Hello, aspiring ethical hackers. In our previous blogpost, you learnt in detail about cybersecurity. In this article, we will give you cybersecurity learning roadmap for beginners for year 2026. Starting cybersecurity can feel overwhelming. You hear terms like hacking, networking, malware, cloud security and it all feels like too much.
But here’s the truth:
- You don’t need to learn everything at once.
- You just need a clear roadmap.
This guide gives you a step-by-step cybersecurity learning roadmap for beginners like you so you know exactly what to learn, in what order and how to progress.
New to Ethical Hacking?
Start your journey with The Beginner Ethical Hacker Starter Kit (2026 Edition).
Inside the free guide, you’ll learn:.
- Ethical hacking fundamentals
- Beginner cybersecurity roadmap
- Essential hacking tools
- Common vulnerabilities explained
What Is Cybersecurity?
Let’s beging with what exactly is cybersecurity so that you and I are on the same plane. Cybersecurity is the practice of protecting systems, networks and data from cyber attacks. It includes:
- Preventing attacks
- Detecting threats
- and responding to incidents
In simple terms: ity is keeping digital systems safe.
Why Learn Cybersecurity in 2026?
Cybersecurity is one of the fastest-growing fields globally. There are multiple reasons for it. Some of them are,
1. High Demand & Salaries:
Due to increasing and constantly evolving cyberthreats, cybersecurity learning professionals are in demand. Due to this demand, even entry level profesiionals are being paid handsome salaries.
2. Remote Opportunities:
Unlike many other jobs, you can work from anywhere in the world or participate in bug bounties around the world.
3. Challenging & Rewarding:
As already mentioned above, cyber threats constantly evolve. That means, every new day brings new problems to solve.
Now that you have understood what cyberecurity is and why you should learn it in 2026, let’s begin with the roadmap.
Step 1: Build Strong Foundations (Month 1–2)
You know what many beginners do when they decide to start learning Cybersecurity. They jump straight into different tools. That’s a mistake. Before doing anything else, you need to understand how systems work. So to begin,
1. Learn Networking Basics:
Focus on:
- IP addresses
- Subnets
- DNS
- HTTP/HTTPS
- TCP/UDP
Why? because Networking is the backbone of cybersecurity.
2. Learn Operating Systems:
Start with:
- Linux (very important)
- Windows basics
Learn:
- Command line
- File systems
- Permissions
3. Understand How the Internet Works:
Learn the working of:
- Client-server model
- Requests & responses
- Web architecture
Without this foundation, nothing else will make sense.
Step 2: Learn Core Security Concepts (Month 2–3)
Once you understood about systems and networks, move to basics of cybersecurity.
CIA Triad:
Learn what is CIA triad and understand in detail about:
- Passwords
- Multi-factor authentication
- Access Control
This is the main foundation of all cybersecurity.
Authentication & Authorization:
Learn about,
- Confidentiality
- Integrity
- Availability
Common Threats:
Learn about the most common threats like,
- Phishing
- Malware
- Ransomware and
- Social engineering
This helps you understand how attacks actually happen in real-world.
Step 3: Start Hands-On Practice (Month 3–4)
You can’t master cybersecurity by just studying theory. You need hands-on practice to do that. That said, never and never practice on real-world systems. Alwyas, create a safe lab environment.
What You Need:
- A laptop (8GB+ RAM recommended)
- Virtualization software (VirtualBox / VMware)
- Kali Linux
Targets for Practice:
- Intentionally Vulnerable machines like Metasploitable.
- Capture-the-flag platforms
Don’t just watch tutorials—practice actively.
Step 4: Learn Essential Tools (Month 4–6)
Now, hacking tools will make a lot of sense. Start using tools but with understanding.
