Hello, aspiring ethical hackers. In our previous blogpost, you have learnt about Blue Teaming. In this article, you will learn about TheHive, a platform that helps manage security incidents the smart way. When learning cybersecurity, many beginners focus on tools that detect threats—alerts, logs and suspicious activity. But detection is only the beginning. Once an alert fires, security teams still need to track, investigate, collaborate and document what happens next. This is where TheHive becomes important.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
TheHive is a security incident response platform designed to help teams manage investigations in an organized, repeatable and collaborative way. For beginners, it provides a structured introduction to how real-world security operations centers (SOCs) handle incidents.
What Is TheHive?
TheHive is an open-source Security Incident Response Platform (SIRP) used by SOCs and DFIR teams to manage security alerts and incidents. Instead of relying on spreadsheets, emails or chat messages, teams use TheHive to centralize investigations in one place.
TheHive was developed by TheHive Project and is widely adopted by blue teams because it focuses on workflow, collaboration and documentation, not just tools.
In simple terms, TheHive answers the question:
“How do we handle security incidents in an organized and consistent way?”
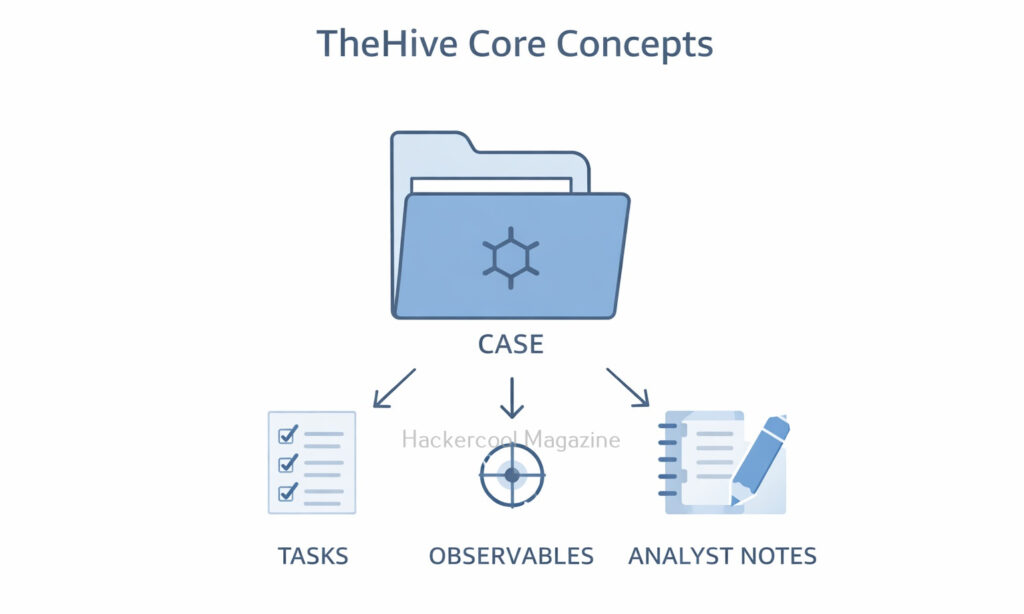
Core Concepts of TheHive
If you want to learn about TheHive, you should begin with understanding a few key concepts which make it much easier to learn.
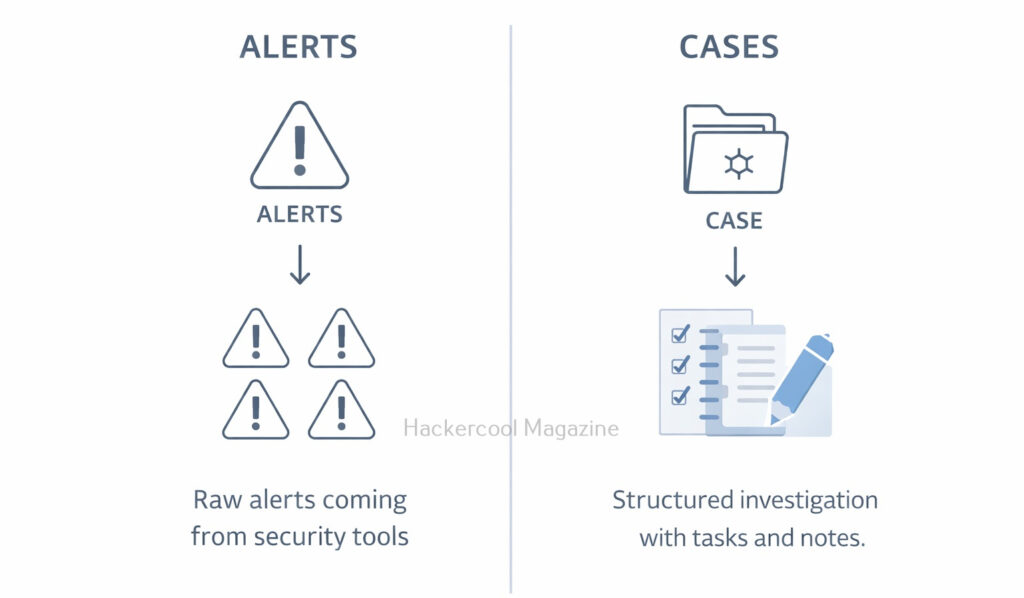
Alerts:
Alerts are raw security signals coming from other tools, such as SIEMs, EDR platforms or scripts. Alerts may indicate suspicious activity, but they are not yet confirmed incidents.
