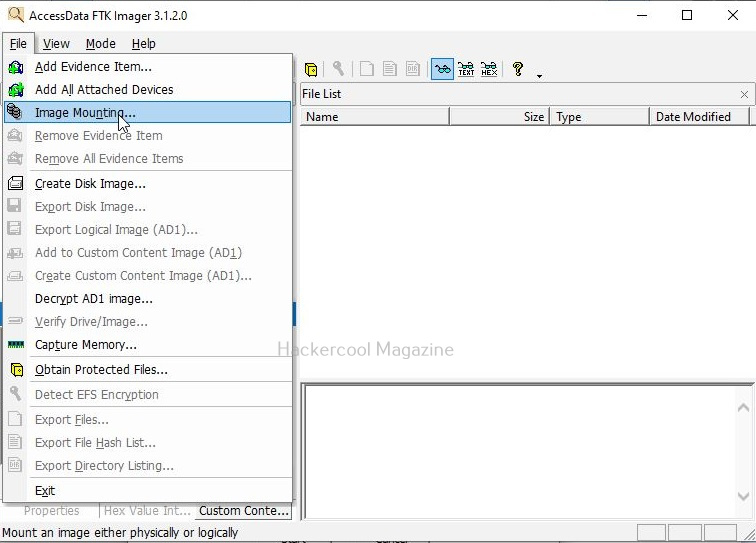
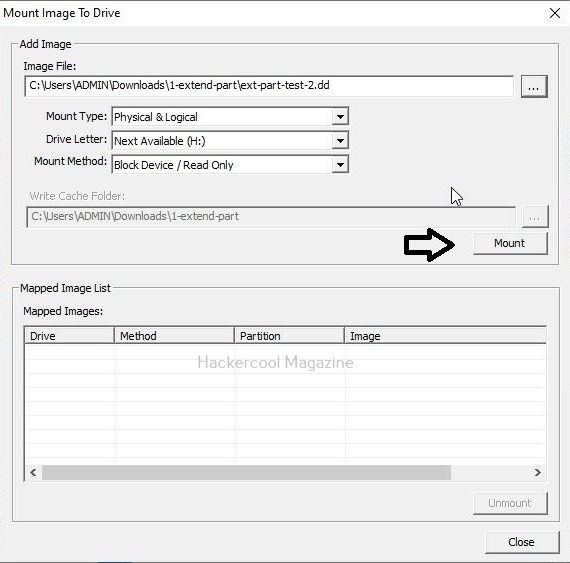
For beginners entering the field of digital forensics, Guymager is one of the easiest and most reliable tools for forensic imaging. Its fast performance, intuitive interface, automated hashing and comprehensive logging make it a favorite among forensic professionals and students alike. Next, learn how to acquire evidence using FTK Imager tool.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply