Hello aspiring ethical hackers. You have learnt what is phishing and about various phishing techniques in our previous blog posts. In this article, you will learn about GoPhish and how to perform Ethical Phishing simulations with it. Phishing remains one of the most effective cyberattack techniques, not because it’s technically advanced but because it targets people. Even with strong security controls in place, a single convincing email can lead to credential theft, malware execution or data loss. This is where GoPhish comes in.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
GoPhish is an open-source phishing simulation framework designed for ethical use only. Pen testers and red teamers use it to test user awareness, improve training programs and understand how real-world phishing campaigns succeed. For beginners, GoPhish offers a safe and structured way to learn how phishing works without harming real users or breaking the law.
What Is GoPhish?
GoPhish is a web-based platform that allows you to create, launch and track phishing campaigns in a controlled environment. Instead of sending malicious emails, GoPhish sends simulated phishing emails to test how users respond. With GoPhish, you can:
- Design phishing email templates
- Create fake landing pages
- Track who opens emails, clicks links or submits credentials
- Measure awareness and training effectiveness
The goal is education and defense.
Why GoPhish Is Popular?
GoPhish has become one of the most widely used phishing simulation tools for a few key reasons. They are,
1. Simple Web Interface:
You don’t need advanced coding skills whie using this tool. Everything from email templates to campaign reports is managed through a clean web dashboard.
2. Realistic Simulations:
GoPhish supports:
- HTML email templates
- Credential capture pages
- Custom domains
- Timing and scheduling
This allows campaigns to closely resemble real phishing attacks, which makes training more effective.
3. Open Source and Free:
There are no licensing costs. This makes GoPhish ideal for:
- Students
- Small security teams
- Labs and training environments
4. Strong Reporting:
GoPhish can track:
- Email delivery
- Opens
- Link clicks
- Form submissions
These metrics help organizations understand where users struggle and where training needs improvement.
How GoPhish Works?
GoPhish follows a straightforward campaign-based model.
STEP 1: Set Up Sending Profiles
A sending profile defines how emails are delivered. This includes:
- SMTP server details
- Sender name and address
In labs, this is often a test mail server or sandboxed environment.
STEP 2: Create Email Templates
Templates control what the phishing email looks like. You can simulate:
- Password reset notices
- Invoice alerts
- HR messages
- Security warnings
Templates support HTML, allowing realistic formatting.
STEP 3: Build Landing Pages
Landing pages simulate login portals or warning pages. These pages can:
- Capture entered credentials
- Redirect users after submission
- Display training messages
Captured data is stored securely within GoPhish for analysis.
STEP 4: Define Users and Groups
You specify the targets which are usually test accounts or consenting employees. Users can be grouped by department or role to analyze trends.
STEP 5: Launch the Campaign
Once everything is configured, you schedule the campaign. GoPhish handles delivery and tracking automatically.
STEP 6: Review Results
The dashboard displays:
- Who opened the email
- Who clicked the link
- Who submitted credentials
This data helps identify risky behaviors and training gaps.
Practical Walkthrough
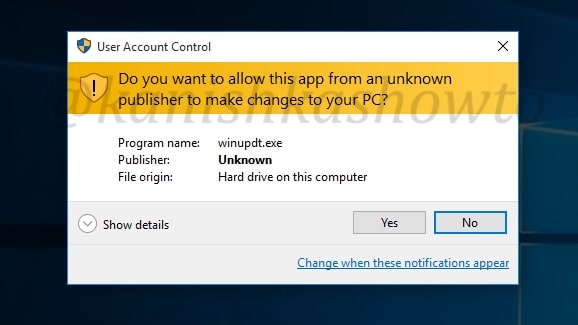
Let’s see the working of GoPhish practically. For this, we have installed GoPhish on Windows. You can download it from here. Once downloaded, open CMD window and navigate to the directory where “ghophish.exe” executable is and run it as shown below.
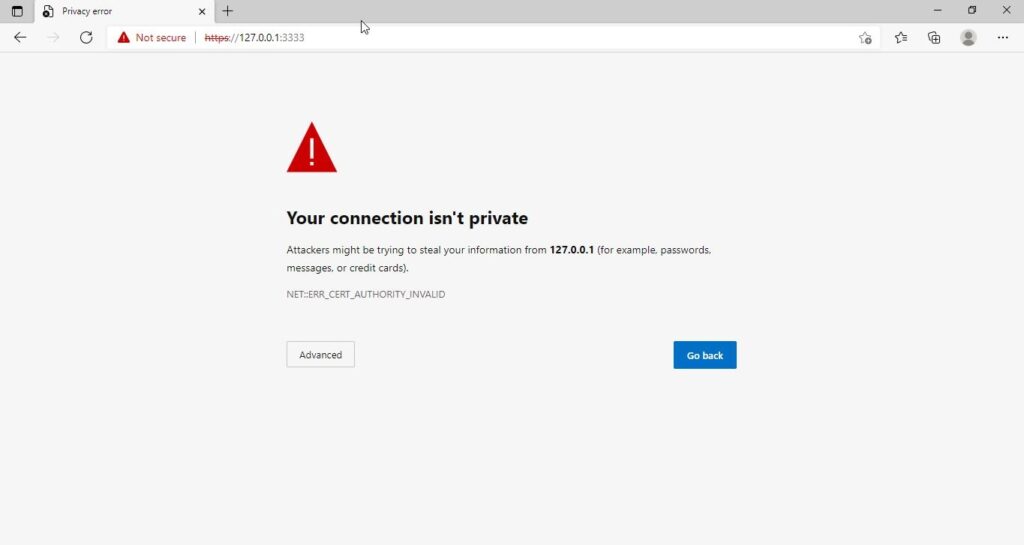
After executing, If you observe the CMD window, you will find the username and password for the Gophish dashboard. This part is highlighted in the image above. These credentials are needed to login into the Gophish dashboard. Keep the CMD window open, Open Browser and enter address https://127.0.0.1:3333. This is the default port on which Gophish runs. If you get any certificate error, click on advanced to bypass it and then enter the above mentioned credentials.
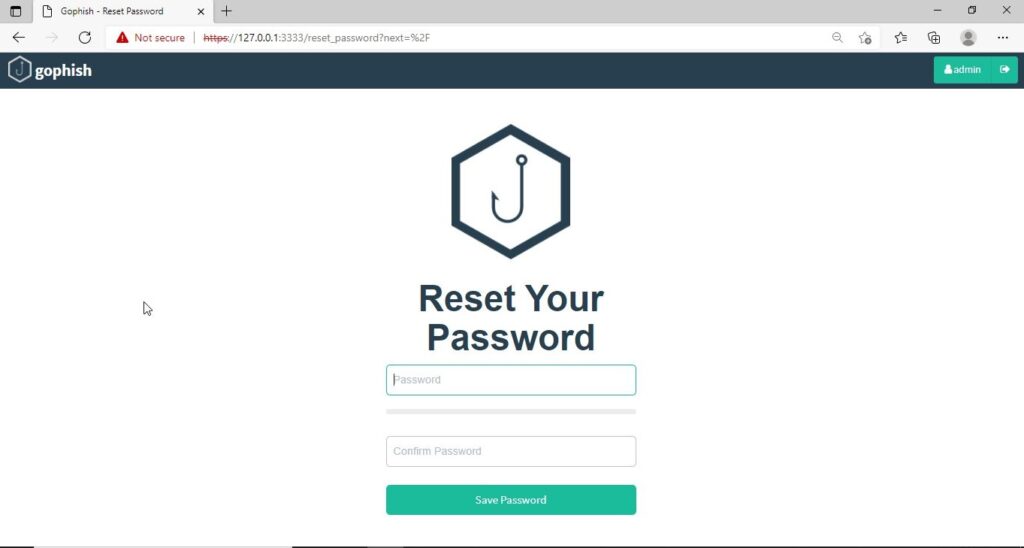
The first thing you will see after logging in is that the system prompts you to reset your password. Reset the password.