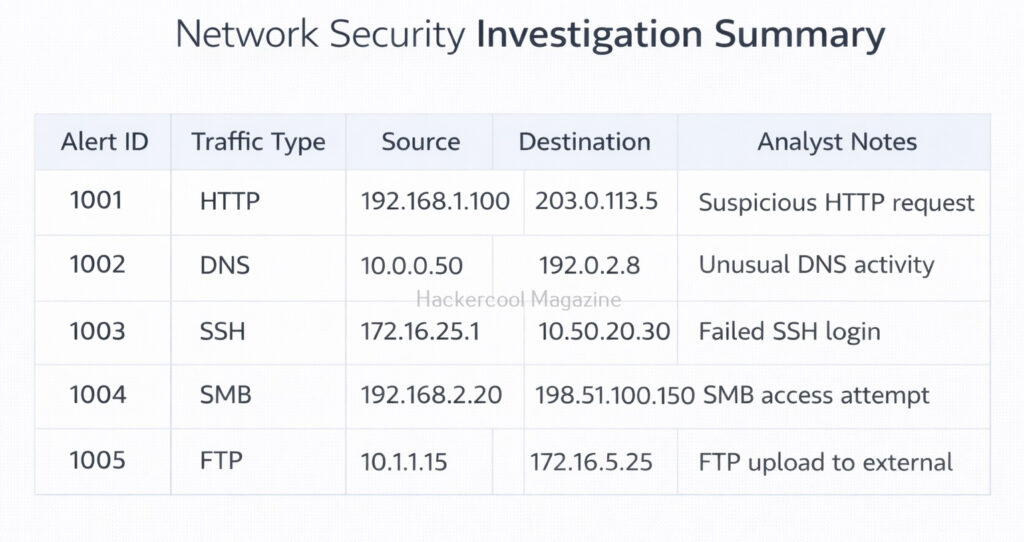
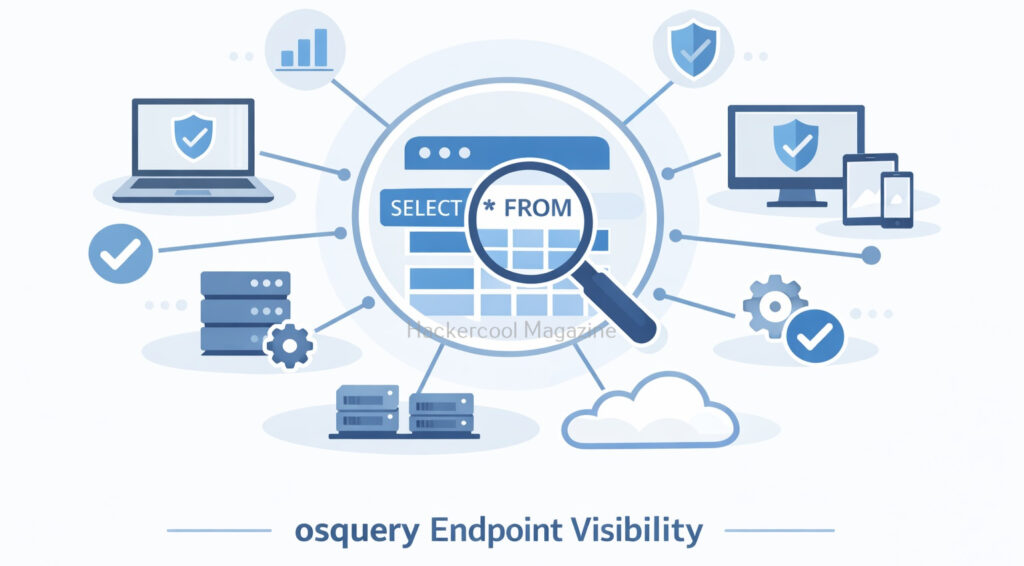
Basic Tool Categories:
- Network scanning
- Web testing
- Password testing
- System analysis
Focus on:
- What the tool does
- Why it works
Not just how to run it.
Want to Learn Ethical Hacking Step-by-Step?
If you’re serious about learning cybersecurity, a structured roadmap makes the journey much easier.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and discover:
✔ The ethical hacking learning path
✔ Beginner-friendly security concepts
✔ Essential tools ethical hackers use
✔ The most common vulnerabilities explained
Step 5: Understand Attack & Defense (Month 5–7)
Now connect everything you learnt together.