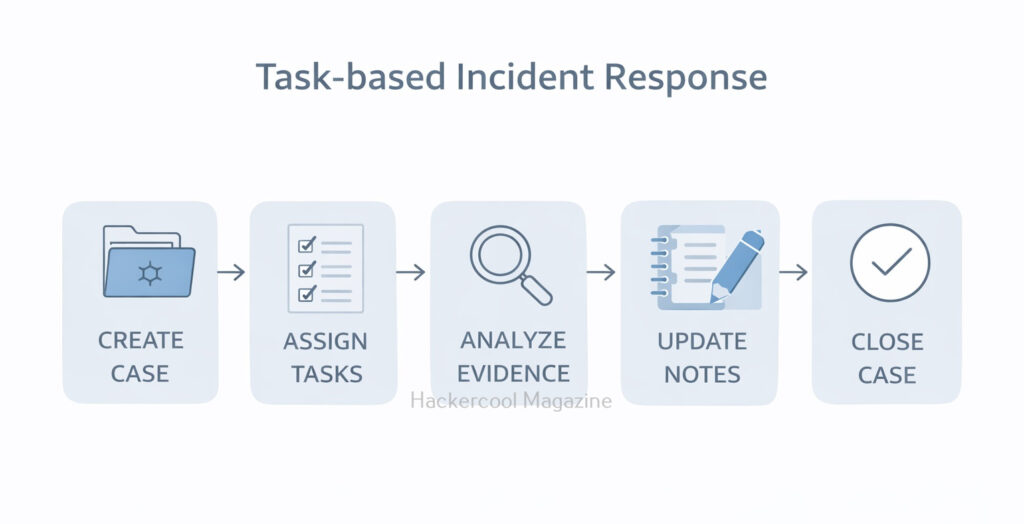
Cases:
A case is created when an alert is worth investigating. A case represents an incident under investigation and contains all related information, tasks and evidence.
Tasks:
Tasks break an investigation into actionable steps, such as:
- Review logs
- Analyzing an IP address
- Collect endpoint data
- Write a summary
Observables:
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Observables are pieces of data related to an incident, such as:
- IP addresses
- Domains
- File hashes
- Email addresses
How TheHive Fits into a SOC Workflow
TheHive is not a detection tool. It sits after detection in the security workflow. A simplified SOC workflow looks like this:
- A security tool generates an alert
- The alert is sent to TheHive
- An analyst reviews the alert
- A case is created if investigation is needed
- Tasks are assigned and completed
- Findings are documented and closed
For beginners, this provides a clear picture of how alerts turn into real investigations.
Collaboration and Case Management
One of TheHive’s biggest strengths is its collaboration. Using TheHive, multiple analysts can:
- Work on the same case
- Add notes and evidence
- Assign tasks to each other
- Track progress in real time
This reflects how real SOCs operate.
TheHive Compared to Other Security Tools
Beginners sometimes confuse TheHive with tools like SIEMs or forensic frameworks. However, there is lot of difference between them.
- SIEMs focus on collecting and correlating logs
- EDR tools focus on endpoint detection and response
- Forensic tools focus on deep technical analysis
- Whereas TheHive focuses on managing the investigation process
TheHive does not replace all the above other tools but it connects them together through workflow.
Why Beginners Should Learn TheHive?
Beginners often learn tools like scanners, SIEMs or forensic utilities, but struggle to understand how investigations are actually managed. TheHive fills this gap by teaching:
- How alerts become investigations
- How tasks are assigned and tracked
- How evidence and notes are documented
- How multiple people collaborate on the same incident
Learning TheHive helps beginners think like SOC analysts, not just tool operators.
Challenges Beginners May Face
Like any platform, TheHive has a learning curve. Beginners may find:
- Case workflows unfamiliar at first
- The number of features overwhelming
- Integration concepts confusing
These challenges are normal. Beginners should focus on basic case creation, tasks and documentation before exploring automation or integrations.
Conclusion
TheHive teaches one of the most important cybersecurity lessons: handling incidents is as important as detecting them. For beginners, it provides a realistic view of how SOCs and DFIR teams organize investigations, collaborate and learn from incidents.
By learning TheHive early, beginners build strong foundations in incident response thinking—skills that remain valuable regardless of which tools or technologies they use in the future.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply






That’s a really helpful overview. It’s great to see how TheHive builds on detection by offering a more complete incident management process.