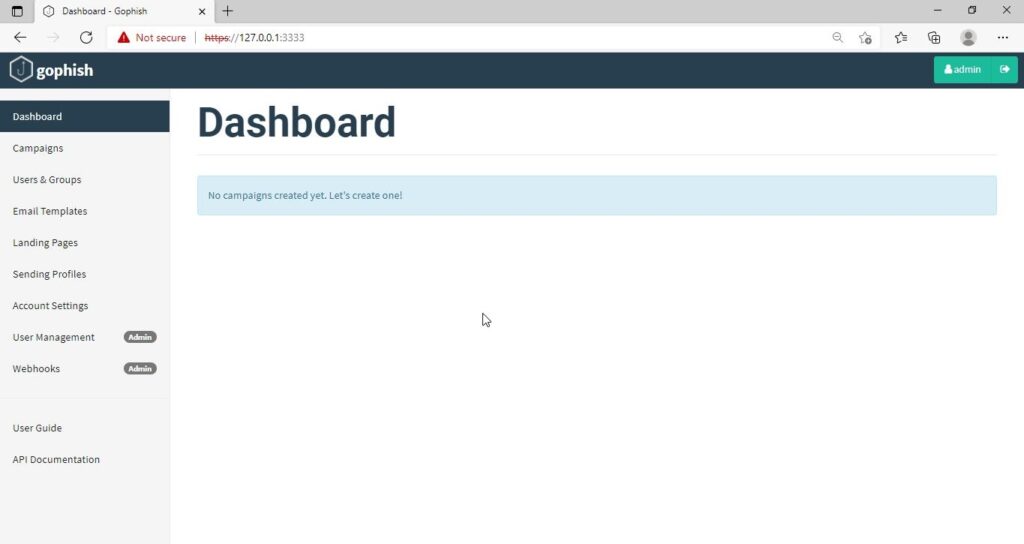
Now, you can access the Gophish dashboard.
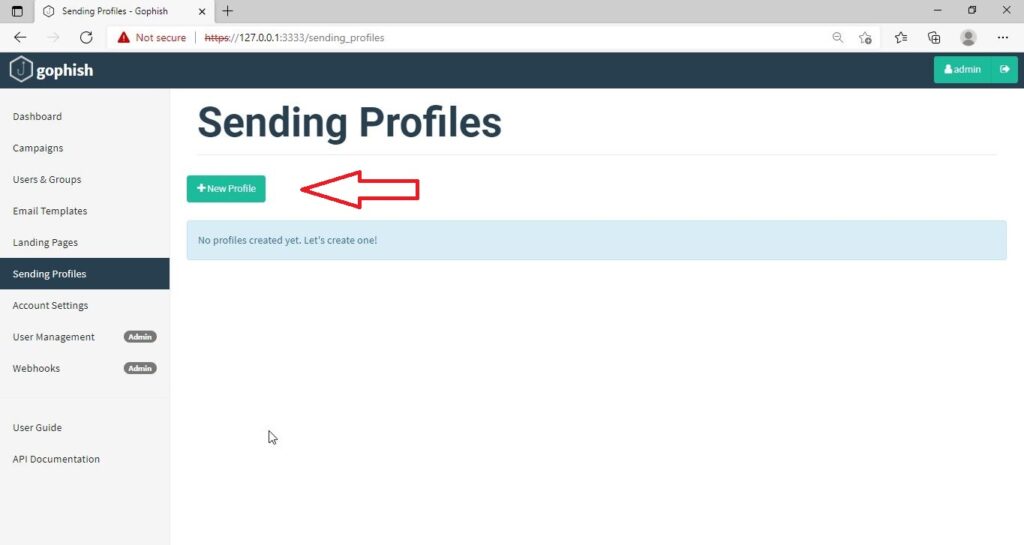
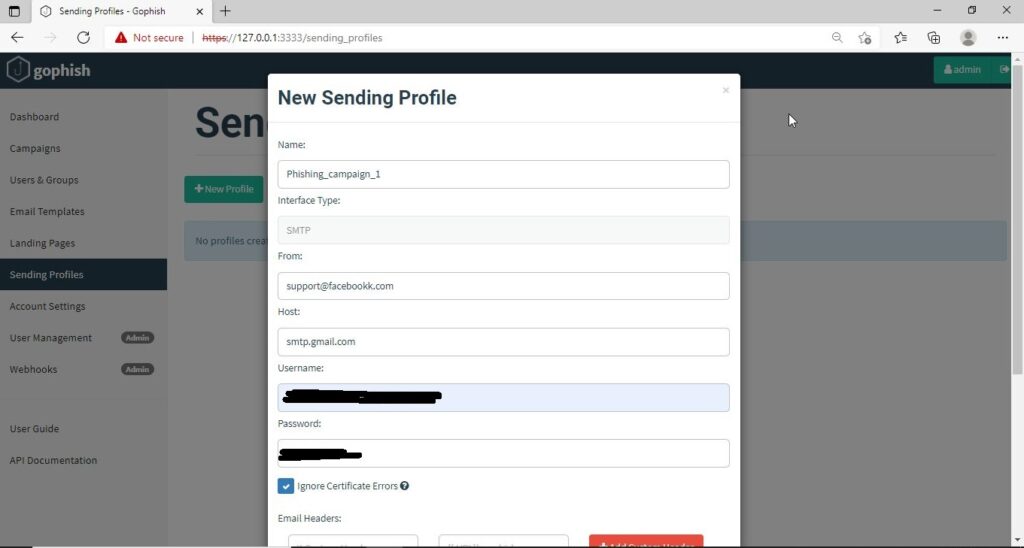
The first thing we need to do is create a “Sender Profile”. This is the mail address from which the spear phishing email comes from.
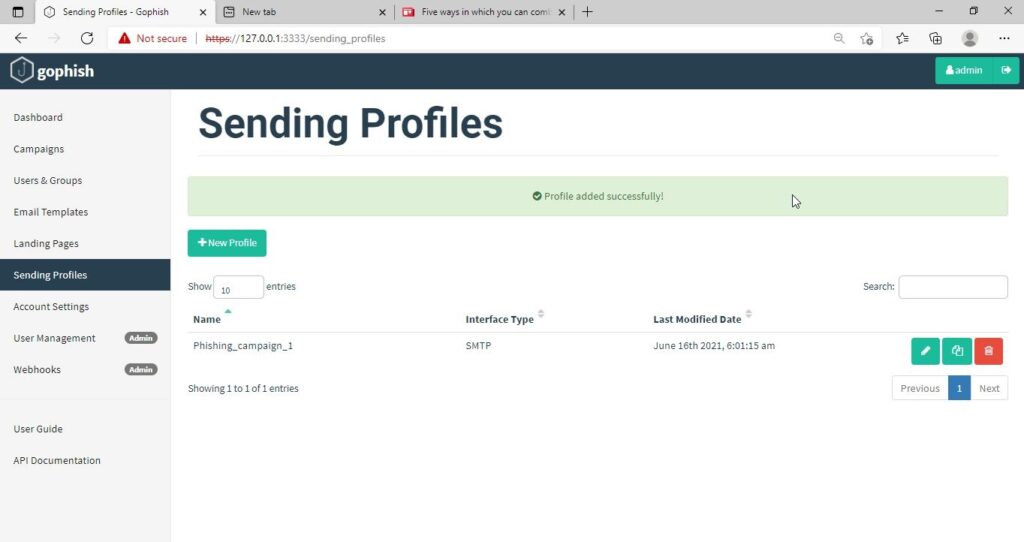
Click on “Sending profiles” tab and then click on “New profile” to create a new Sending Profile. Set the options for the sending profile. For example, we set the name for this as “phishing campaign 1”. To send any type of email, we’ll need a SMTP server. For this tutorial, I will be using the SMTP server of Gmail as I will be sending an email from Gmail. In Real world phishing attacks and even in many phishing simulations, a new domain is created and the email is sent from that domain’s mail to make the phishing email appear genuine. The username is the Gmail username and password is Gmail password.