Offensive Security (Hacking Basics):
Learn about:
- Reconnaissance
- Scanning
- Exploitation
- Privilege escalation
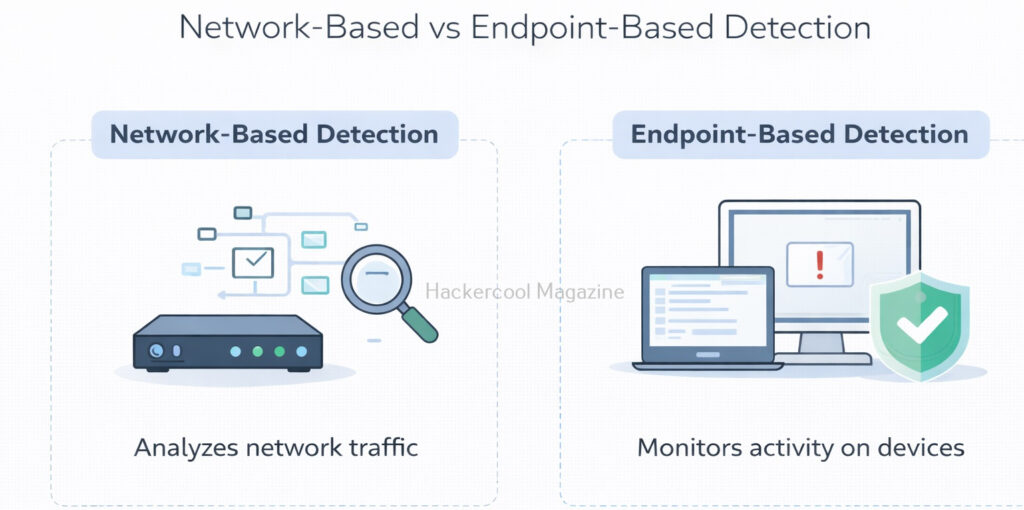
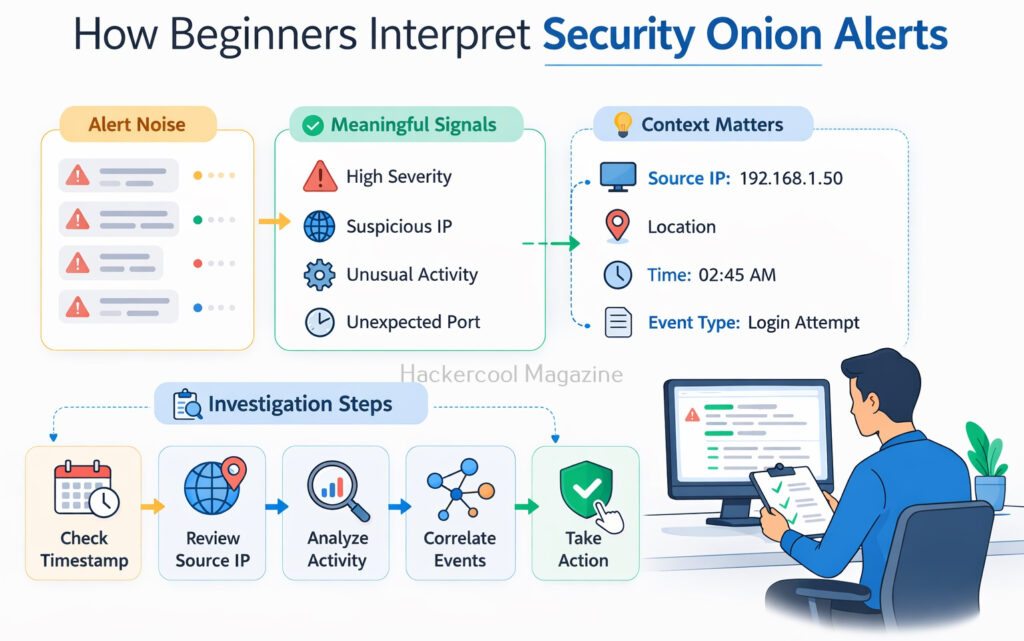
Defensive Security:
Learn:
- Monitoring systems
- Detecting threats
- Responding to attacks
A good cybersecurity professional should understand both sides.