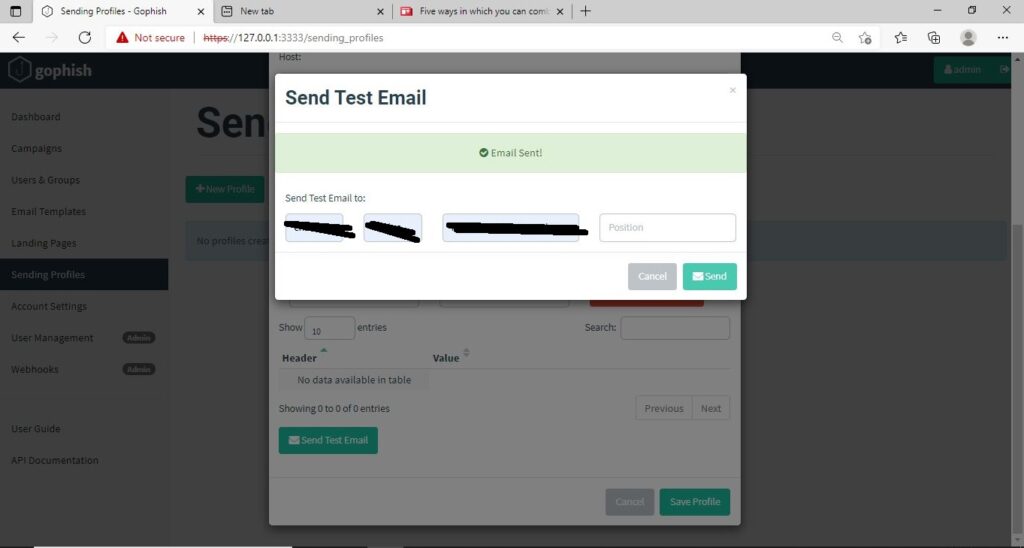
Save the changes. Send a test email to the email of your choice to see if the Phishing email appears as you want it to be.
The username we specify is very important here as it will be displayed. So it has to be made as convincing as possible. Once you are satisfied with the sending profile, you can save it.
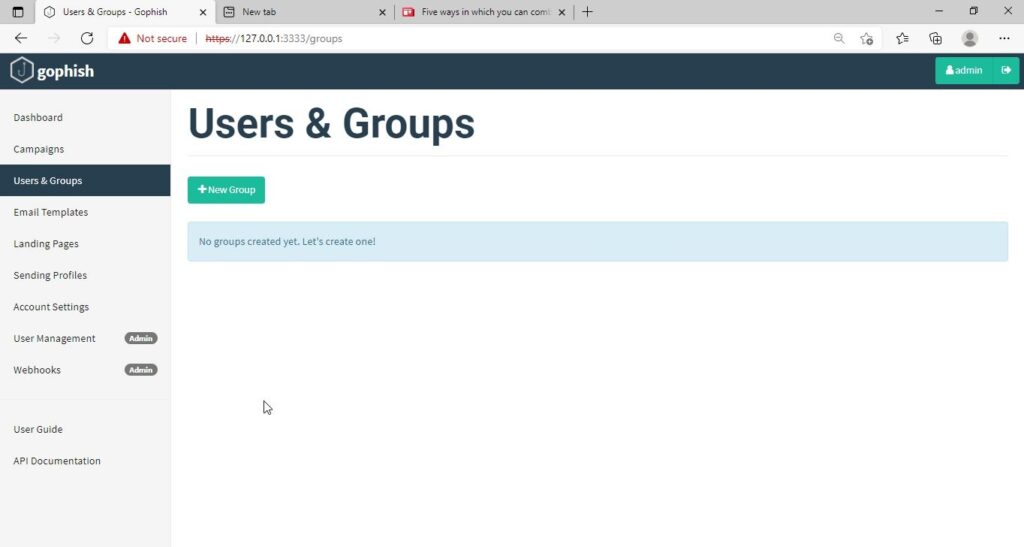
Next, we need to create Users and Groups. This is where we assign target users for of our phishing campaign.
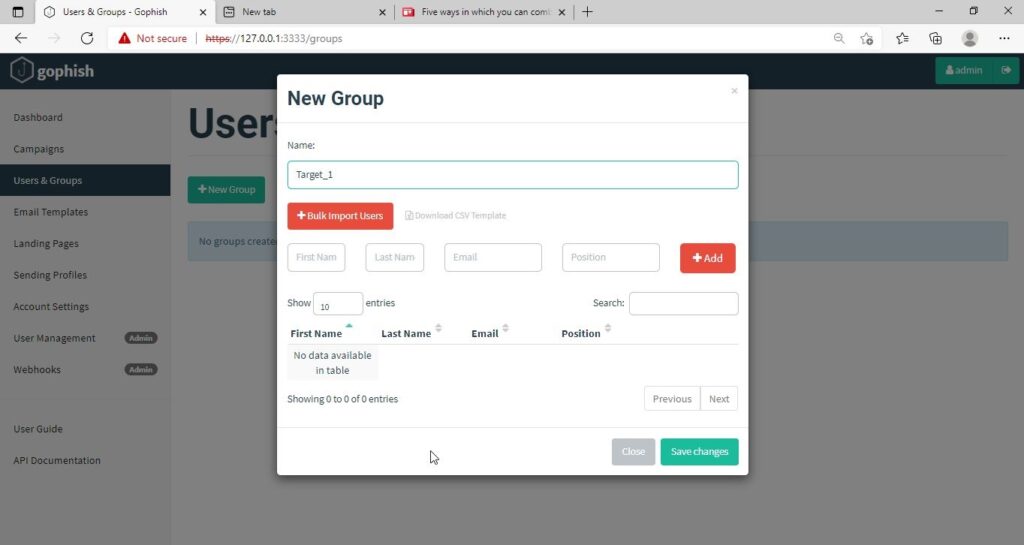
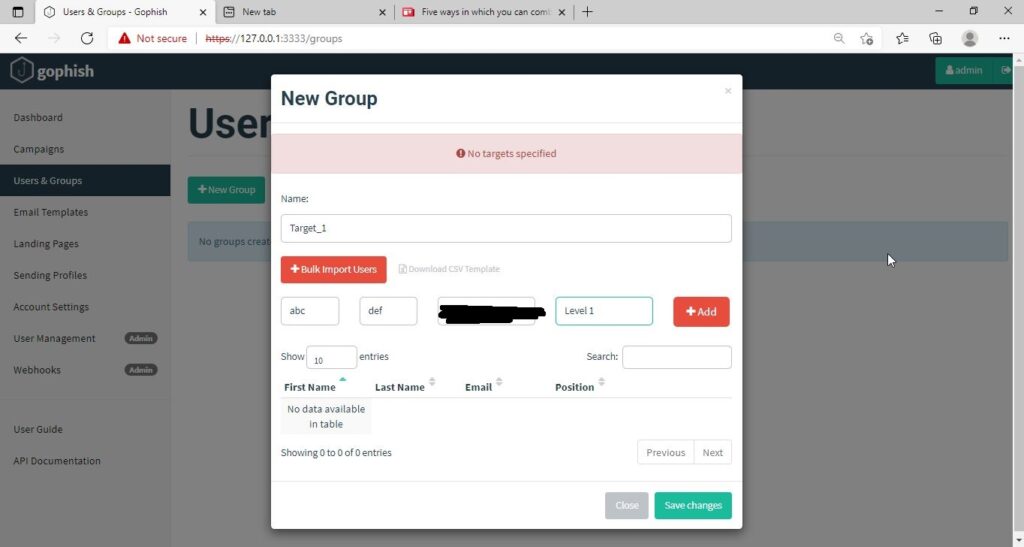
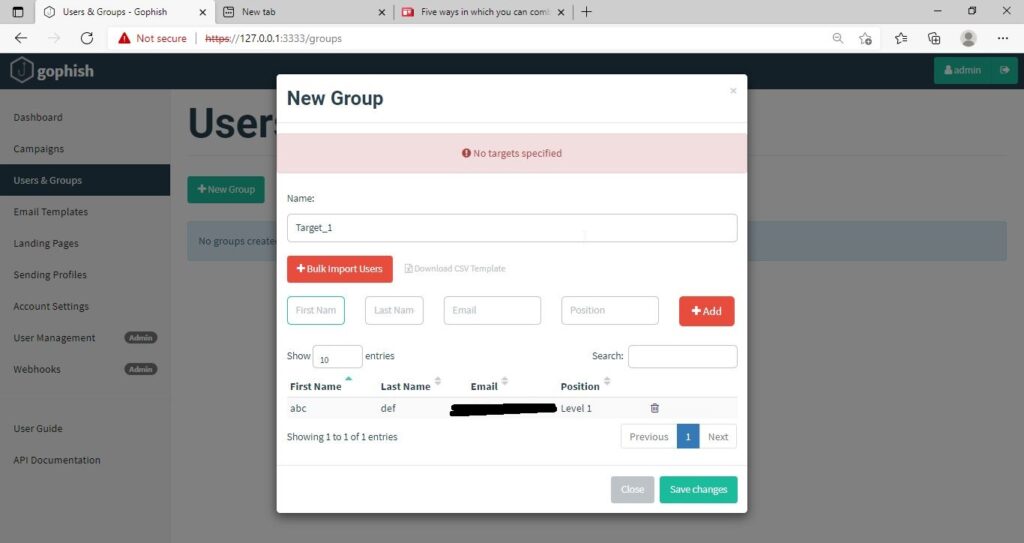
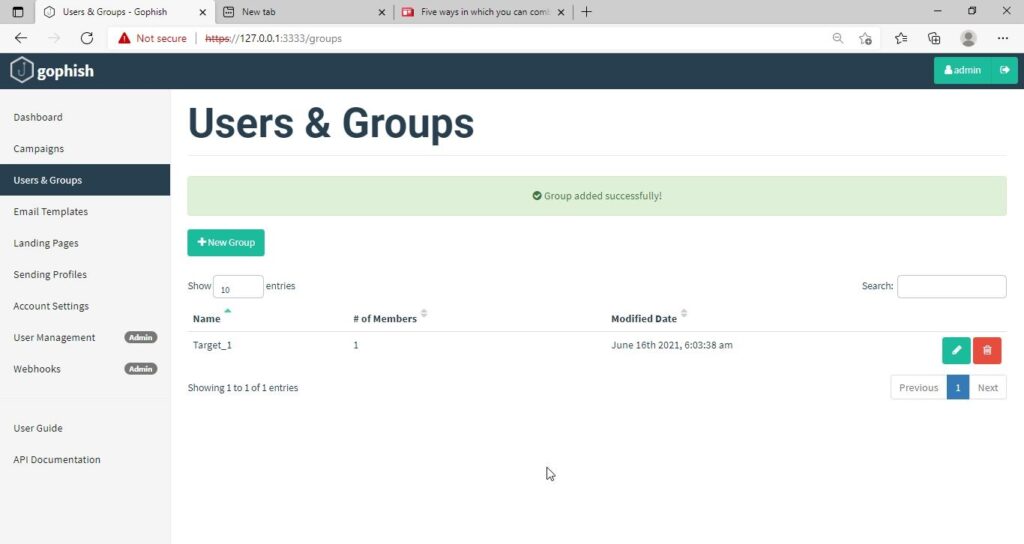
Click on “New Group” to create a new batch of recipients. I have named this group as Target_ 1.
For this tutorial, I’ll add only a single recipient.
If you want to add a large number of users, you can save them in a CSV file and just import those users with the “bulk import users option”.