Step 6: Choose a Specialization (After 6 Months)
Cybersecurity is huge. After 6 months, you must choose a preferred path. Here are some of the paths you can take.
Ethical Hacking / Penetration Testing:
You should choose this path if you like:
- Finding vulnerabilities
- Simulating attacks
Security Analyst (Blue Team):
Involves:
- Monitoring systems
- Detecting threats
Cloud Security:
Securing AWS, Azure and other cloud apps
Investigating cyber incidents.
Remember one important thing. Always choose your path on what you are interested in.
A Simple 6-Month Learning Plan
Here’s a simple 6-month Learning plan to master cybersecurity easily.
Month 1-2:
- Networking
- Linux basics
Month 3:
Security concepts
Month 4:
Lab setup + practice
Month 5-6:
Tools + real scenarios
After this, you’ll have a strong foundation.
Common Mistakes Beginners Make (Avoid These)
Here are some of the most common mistakes almost all beginners make while learning cybersecurity. Please try to avoid making these mistakes.
Tool overload:
Too many tools = confusion. Trust me, even if you do this successfully, you’ll become a “script kiddie” with no real skills.
Skipping basics:
You may think by skipping basics you will go faster but this will slow you down later.
Watching tutorials without doing any practice:
Passive learning doesn’t work here. What may work in a tutorial may not work in practice.
Giving up too early:
Cybersecurity has a steep learning curve so prepare for long haul to master it properly.
How to Learn Faster (Pro Tips)?
Here are some tips to accelerate your learning and practice like a real hacker.
Think Like an Attacker:
While learning, ask yourself questions like:
- What can go wrong here?
- Where is the weakest point?
Practice daily:
Even 1–2 hours of practice helps but you should practice daily.
Document Everything:
Keep notes of:
- Commands
- Techniques
- Mistakes
Repeat and Improve:
Repetition builds mastery.
Join Communities:
It helps you to learn from others.
Career Opportunities in Cybersecurity
Once you build your skills, you can choose one of the career paths in cybersecurity. Some of the careers you can take in cybersecurity are,
Penetration Tester:
A penetration tester simulates real-world attacks on systems and networks.
Security Analyst:
A Security Analyst is a person who monitors and defends systems.
Bug Bounty Hunter:
A Bug Bounty Hunter finds vulnerabilities and gets paid for reporting them responsibly.
SOC Analyst:
A SOC Analyst monitors, detects and responds to digital security threats.
Cloud Security Engineer:
Responsible for security of the Cloud.
Do You Need Certifications?
Certifications in cybersecurity can help in getting you a job but they’re not mandatory. Here are some of the certifications beginners can opt for.
- Basic cybersecurity certifications
- Practical hacking certifications
But remember: Skills matter more than certificates.
Legal & Ethical Responsibility
In your cybersecurity journey, always remember. Never:
- Hack systems without permission
- Access unauthorized data
Always:
- Practice in legal environments
- Follow ethical guidelines
How Long Does It Take?
Many people ask how long does it take to learn ethical hacking. Realistically speaking:
- 3 months → Basic understanding
- 6 months → Hands-on skills
- 12 months → Job-ready (if consistent)
Remember. Consistency is key.
Conclusion
Cybersecurity is not about learning everything. It’s about learning the right things in the right order. Follow this roadmap:
- Build strong basics
- Practice consistently
- Stay patient
And you’ll go from beginner to skilled professional.
Start Your Ethical Hacking Journey Today
Learning cybersecurity can feel overwhelming at first. The best way to start is with a clear roadmap and the right resources.
Download The Beginner Ethical Hacker Starter Kit (2026 Edition) and get instant access to:
✔ Ethical hacking fundamentals
✔ A beginner cybersecurity learning roadmap
✔ Essential hacking tools every beginner should know
✔ Common vulnerabilities explained simply