It’s time to create an email template. This is the most important part of a phishing email since it has the email body that convinces a victim to click or take any other action.
But before we compose the spear phishing email, let’s create a phishing webpage. For this tutorial, we will be capturing some credentials. Hence we will be using a fake website created using Social Engineering Toolkit in Kali Linux. We can also create a phishing website with Weeman HTTP Server.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
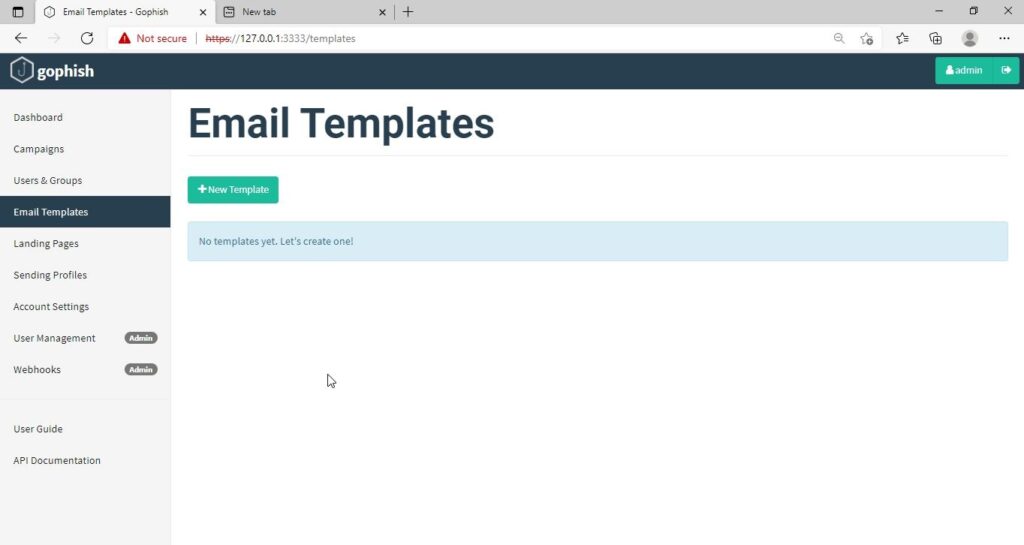
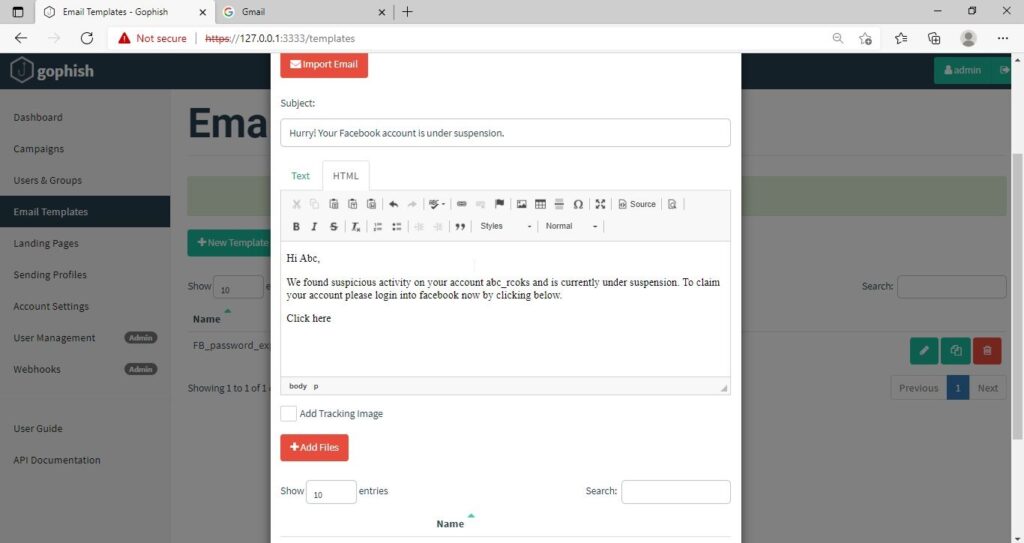
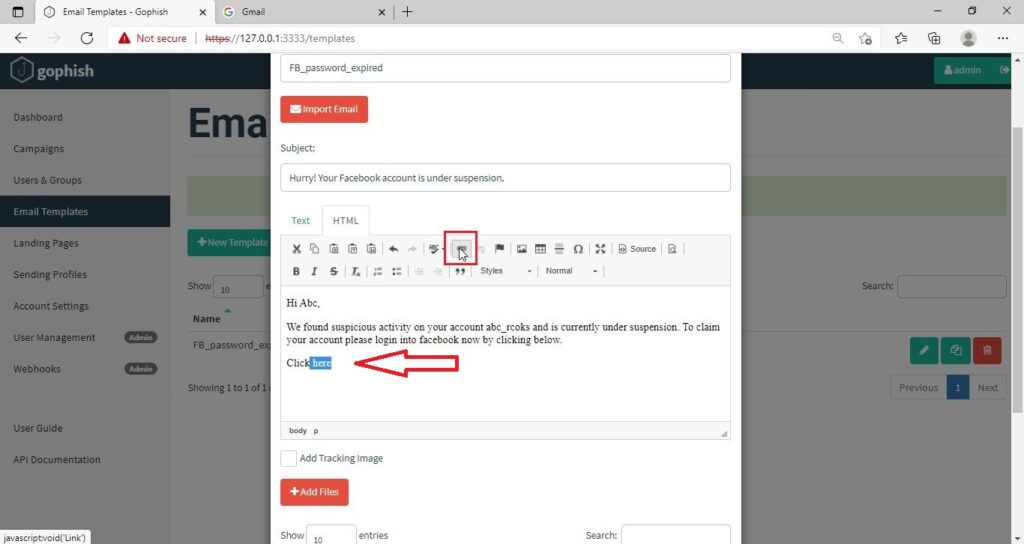
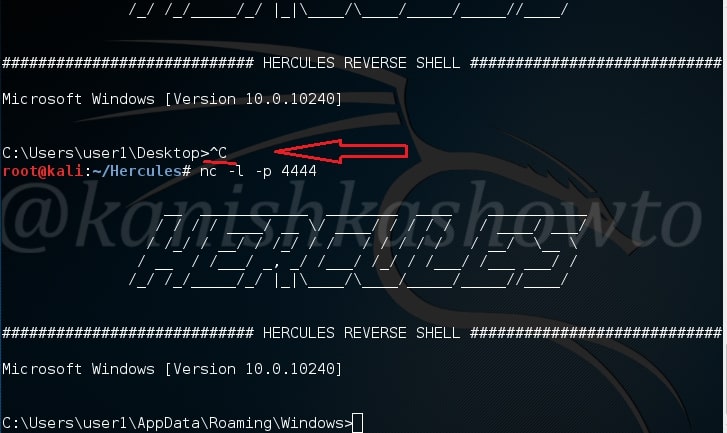
The phishing site is ready and will display any captured credentials on this terminal. Go back to GoPhish. Click on “New Template” to create a new email.
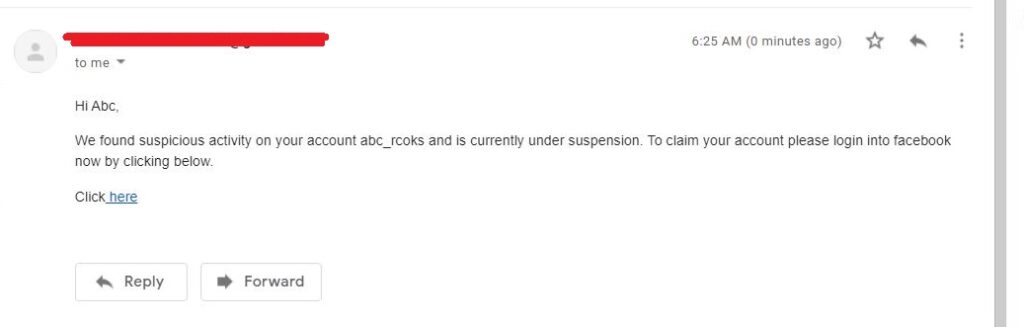
Remember what I said. This part is the most important and the content of the email should convince the user take whatever action you want him to take. We are just showing the age-old account suspension mail. Let’s have a look at some of the spear phishing emails used in real world hacking attacks.
The above mail was sent to Godaddy customers. The Logo, Customer support number etc almost convince even me but just look at the Sender Email. The domain of Godaddy is godaddy.com but sender email is really phishy.
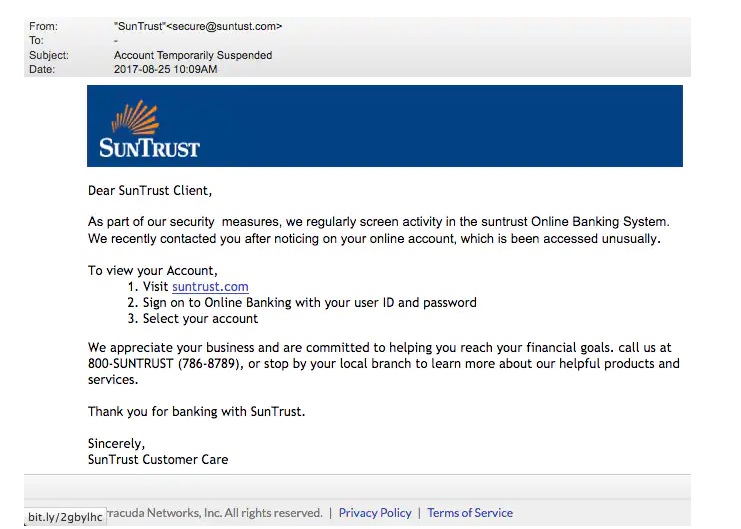
This above phishing email is a must read. Everything looks so convincing. Even I think I have a account at Suntrust. Only when we hover over the link that we can see it is suspicious.
The above mail is directed towards Instagram users. Although sender email is phishy, have a look at the message of the mail. It says your Instagram password has been changed and if it is not you that changed the password, you are asked to click on the link they have provided to reset your password. It even provides a link to the Instagram Help Center to appear trustworthy.
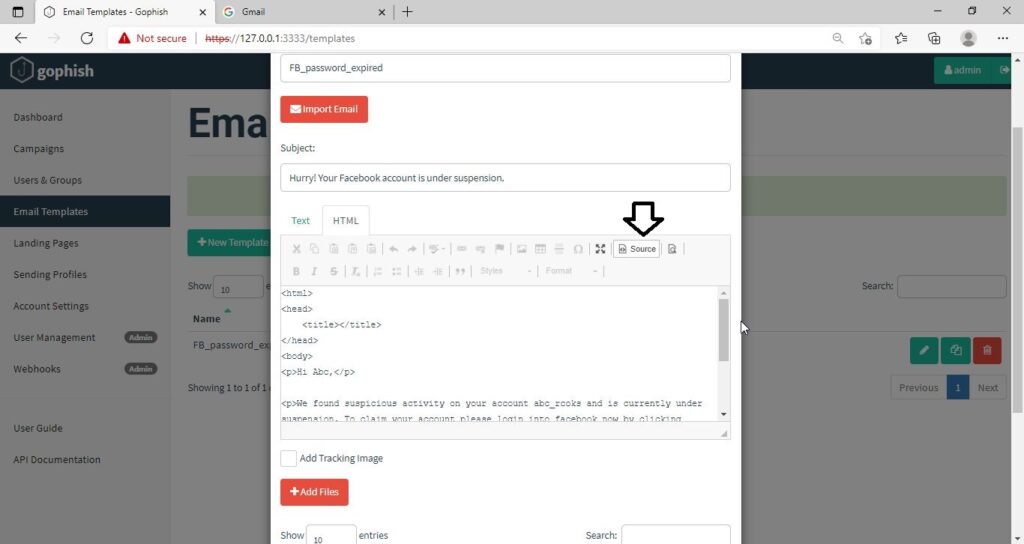
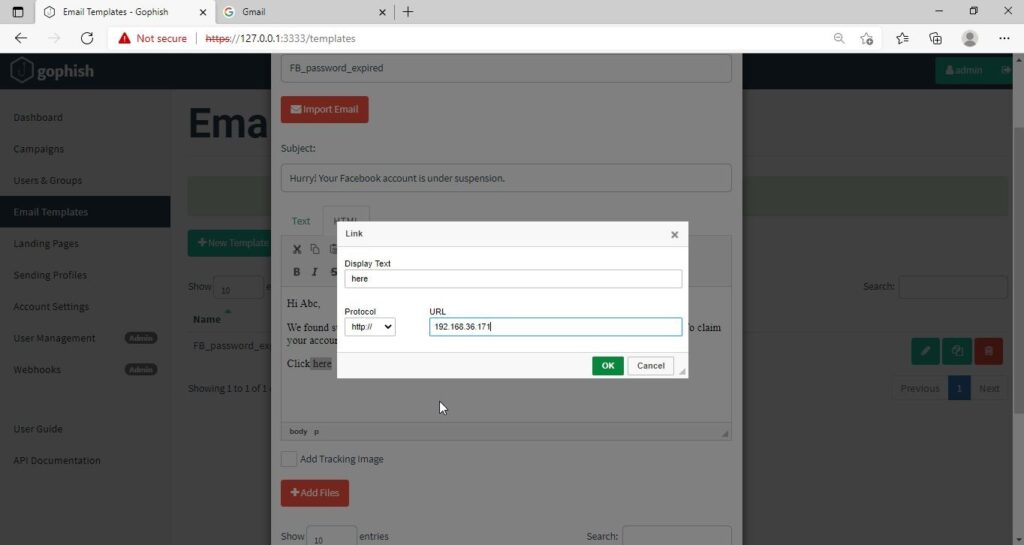
I am sure readers got an idea about how phishing emails look like. If you find an email suspicious, just hover over the links instead of clicking on them. Once, the body of the email is complete, let’s add a hyperlink to the email content. Click on “source”.
I want the users to be redirected to my Kali Linux attacker machine.
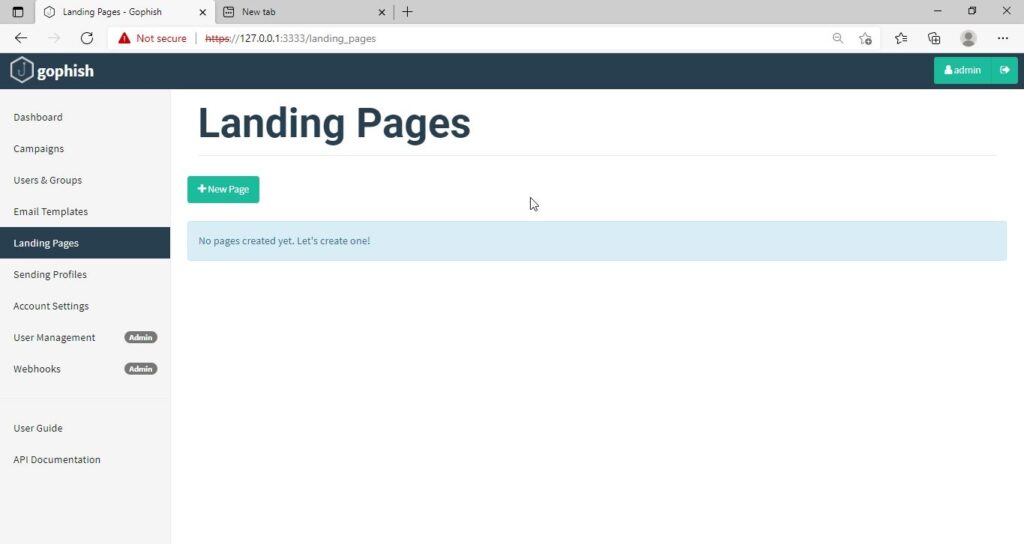
The Email template is ready. It’s time to set the landing page. Landing page in Gophish is the page where users will be redirected to after clicking a link in the phishing email we sent.
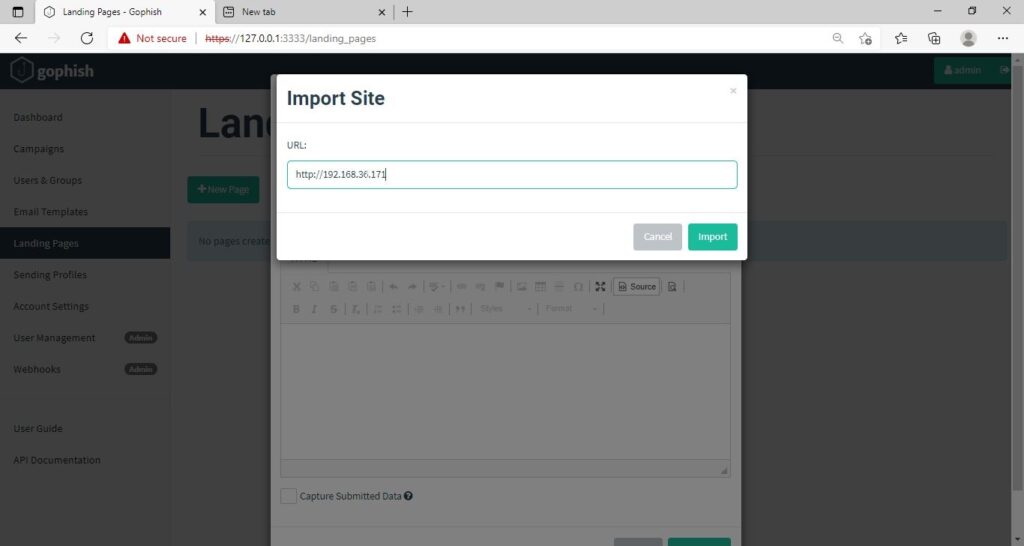
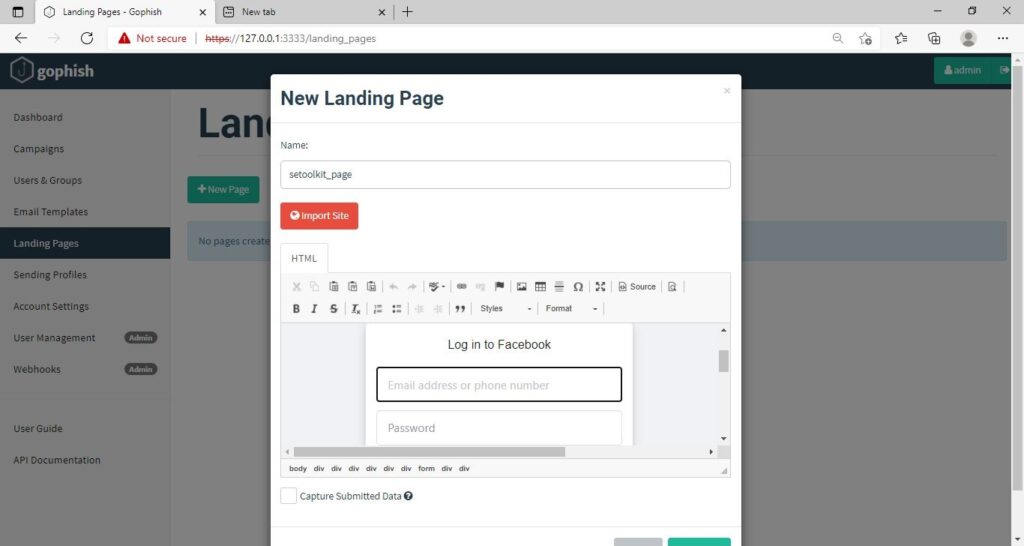
Click on “New Page”. You can create a new landing page or you can import an already created landing page. Let me import the phishing site I created in SE Toolkit on Kali Linux.
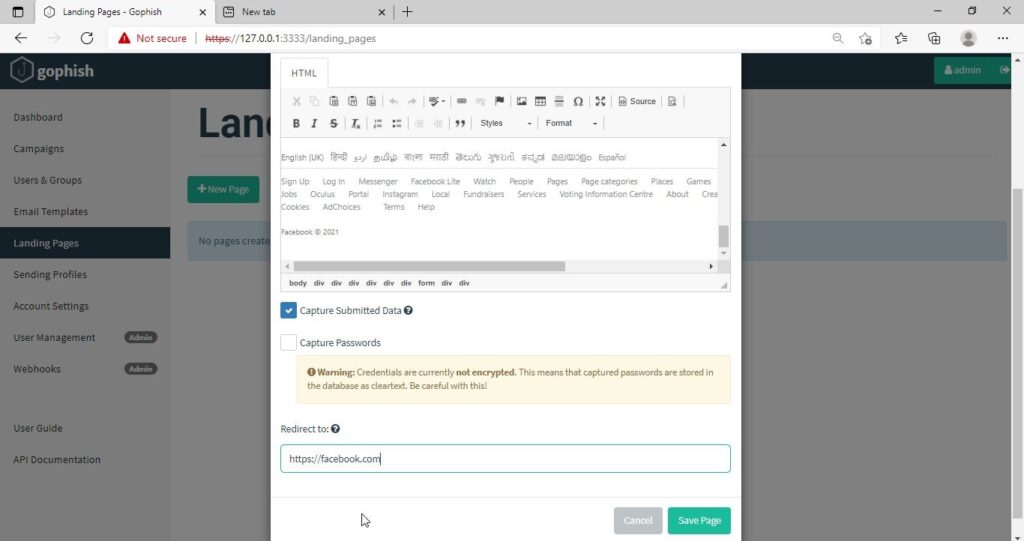
After capturing credentials, just like any phishing page, we can redirect the users to another webpage after capturing credentials. I want the victims to be redirected to the genuine site of Facebook.
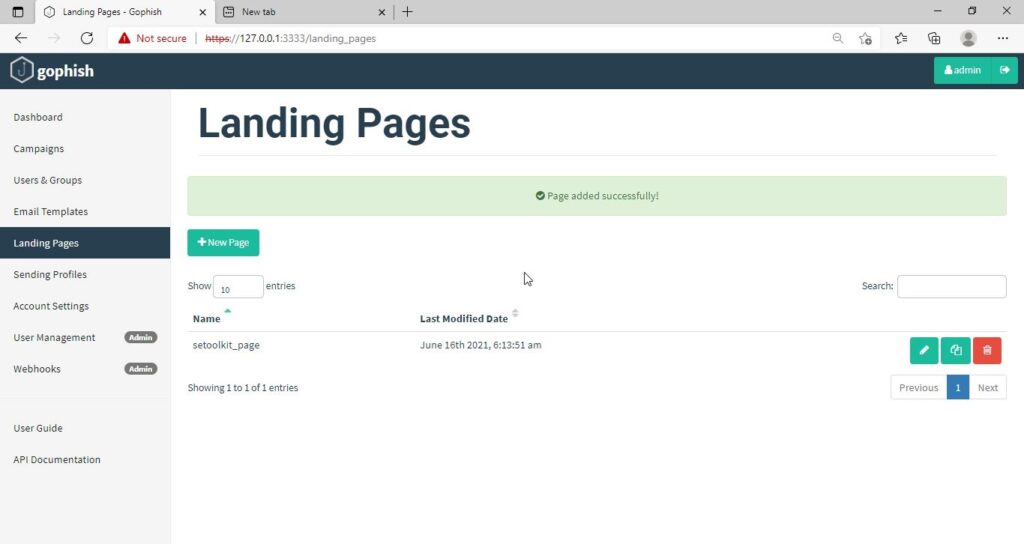
Save the landing page.
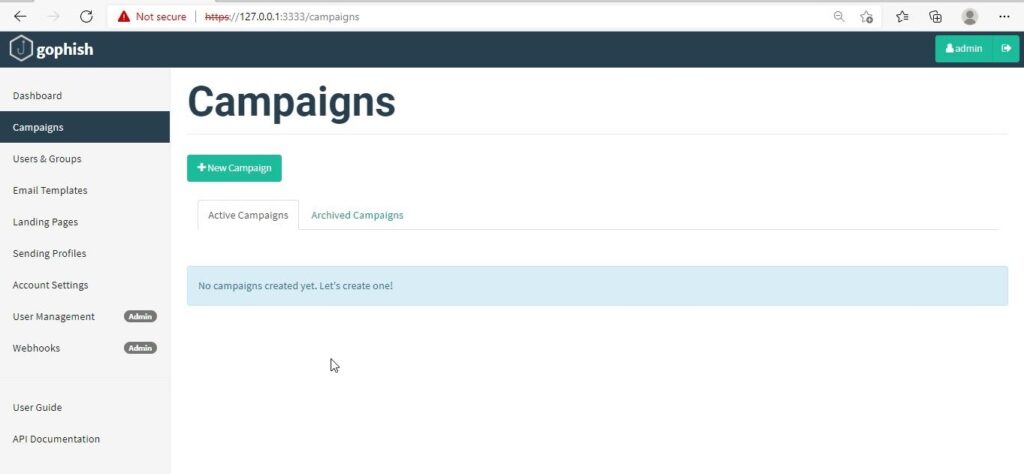
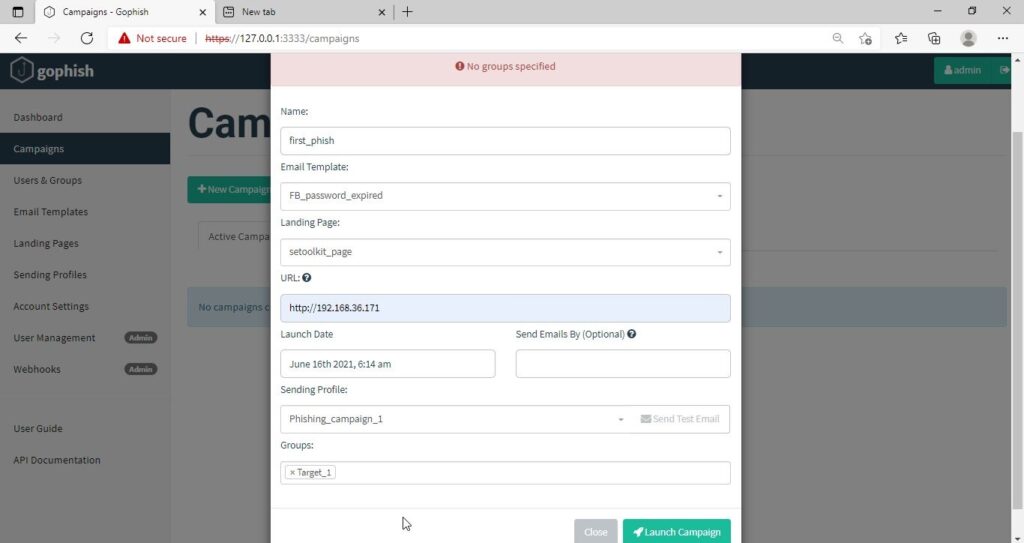
Everything is ready. It’s time to start the phishing campaign. Go to campaigns and click on “New Campaign”.
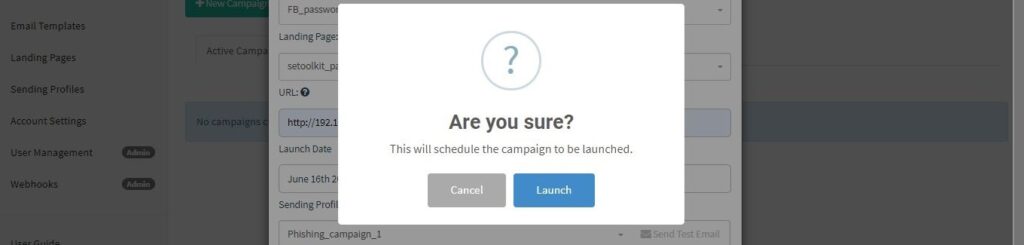
Specify all the options like URl, the recipients etc and click on “Launch campaign”. You can set the date and timing for the phishing campaign.
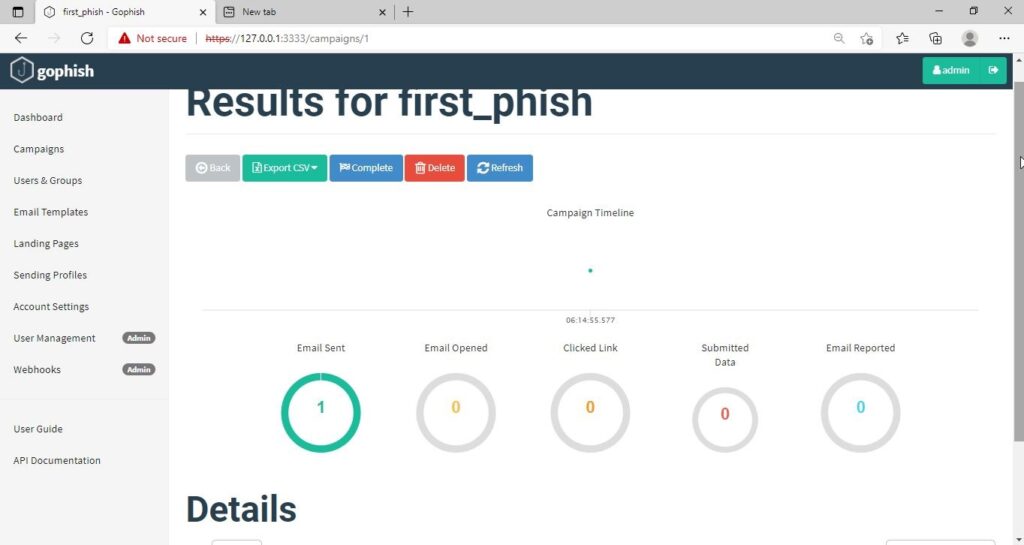
In the dashboard you can view result of the campaign. You can see how many users read your email and how many fell victim to your phishing campaign.
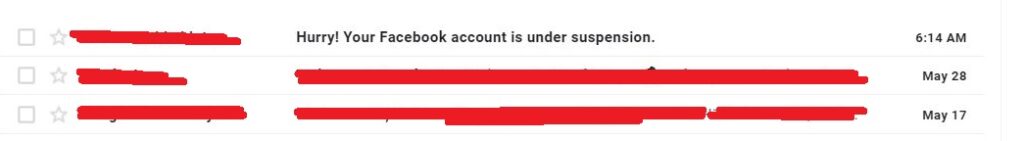
This is how the spear phishing email I created looks in the Inbox of our target user.
Here is how the content of the email looks.
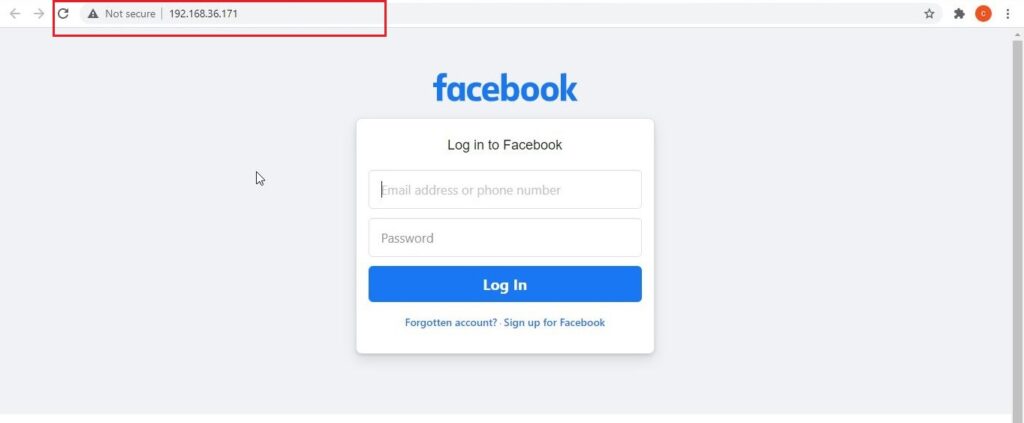
Here is the phishing page the user is directed to once he clicks on the link.
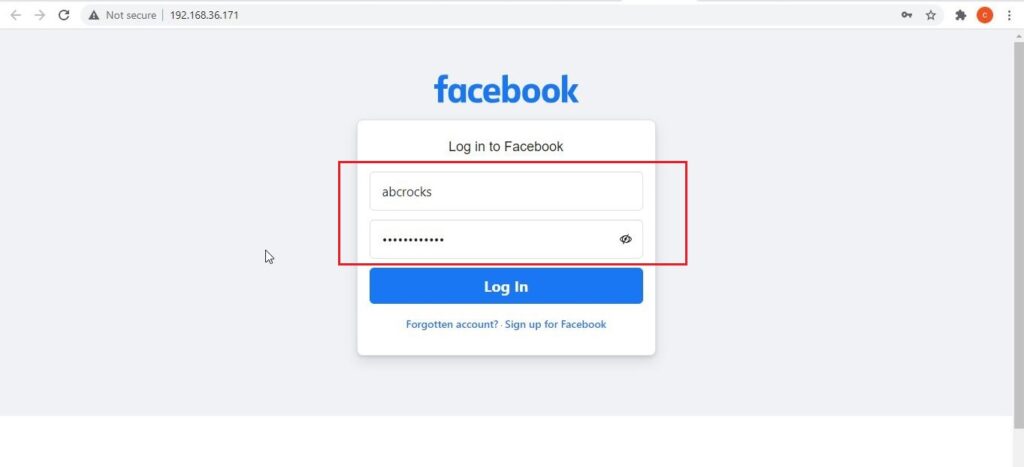
Once the victim fails to notice the signs of a phishing email, he enters his credentials.
These credentials are captured in SETOOLKIT as shown below.
Credentials are captured and our phishing campaign is successful. This is how a successful campaign is run.
Conclusion
GoPhish is commonly used in:
- Security awareness programs
- Red team training
- Blue team detection testing
- SOC readiness exercises
- Ethical hacking labs
For beginners, it builds a strong foundation in human-focused attack techniques, which are often more effective than technical exploits. GoPhish shows that modern cybersecurity isn’t just about firewalls and exploits. It’s about understanding human behavior. By simulating phishing attacks ethically, organizations can reduce real-world risk and improve user awareness. For students and beginners, GoPhish offers a hands-on, responsible way to learn how phishing works and how it can be stopped.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply